02: Create and configure network security groups
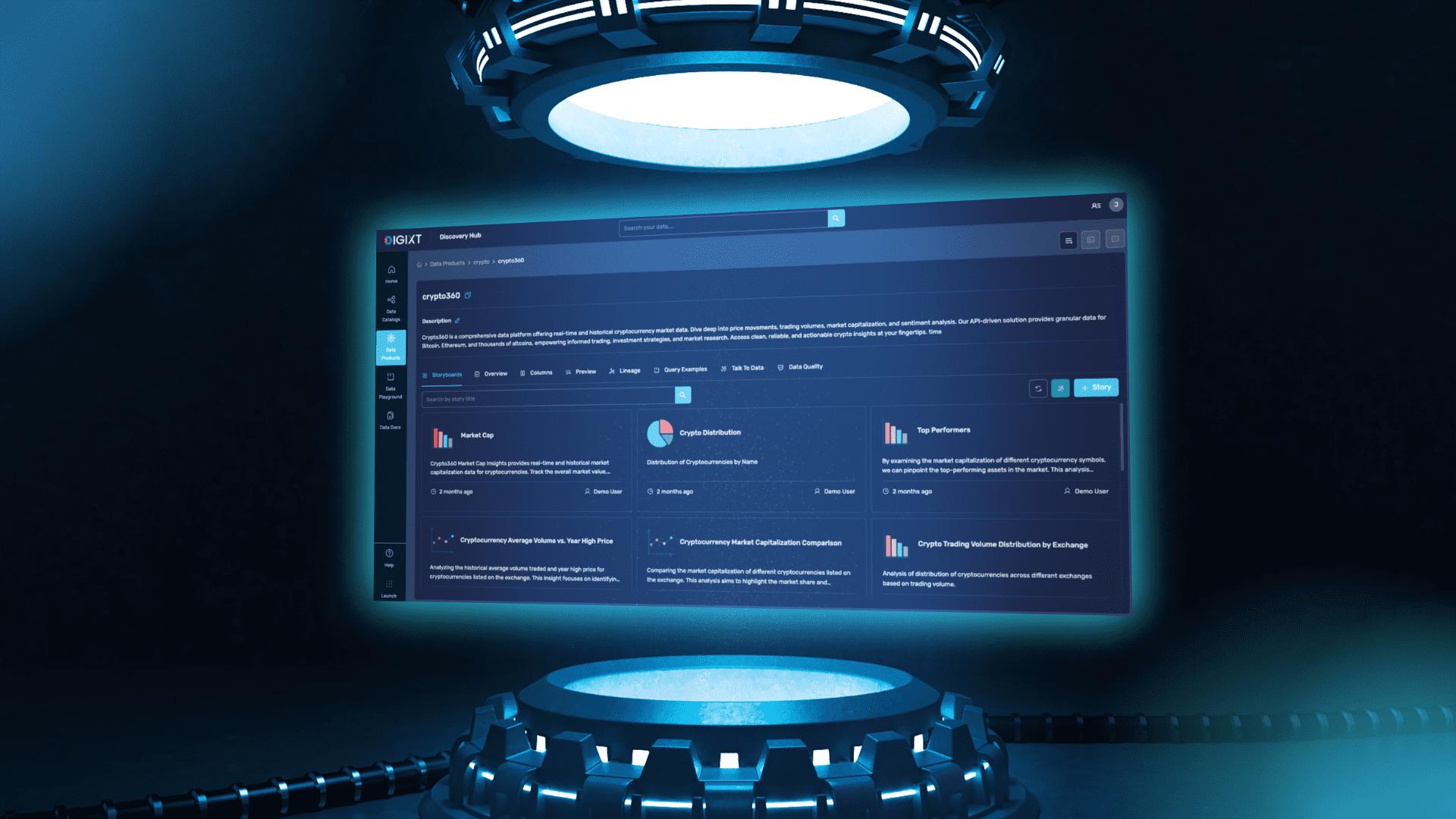
Create the network infrastructure for the exercise Note: This exercise requires the Lab 01 virtual networks and subnets to be installed. A template is provided if you need to deploy those resources. Scenario Your organization requires the network traffic in the app-vnet to be tightly controlled. You identify these requirements. The frontend subnet has web servers that can be accessed from the internet. An application security group (ASG) is required for those servers. The ASG should be associated with any virtual machine interface that is part of the group. This will allow the web servers to be easily managed. The backend subnet has database servers used by the frontend web servers. A network security group (NSG) is required to control this traffic. The NSG should be associated with any virtual machine interface that will be accessed by the web servers. For testing, a virtual machine should be installed in the frontend subnet (VM1) and the backend subnet (VM2). The IT group has provided an Azure resource manager template to deploy these Ubuntu servers. Skilling tasks Create a network security group. Create network security group rules. Associate a network security group to a subnet. Create and use application security groups in network security group rules. Firstly; we need to create and deploy 2 virtual machines to complete this task In the portal search for and select virtual machines. Verify both vm1 and vm2 are Running. Next; Create Application Security Group Application security groups (ASGs) let you group together servers with similar functions. For example, all the web servers hosting your application. 1, In the portal, search for and select Application security groups 2, Select + Create and configure the application security group. 