Supercon 2024: Repurposing ESP32 Based Commercial Products
It’s easy to think of commercial products as black boxes, built with proprietary hardware that’s locked down from the factory. However, that’s not always the case. A great many companies …read more


It’s easy to think of commercial products as black boxes, built with proprietary hardware that’s locked down from the factory. However, that’s not always the case. A great many companies are now turning out commercial products that rely on the very same microcontrollers that hackers and makers use on the regular, making them far more accessible for the end user to peek inside and poke around a bit.
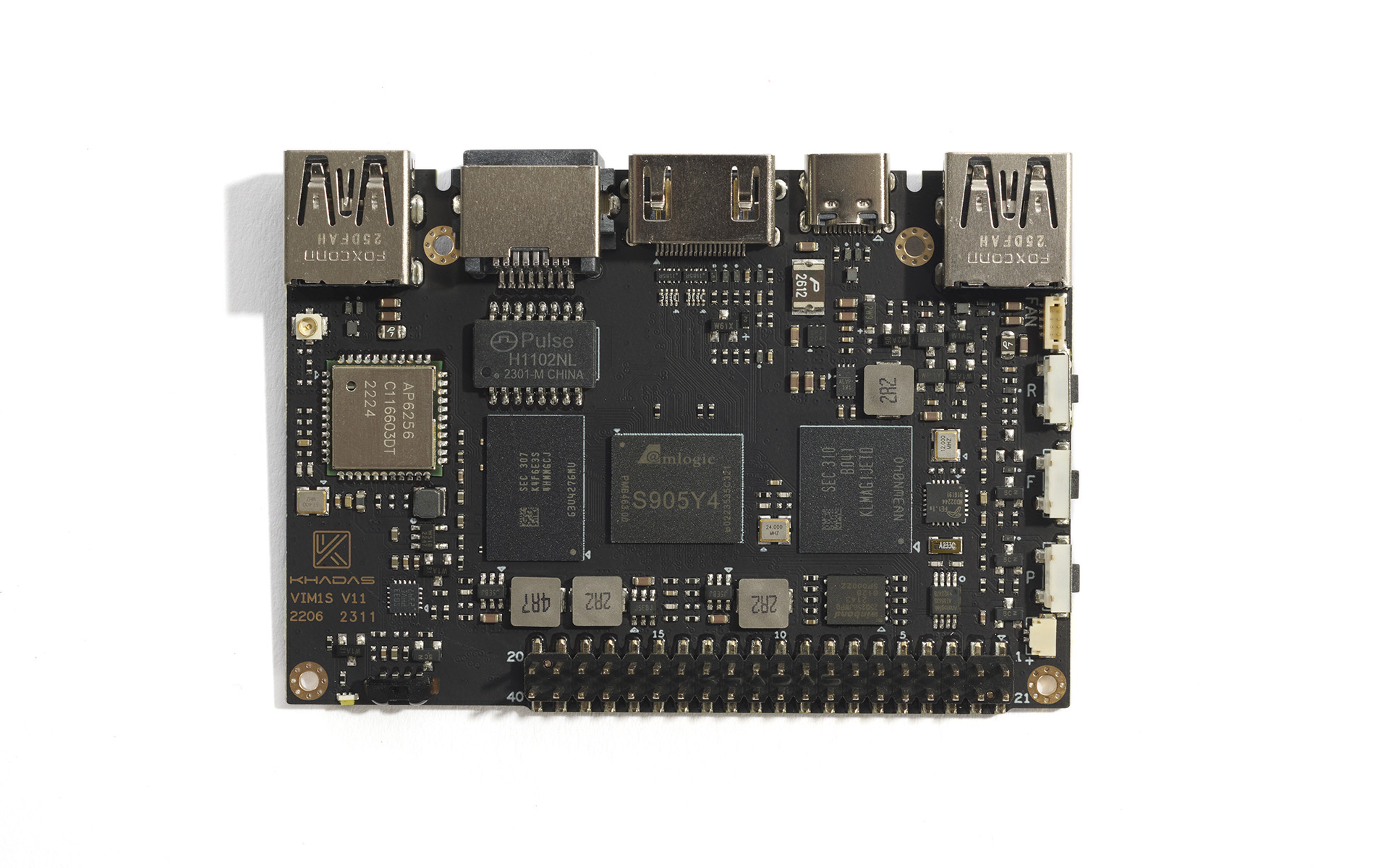
