LibreOffice Vulnerabilities Let Attackers Execute Malicious Files on Windows Systems
A critical security vulnerability in LibreOffice (CVE-2025-0514) has been patched after researchers discovered that manipulated documents could bypass safeguards and execute malicious files on Windows systems. The flaw, rated 7.2 on the CVSS v4.0 scale, exposes users to potential remote code execution (RCE) attacks by exploiting LibreOffice’s hyperlink handling mechanism. The vulnerability stems from improper […] The post LibreOffice Vulnerabilities Let Attackers Execute Malicious Files on Windows Systems appeared first on Cyber Security News.
.webp?#)
A critical security vulnerability in LibreOffice (CVE-2025-0514) has been patched after researchers discovered that manipulated documents could bypass safeguards and execute malicious files on Windows systems.
The flaw, rated 7.2 on the CVSS v4.0 scale, exposes users to potential remote code execution (RCE) attacks by exploiting LibreOffice’s hyperlink handling mechanism.
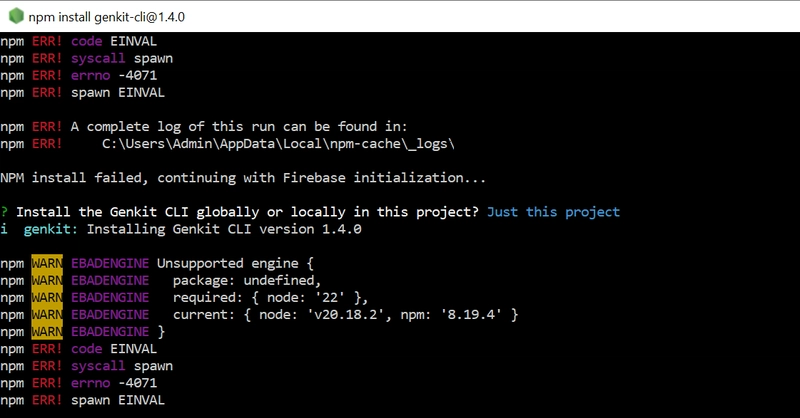
The vulnerability stems from improper input validation in LibreOffice’s handling of hyperlinks on Windows. When users press CTRL + Click on a hyperlink, the application passes the link to the Windows ShellExecute function, which processes the request.
While LibreOffice includes a security mechanism to block executable file paths from being passed to ShellExecute, attackers found a workaround using non-file URLs that mimic Windows file paths.
For example, a crafted link like \\attacker-server\malicious.exe could be interpreted as a local file path, bypassing LibreOffice’s filters and triggering the execution of malicious payloads.
This flaw affects LibreOffice versions 24.8 through 24.8.4 on Windows. Successful exploitation requires user interaction, as victims must click the hyperlink while holding the CTRL key.
However, attackers could embed such links in seemingly benign documents such as invoices or reports to increase the likelihood of activation.
Amel Bouziane-Leblond, the researcher who reported the flaw, emphasized that the exploit’s simplicity underscores the importance of rigorous input validation in office software.
Stephen Bergman of allotropia and Collabora’s Caolán McNamara developed the fix, which blocks non-file URL misinterpretations within ShellExecute.
Mitigation and Patches
The Document Foundation addressed the vulnerability in LibreOffice 24.8.5. The update modifies how non-file URLs are processed, ensuring they no longer bypass executable path checks.
Security teams strongly recommend immediate upgrades for all Windows users. Organizations unable to patch immediately should consider disabling hyperlink execution via LibreOffice’s settings or implementing application whitelisting to block unauthorized executables.
LibreOffice’s hyperlink feature, designed for user convenience, inadvertently created a vector for living-off-the-land (LOL) attacks, where legitimate system tools like ShellExecute are weaponized.
Similar issues have plagued LibreOffice in the past, including the 2018 WEBSERVICE function exploit (CVE-2018-6871), which allowed arbitrary file disclosures via manipulated spreadsheet formulas.
While no active exploits for CVE-2025-0514 have been observed yet, the public release of technical details increases the likelihood of weaponization.
For now, upgrading to LibreOffice 24.8.5 remains the most effective defense against CVE-2025-0514. Users can download the latest version from LibreOffice’s official site, while enterprise deployments should prioritize endpoint monitoring to detect anomalous process executions linked to document workflows.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free
The post LibreOffice Vulnerabilities Let Attackers Execute Malicious Files on Windows Systems appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)