3, Select Review + create and then select Create. Associate the application security group to the network interface of the VM In the Azure portal, search for and select VM1. In the Networking blade, select Application security groups and then select Add application security groups. Select the app-frontend-asg and then select Add. Create and Associate the Network Security Group Network security groups (NSGs) secure network traffic in a virtual network. In the portal search for and select Network security group. Select + Create and configure the network security group. Select Review + create and then select Create. Associate the NSG with the app-vnet backend subnet. NSGs can be associated with subnets and/or individual network interfaces attached to Azure virtual machines. Select Go to resource or navigate to the app-vnet-nsg resource. In the Settings blade select Subnets. Select + Associate Select app-vnet (RG1) and then the Backend subnet. Select OK. Create Network Security Group rules An NSG use security rules to filter inbound and outbound network traffic. In the search box at the top of the portal, enter Network security groups. Select Network security groups in the search results. Select app-vnet-nsg from the list of network security groups. In the Settings blade, select Inbound security rules. Select + Add and configure an inbound security rule.
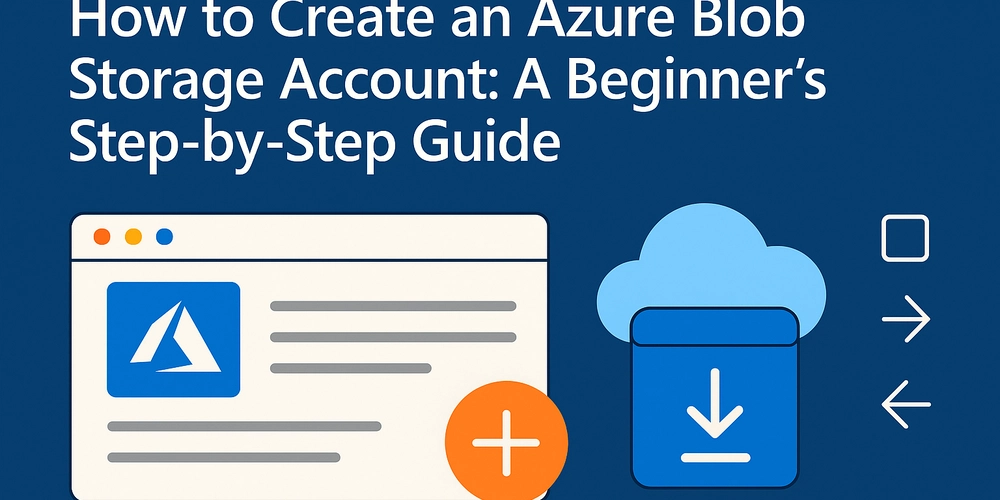
Create the network infrastructure for the exercise
Note: This exercise requires the Lab 01 virtual networks and subnets to be installed. A template is provided if you need to deploy those resources.
Scenario
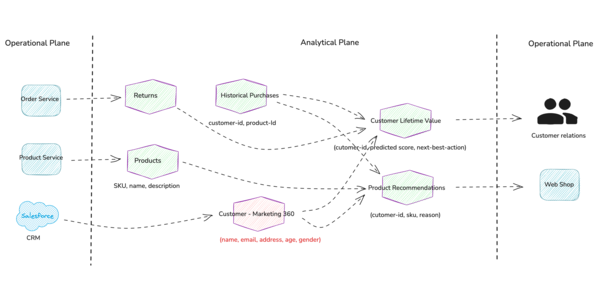
Your organization requires the network traffic in the app-vnet to be tightly controlled. You identify these requirements.
The frontend subnet has web servers that can be accessed from the internet. An application security group (ASG) is required for those servers. The ASG should be associated with any virtual machine interface that is part of the group. This will allow the web servers to be easily managed.
The backend subnet has database servers used by the frontend web servers. A network security group (NSG) is required to control this traffic. The NSG should be associated with any virtual machine interface that will be accessed by the web servers.
