Manage Engine Analytics Vulnerability Allows User Account Takeover
A high-severity authentication vulnerability in ManageEngine Analytics Plus on-premise installations has been identified, potentially allowing malicious actors to gain unauthorized access to Active Directory (AD) authenticated user accounts. The vulnerability, tracked as CVE-2025-1724, affects all Windows builds prior to 6130 and was patched on March 11, 2025. Security teams are urged to update affected systems […] The post Manage Engine Analytics Vulnerability Allows User Account Takeover appeared first on Cyber Security News.

A high-severity authentication vulnerability in ManageEngine Analytics Plus on-premise installations has been identified, potentially allowing malicious actors to gain unauthorized access to Active Directory (AD) authenticated user accounts.
The vulnerability, tracked as CVE-2025-1724, affects all Windows builds prior to 6130 and was patched on March 11, 2025. Security teams are urged to update affected systems immediately to mitigate the risk of account takeovers.
The flaw in ManageEngine Analytics Plus on-premise creates a critical authentication bypass vulnerability that security researchers have classified as high severity.
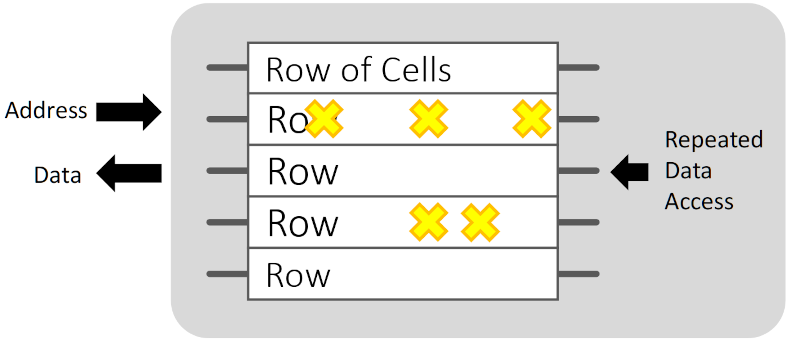
This vulnerability specifically affects the AD authentication flow in Windows-based installations that don’t have Active Directory Single Sign-On (SSO) configurations enabled.
During analysis, security experts determined that the vulnerability could be exploited to intercept and manipulate authentication processes, potentially leading to complete account takeover scenarios.
The core issue stems from insufficient key management and inadequate encryption in the authentication handling process.
The authentication flaw allows attackers to potentially capture and replay authentication tokens, effectively impersonating legitimate users without requiring their credentials.
The vulnerability was discovered and responsibly disclosed by security researcher Muhammed Mekkawy through ManageEngine’s Bug Bounty program.
Risk Factors Details Affected Products All Analytics Plus on-premise Windows builds below 6130 Impact Access to AD user accountsExposure of sensitive user informationAccount takeover capability Exploit Prerequisites Windows installation AD authentication without SSO configuration Network access to target system CVSS 3.1 Score 8.2 (High)
Organizations running vulnerable versions of Analytics Plus face significant risks. Successful exploitation could enable attackers to gain unauthorized access to sensitive data analytics dashboards, reports, and underlying data sources connected to the platform.
The vulnerability effectively compromises the authentication boundary that segregates user accounts.
“The potential for account takeover attacks exposes organizations to data exfiltration, privilege escalation, and potential regulatory compliance issues.”
The most significant impacts include:
- Unauthorized access to sensitive analytics dashboards and reports
- Potential exposure of connected data sources
- Compromised user account integrity
- Possible privilege escalation within the platform
Mitigations
ManageEngine has addressed this vulnerability in build 6130, released on March 11, 2025.
The fix implements robust key management practices by generating installation-specific keys and storing them with appropriate encryption strength.
This remediation prevents the interception and manipulation of authentication data that made the vulnerability exploitable.
Organizations should download the latest upgrade pack from ManageEngine’s service pack page and follow the provided instructions to update to the patched version.
IT administrators are encouraged to implement the fix during scheduled maintenance windows to minimize operational disruption.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Manage Engine Analytics Vulnerability Allows User Account Takeover appeared first on Cyber Security News.











































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)








































































































































_Anthony_Brown_Alamy.jpg?#)
_Hanna_Kuprevich_Alamy.jpg?#)




.png?#)

















































































![Hands-on: We got to play Nintendo Switch 2 for nearly six hours yesterday [Video]](https://i0.wp.com/9to5toys.com/wp-content/uploads/sites/5/2025/04/Switch-FI-.jpg.jpg?resize=1200%2C628&ssl=1)
![Fitbit redesigns Water stats and logging on Android, iOS [U]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2023/03/fitbit-logo-2.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)













![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)
























































































































.webp?#)