Jim Scarletta has been doing just that with a wide variety of off-the-shelf gear. He came down to the 2024 Hackaday Superconference to tell us all about how you can repurpose ESP32-based commercial products.
Drop It Like It’s Hot
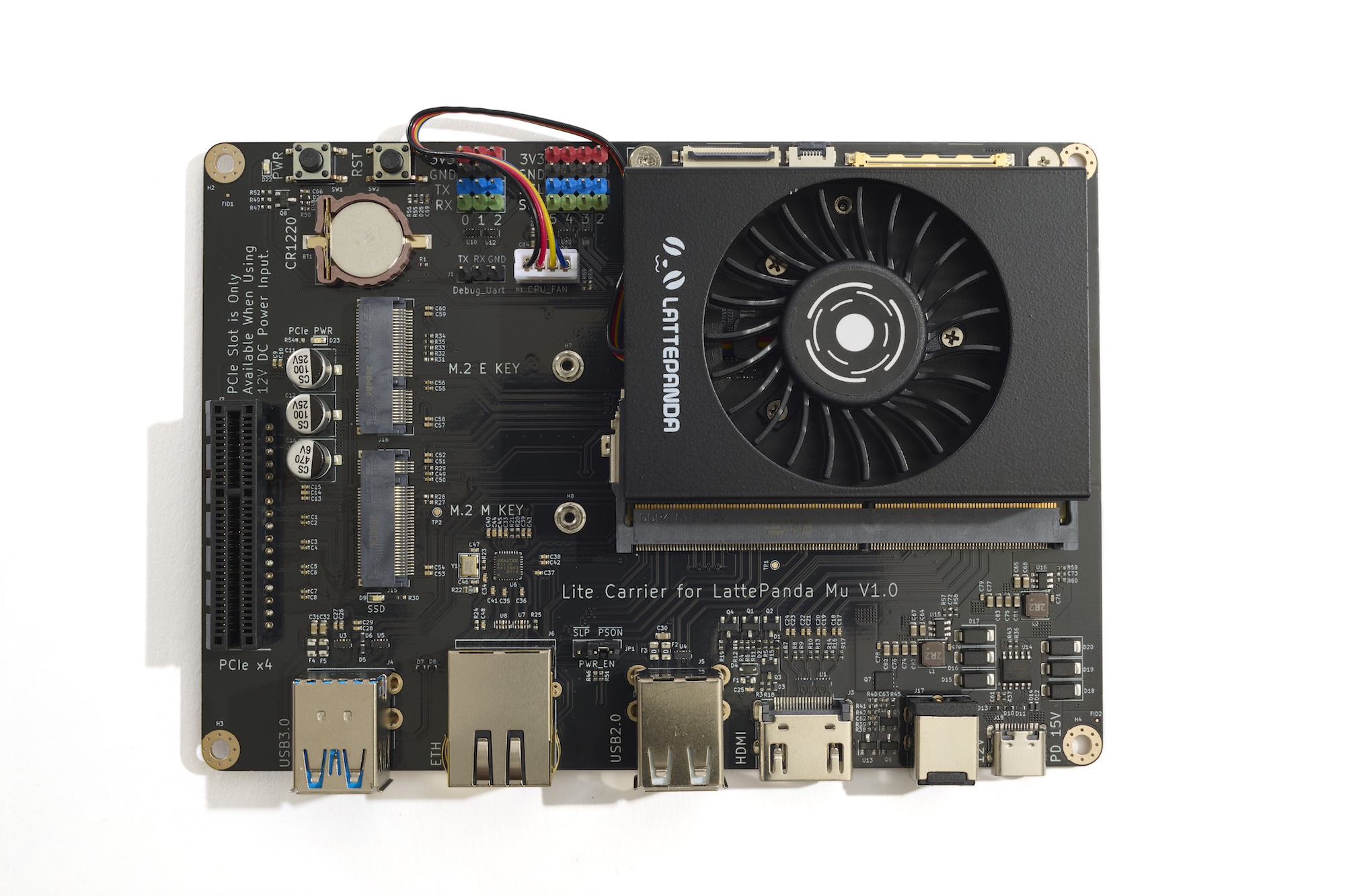
Jim starts off this talk by explaining just why the ESP32 is so popular. Long story short, it’s a powerful and highly capable microcontroller that can talk WiFi and Bluetooth out of the box and costs just a few bucks even in small quantities. That makes it the perfect platform for all kinds of modern hardware that might want to interact with smartphones, the Internet, or home networks at some point or other. It’s even got hardware accelerated cryptography built-in. It’s essentially a one-stop shop for building something connected.