For testing, a virtual machine should be installed in the frontend subnet (VM1) and the backend subnet (VM2). The IT group has provided an Azure resource manager template to deploy these Ubuntu servers.
Skilling tasks
Create a network security group.
Create network security group rules.
Associate a network security group to a subnet.
Create and use application security groups in network security group rules.
-
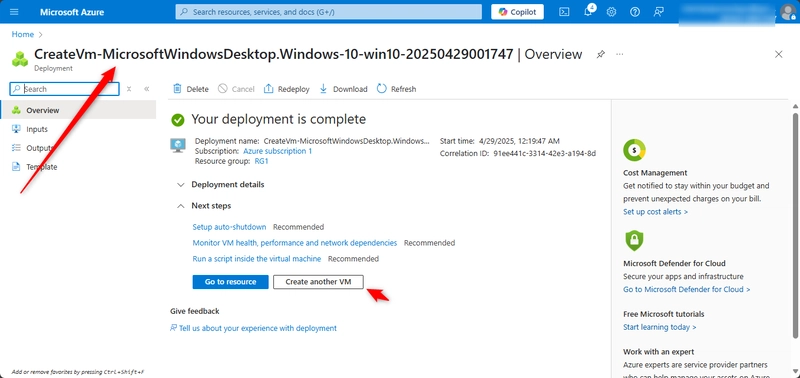
Firstly; we need to create and deploy 2 virtual machines to complete this task
In the portal search for and select virtual machines. Verify both vm1 and vm2 are Running.
Next;
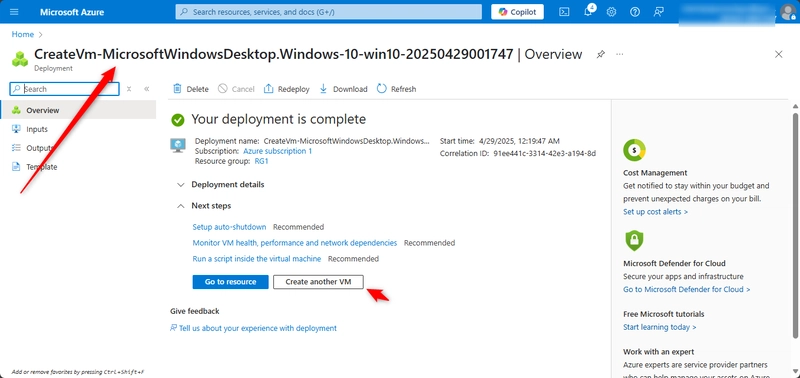
Create Application Security Group
Application security groups (ASGs) let you group together servers with similar functions. For example, all the web servers hosting your application.
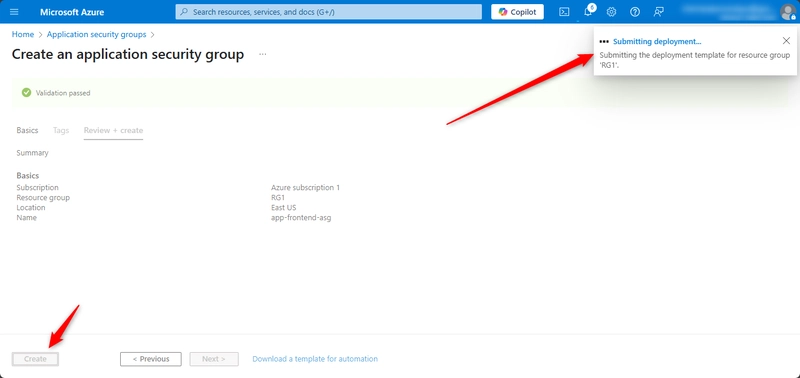
1, In the portal, search for and select Application security groups
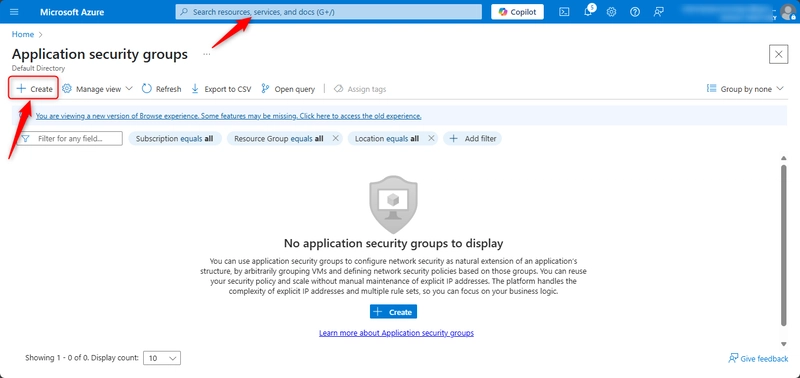
2, Select + Create and configure the application security group.
