Windows Common Log File System 0-Day Vulnerability Exploited in the Wild
A critical zero-day vulnerability in the Windows Common Log File System (CLFS) driver, tracked as CVE-2025-29824, has been actively exploited in the wild. This security flaw allows attackers to elevate privileges to SYSTEM level, posing a significant risk to affected systems. Microsoft has acknowledged the issue and is working on a security update, but no […] The post Windows Common Log File System 0-Day Vulnerability Exploited in the Wild appeared first on Cyber Security News.

A critical zero-day vulnerability in the Windows Common Log File System (CLFS) driver, tracked as CVE-2025-29824, has been actively exploited in the wild.
This security flaw allows attackers to elevate privileges to SYSTEM level, posing a significant risk to affected systems. Microsoft has acknowledged the issue and is working on a security update, but no immediate patch is available.
Windows Common Log File System 0-Day
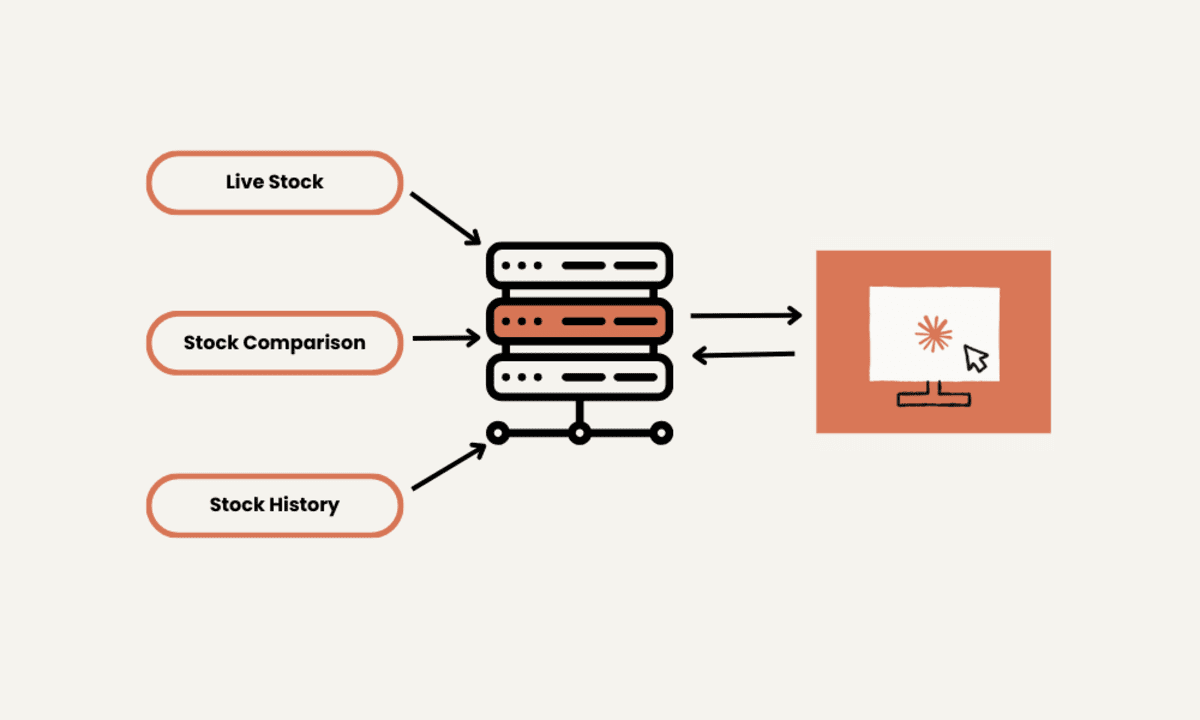
The vulnerability stems from a use-after-free issue within the CLFS driver, which improperly handles objects in memory.
This flaw enables an attacker with local access to execute malicious code with elevated privileges. Successful exploitation could allow attackers to gain SYSTEM-level access, bypassing critical security measures and potentially compromising sensitive data or system integrity.
The CLFS driver is a core component of Windows operating systems, responsible for managing transaction logs crucial for data reliability and recovery. The improper handling of log files in this driver creates an opportunity for attackers to manipulate memory and escalate privileges.
Microsoft has confirmed that CVE-2025-29824 has been exploited in the wild. Although details about specific attack campaigns remain undisclosed, the active exploitation underscores the urgency of addressing this vulnerability.
Public disclosure of exploit methods has not occurred yet, but the ongoing attacks highlight its real-world impact.
The vulnerability affects multiple versions of Windows 10, including both x64-based and 32-bit systems. Organizations relying on these systems are particularly at risk if they lack robust privilege management or endpoint protection measures.
Vulnerability Impact
Exploitation of CVE-2025-29824 can have severe consequences:
- Privilege Escalation: Attackers can gain SYSTEM-level access, enabling them to execute commands or modify critical system settings.
- Data Breach: Unauthorized access to sensitive data stored on compromised systems.
- Operational Disruption: Critical business operations could be disrupted due to system compromise or downtime.
- Malware Deployment: The vulnerability could serve as an entry point for ransomware or other malicious payloads.
Microsoft has addressed the vulnerability in the April 2025 security update. Organizations are urged to promptly apply the patches.
Microsoft has classified this vulnerability as “Important” with an elevation of privilege impact. The company has assured users that updates will be released promptly and that notifications will be provided through official channels once they become available.
Application Security is no longer just a defensive play, Time to Secure -> Free Webinar
The post Windows Common Log File System 0-Day Vulnerability Exploited in the Wild appeared first on Cyber Security News.




































































































































































![[The AI Show Episode 143]: ChatGPT Revenue Surge, New AGI Timelines, Amazon’s AI Agent, Claude for Education, Model Context Protocol & LLMs Pass the Turing Test](https://www.marketingaiinstitute.com/hubfs/ep%20143%20cover.png)












































































































![From Accountant to Data Engineer with Alyson La [Podcast #168]](https://cdn.hashnode.com/res/hashnode/image/upload/v1744420903260/fae4b593-d653-41eb-b70b-031591aa2f35.png?#)































































































.png?#)




































































































































![Apple Watch SE 2 On Sale for Just $169.97 [Deal]](https://www.iclarified.com/images/news/96996/96996/96996-640.jpg)

![Apple Posts Full First Episode of 'Your Friends & Neighbors' on YouTube [Video]](https://www.iclarified.com/images/news/96990/96990/96990-640.jpg)























































































































.webp?#)

