Hacking deep learning: model inversion attack by example
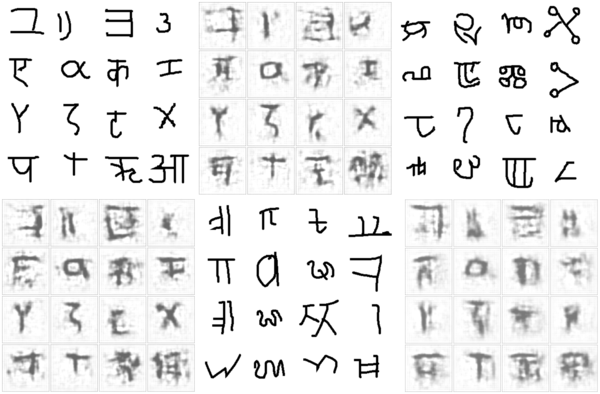
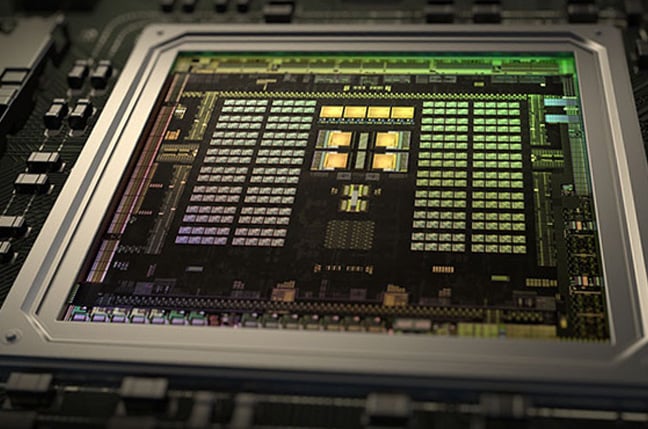
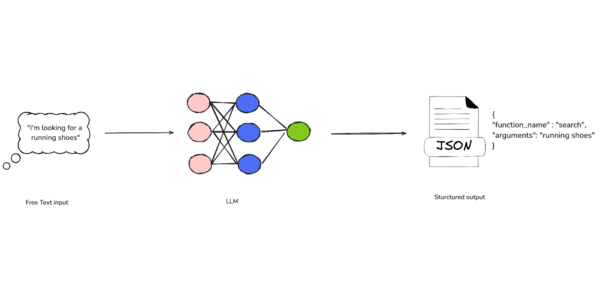
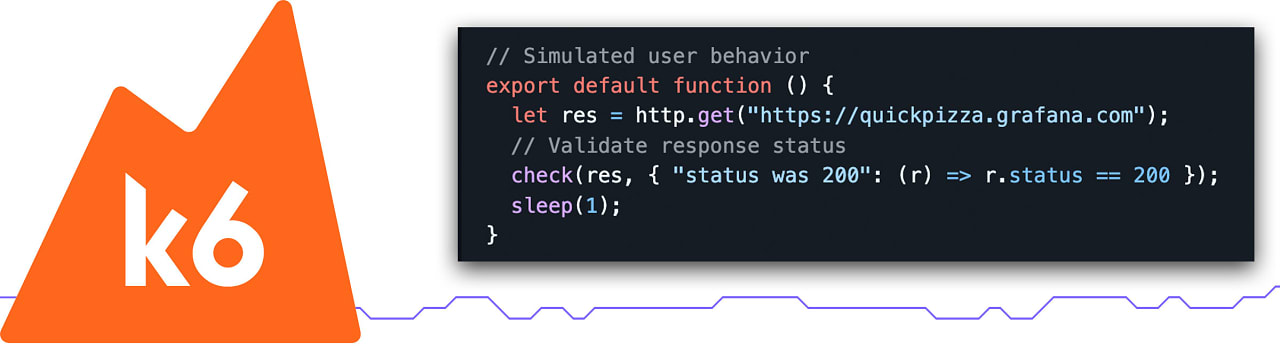
Compared to other applications, deep learning models might not seem too likely as victims of privacy attacks. However, methods exist to determine whether an entity was used in the training set (an adversarial attack called member inference), and techniques subsumed under "model inversion" allow to reconstruct raw data input given just model output (and sometimes, context information). This post shows an end-to-end example of model inversion, and explores mitigation strategies using TensorFlow Privacy.
Compared to other applications, deep learning models might not seem too likely as victims of privacy attacks. However, methods exist to determine whether an entity was used in the training set (an adversarial attack called member inference), and techniques subsumed under "model inversion" allow to reconstruct raw data input given just model output (and sometimes, context information). This post shows an end-to-end example of model inversion, and explores mitigation strategies using TensorFlow Privacy.

























































































































































![[The AI Show Episode 150]: AI Answers: AI Roadmaps, Which Tools to Use, Making the Case for AI, Training, and Building GPTs](https://www.marketingaiinstitute.com/hubfs/ep%20150%20cover.png)
![[The AI Show Episode 149]: Google I/O, Claude 4, White Collar Jobs Automated in 5 Years, Jony Ive Joins OpenAI, and AI’s Impact on the Environment](https://www.marketingaiinstitute.com/hubfs/ep%20149%20cover.png)






























































































![[PHP] Upgrading from PHP 7.4 to 8.1](https://media2.dev.to/dynamic/image/width%3D1000,height%3D500,fit%3Dcover,gravity%3Dauto,format%3Dauto/https:%2F%2Fdev-to-uploads.s3.amazonaws.com%2Fuploads%2Farticles%2Fqmaaabplfbcjejg2rr5n.png)



























































































































_ArtemisDiana_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale#)






















































































![In the market for a new router? Here are 13 models to avoid, according to the FBI [U]](https://i0.wp.com/9to5mac.com/wp-content/uploads/sites/6/2025/04/Most-Americans-are-paying-more-for-broadband-%E2%80%93-here-are-four-solutions.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)




![Galaxy S25 Ultra gets ‘Arc’ case that leaves the phone mostly exposed – available for Pixel 9 too [Gallery]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2025/05/arc-pulse-case-galaxy-s25-ultra-1.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)
















![Apple 15-inch M4 MacBook Air On Sale for $1023.86 [Lowest Price Ever]](https://www.iclarified.com/images/news/97468/97468/97468-640.jpg)