Infosec Europe 2025: we're live at the show, and here's everything we've seen
We're live at Infosecurity Europe 2025 - here's what we've seen so far.

Hello and welcome to our coverage of InfoSecurity Europe 2025!
Held at London's Excel center, Infosec 2025 (as everyone actually calls it) is one of the biggest security-focused events on the calendar, packed with big names, informative talks, and news from the biggest firms around.
We're here in London and live on the ground for Infosec 2025 - here's what we've seen so far!
Good morning from InfoSecurity Europe 2025! We're here at the Excel, and off to collect our badge before heading in.
Despite it being June, it's a cloudy and blustery day here - let's hope things are warmer inside...
We're heading in to the show now!
As you can see from our pictures, the theme of Infosec 2025 is "Building a Safer Cyber World" - something you can bet we'll hear more about over the next few days.

We're now seated for a super packed keynote, plenty of people are standing - so this is clearly a popular one! We're about to hear from Graham Cluley, host of the Smashing Security Podcast who'll introduce us all to Infosec's 30th year!
There's a quick look back to how far cybersecurity has come in the last 30 years before Cluley explains that hackers aren't girlfriend-less men in garages anymore (his words!), but are serious, state sponsored actors - outlining an almost unrecognisable evolution in that InfoSec has helped to guide security experts through.
Now, we're listening to Professor Brian Cox who's talking us through the link between cosmology and cybersecurity and computing. General relativity, the theory of space and time, and cosmology all link closely to quantum computing - with complex mathematics, data sets, and quantum mechanics.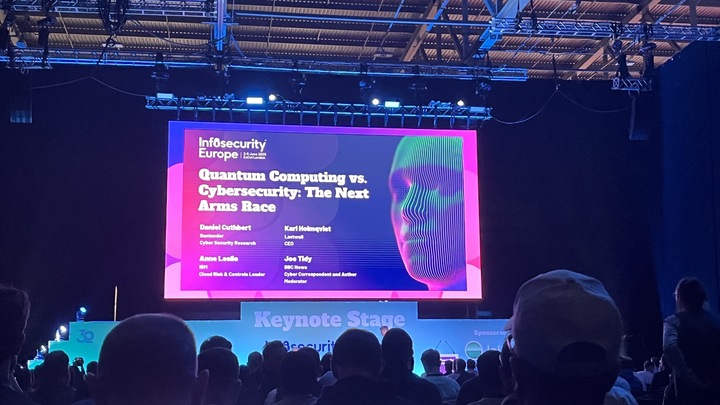
Next, it's 'Quantum computing v Cybersecurity' - chaired by BBC News' Joe Tidy. Here, cybersecurity is described as an 'Arms Race' - although not everyone think that terminology is helpful!
There's a myth, panel expert and Lastwall CEO Karl Holmqvist explains, that quantum computers can break any encryption. But really, at the moment, quantum computers can decrypt several commonly used encryptions - encryption will look different in the age of quantum, but it could still be effective. Cryptography will remain an important facet of cybersecurity for a long, long time - he argues.
"Harvest now, decrypt later" is a huge talking point. The industries most at risk (unsurprisingly) are the 'critical national' warns Daniel Cuthbert - panel participant and cybersecurity expert. That means healthcare, finance, and telecoms could face serious difficulties in a PQC (post-quantum cryptography) world.
Next up - we're listening to Paul Chichester and his take on the 'Cyber Cold War' and the geopolitics of cyber threats. Paul is the Director of Operations at the NCSC - so investigating cyber threats is his bread and butter.
As everyone knows, geopolitics is key to the cyber landscape. Cyber operations are now one of the go-to tools for covert state campaigns. Conflicts today are powered by cyber capabilities. Chichester points to the Viasat offensive in the Russian war in Ukraine as a prime example, and he explains that targeted attacks are increasingly disruptive, especially in the case of Russia, which are focusing on the logistical supply chain of materials into Ukraine.
Good cybersecurity has helped Ukraine, namely in the recent drone attack, which seemingly took Russia entirely by surprise. This shows the importance of great cybersecurity, Chichester argues. Defence, when done right, can be a vital weapon.
Beyond state sponsored attacks and espionage, states are using cyber capabilities for sabotage and coercion. Real world sabotage used cyber as a tool to inform operations. Volt Typhoon, Chichester points out, is a perfect example of how geopolitics threatens critical infrastructure. States are understanding that penetrating critical infrastructure will likely form the basis of conflict in the future.
So what's the takeaway? Well, it's that geopolitics should inform your cyber strategies as security team - so make sure to integrate this conversation into your risk management and global footprint landscapes.
Now, a little break from the keynote stage and on to exhibition floor for some showcases and introductions!
























































































































































![[The AI Show Episode 151]: Anthropic CEO: AI Will Destroy 50% of Entry-Level Jobs, Veo 3’s Scary Lifelike Videos, Meta Aims to Fully Automate Ads & Perplexity’s Burning Cash](https://www.marketingaiinstitute.com/hubfs/ep%20151%20cover.png)










































































































































































































.png?width=1920&height=1920&fit=bounds&quality=70&format=jpg&auto=webp#)

























































































































![Apple AI Launch in China Delayed Amid Approval Roadblocks and Trade Tensions [Report]](https://www.iclarified.com/images/news/97500/97500/97500-640.jpg)