You might ask why you’d want to repurpose a commercial product that has an ESP32 in it, when even fully-built devboards are relatively cheap. “It’s fun!” explains Jim. Beyond that, he notes there are other reasons, too.
You might like re-configuring a commercial product that doesn’t quite do what you want, or you might want to restore functionality to a device that has been deactivated or is no longer supported by its original manufacturer. You can even take a device with known security vulnerabilities and patch them or rebuild them with a firmware that isn’t so horridly dangerous.
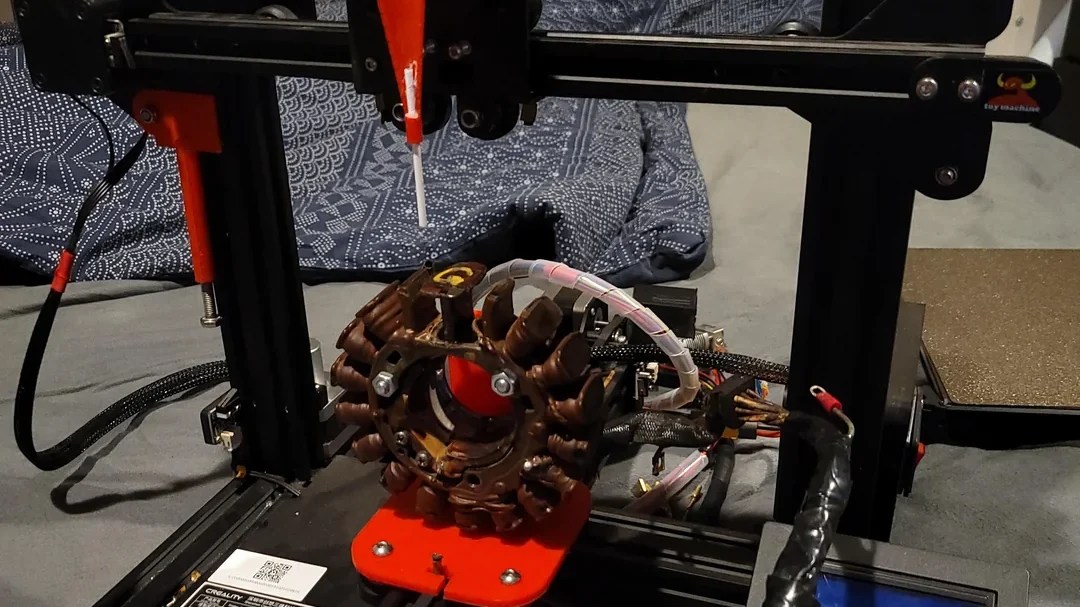
It’s also a great way to reuse hardware and stop it becoming e-waste. Commercial hardware often comes with great enclosures, knobs, buttons, and screens that are far nicer than what most of us can whip up in our home labs. Repurposing a commercial product to do something else can be a really neat way to build a polished project.
Jim then explains how best to pursue your goal of repurposing a commercial product based on the ESP32. He suggests starting with an ESP32 devboard to learn the platform and how it works. He also recommends researching the product’s specifications so you can figure out what it’s got and how it all works.
Once you’ve got into the thing, you can start experimenting to create your hacked prototype device, but there’s one more thing he reckons you should be thinking about. It’s important to have a security plan from the beginning. If you’re building a connected device, you need to make sure you’re not putting something vulnerable on your home network that could leave you exposed.
You also need to think about physical safety. A lot of ESP32 devices run on mains power—smart bulbs, appliances, and the like. You need to know what you’re doing and observe the proper safety precautions before you go tinkering with anything that plugs into the hot wires coming out of the wall. It’s outside the scope of Jim’s talk to cover this in detail, but you’re well advised to do the reading and learn from those more experienced before you get involved with mains-powered gear.