3, Select Review + create and then select Create.
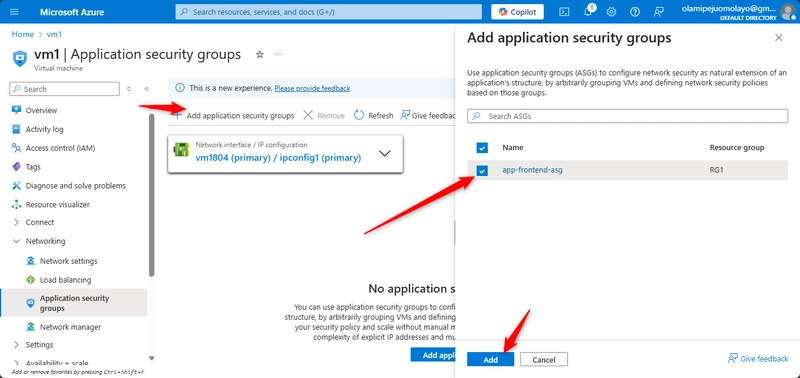
Associate the application security group to the network interface of the VM
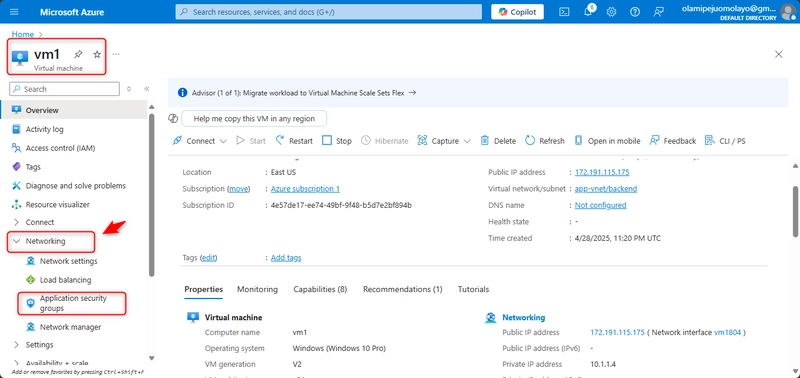
In the Azure portal, search for and select VM1.
In the Networking blade, select Application security groups and then select Add application security groups.
Select the app-frontend-asg and then select Add.
Create and Associate the Network Security Group
Network security groups (NSGs) secure network traffic in a virtual network.
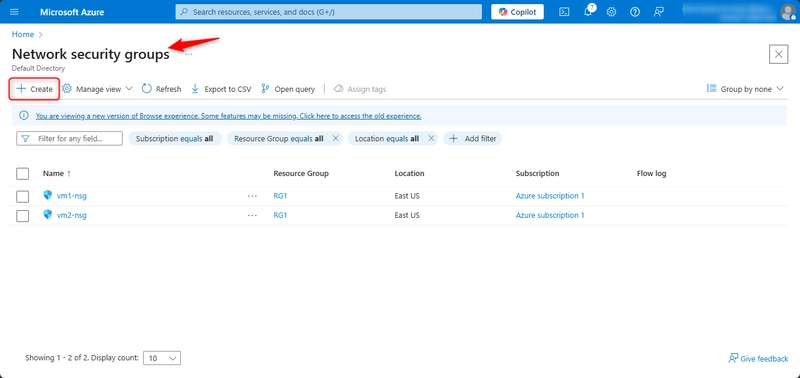
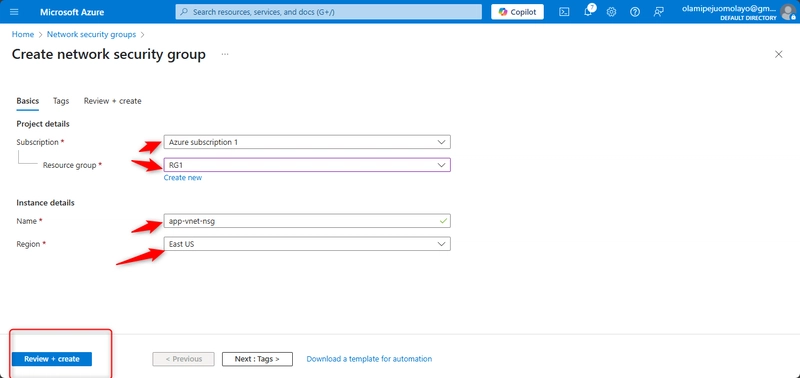
In the portal search for and select Network security group.