The rest of Jim’s talk covers the practical details of working with the ESP32. He notes that it’s important to think about GPIO pin statuses at startup, and to ensure you’re not mixing up 5 V and 3.3 V signals, which is an easy way to release some of that precious Magic Smoke.
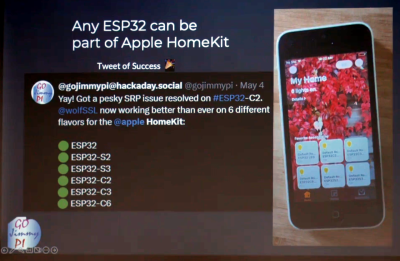
He also outlines the value of using tools like QEMU and Wokwi for emulation, in addition to having a simple devboard for development purposes. He explores a wide range of other topics that may be relevant to your hacking journey—using JTAG for debugging, working with Apple HomeKit, and even the basics of working with SSL and cryptography. And, naturally, he shows off some real ESP32-based products that you can go out and buy and start tinkering with right away!
Jim’s talk was one of the longer ones, and absolutely jam packed with information at that. No surprise given the topic is such a rich one. We’re blessed these days that companies are turning out all sorts of hackable devices using the popular ESP32 at their heart. They’re ripe for all kinds of tinkering; you just need to be willing to dive in, poke around, and do what you want with them!


























































































































![Top Features of Vision-Based Workplace Safety Tools [2025]](https://static.wixstatic.com/media/379e66_7e75a4bcefe14e4fbc100abdff83bed3~mv2.jpg/v1/fit/w_1000,h_884,al_c,q_80/file.png?#)




























![[The AI Show Episode 152]: ChatGPT Connectors, AI-Human Relationships, New AI Job Data, OpenAI Court-Ordered to Keep ChatGPT Logs & WPP’s Large Marketing Model](https://www.marketingaiinstitute.com/hubfs/ep%20152%20cover.png)



































































































































.jpg?#)











































![MindsEye From Ex-GTA Producer Is A Day-One Car Wreck [Update]](https://i.kinja-img.com/image/upload/c_fill,h_675,pg_1,q_80,w_1200/aa09b256615c422f7d1e1535d023e578.png)





















.png?width=1920&height=1920&fit=bounds&quality=70&format=jpg&auto=webp#)








































































































![PSA: iOS 26 Spatial Scenes will work on iPhones 12 and up [U]](https://i0.wp.com/9to5mac.com/wp-content/uploads/sites/6/2025/06/spatial-photos-ios26.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)
![Apple categorically denies Siri vaporware claims, and offers a better explanation [Video]](https://i0.wp.com/9to5mac.com/wp-content/uploads/sites/6/2025/06/Apple-categorically-denies-Siri-vaporware-claims-and-offers-a-better-explanation.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)
![This new iPad keyboard was purpose-built for versatility and portability – Logitech Flip Folio [Hands-on]](https://i0.wp.com/9to5mac.com/wp-content/uploads/sites/6/2025/06/Logitech-FI.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)
![Nothing confirms it was almost called ‘Essential’ instead [Video]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2025/06/nothing-essential-3.png?resize=1200%2C628&quality=82&strip=all&ssl=1)










![Apple Shares Teaser Trailer for 'The Lost Bus' Starring Matthew McConaughey [Video]](https://www.iclarified.com/images/news/97582/97582/97582-640.jpg)