Select + Create and configure the network security group.
Select Review + create and then select Create.
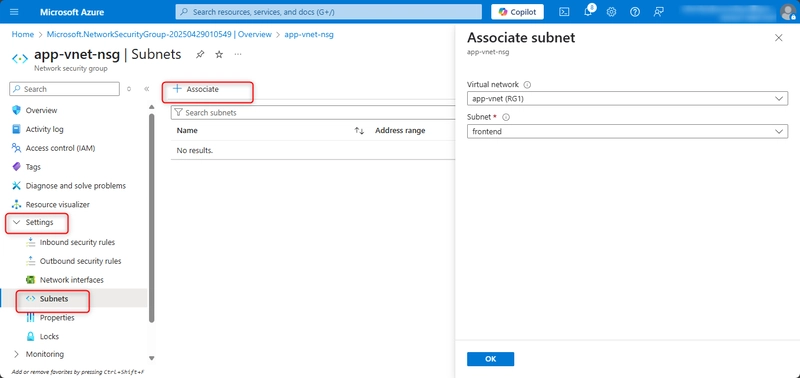
Associate the NSG with the app-vnet backend subnet.
NSGs can be associated with subnets and/or individual network interfaces attached to Azure virtual machines.
Select Go to resource or navigate to the app-vnet-nsg resource.
In the Settings blade select Subnets.
Select + Associate
Select app-vnet (RG1) and then the Backend subnet. Select OK.
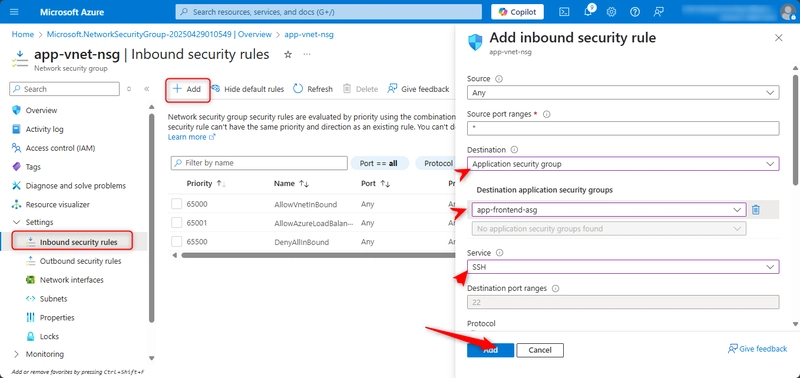
Create Network Security Group rules
An NSG use security rules to filter inbound and outbound network traffic.
In the search box at the top of the portal, enter Network security groups. Select Network security groups in the search results.
Select app-vnet-nsg from the list of network security groups.
In the Settings blade, select Inbound security rules.

















































































































































![[The AI Show Episode 145]: OpenAI Releases o3 and o4-mini, AI Is Causing “Quiet Layoffs,” Executive Order on Youth AI Education & GPT-4o’s Controversial Update](https://www.marketingaiinstitute.com/hubfs/ep%20145%20cover.png)





























































































































.jpg?#)






















































































_NicoElNino_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale#)













































































































![Standalone Meta AI App Released for iPhone [Download]](https://www.iclarified.com/images/news/97157/97157/97157-640.jpg)