North Korean IT Workers Attacking European Organizations to Infiltrate Corporate Infrastructure
North Korean IT workers have significantly expanded their operations beyond the United States, with a growing focus on European organizations. These threat actors pose as legitimate remote workers to infiltrate companies, generating revenue for the DPRK regime while potentially compromising sensitive corporate infrastructure. Their tactics have evolved to include falsifying credentials, building rapport with recruiters, […] The post North Korean IT Workers Attacking European Organizations to Infiltrate Corporate Infrastructure appeared first on Cyber Security News.

North Korean IT workers have significantly expanded their operations beyond the United States, with a growing focus on European organizations.
These threat actors pose as legitimate remote workers to infiltrate companies, generating revenue for the DPRK regime while potentially compromising sensitive corporate infrastructure.
Their tactics have evolved to include falsifying credentials, building rapport with recruiters, and utilizing multiple personas to vouch for their fabricated identities across job platforms like Upwork and Telegram.
The infiltration begins when these operatives apply for remote technical positions, particularly targeting those in the defense industrial base and government sectors.
They craft elaborate backstories, claiming nationalities from diverse countries including Italy, Japan, Malaysia, Singapore, and Ukraine.
.webp)
To circumvent verification procedures, they deploy a sophisticated network of facilitators who help defeat identity checks and manage the fraudulent receipt of funds.
Google Threat Intelligence Group (GTIG) has identified this expanding threat through extensive investigations conducted in collaboration with security partners.
Their research indicates a tactical shift in response to increased awareness and enforcement actions in the United States, driving these operatives to establish more robust operations across Europe.
The impact of these infiltrations extends beyond simple fraud, as recent incidents show an increase in extortion attempts against former employers.
When discovered and terminated, these IT workers have threatened to release sensitive data or sell proprietary source code to competitors, representing a significant escalation in their approach.
This shift coincided with heightened law enforcement actions, suggesting the pressure is driving them toward more aggressive revenue-generation tactics.
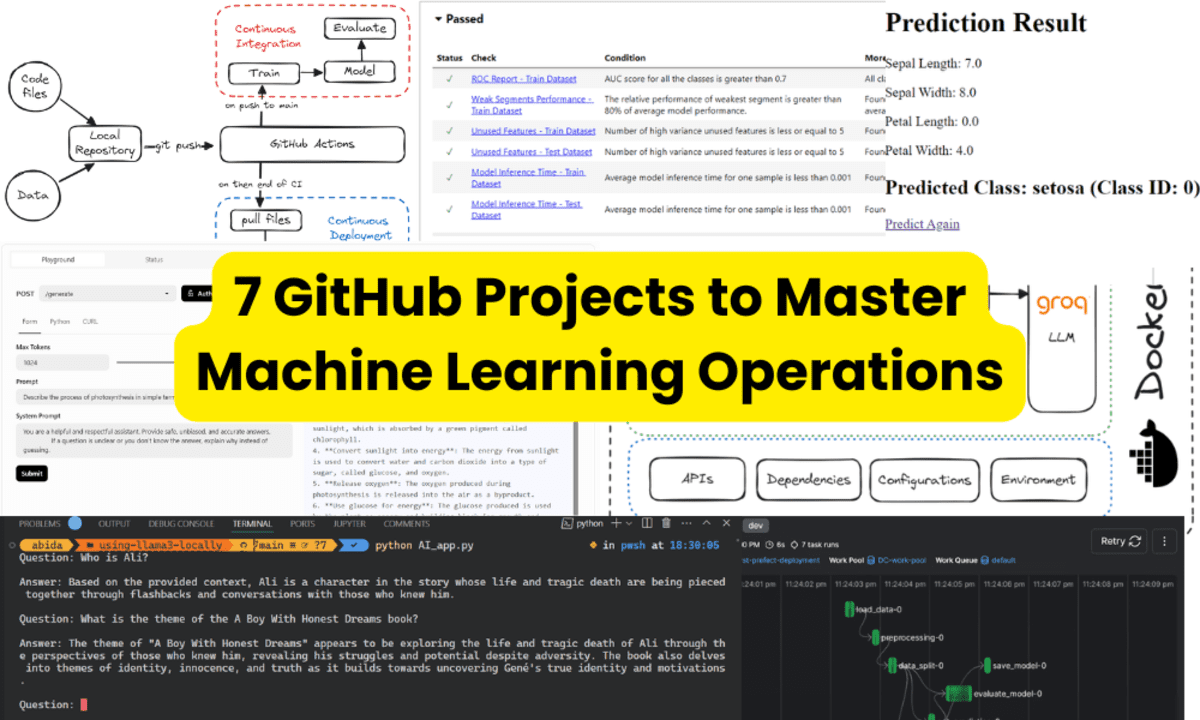
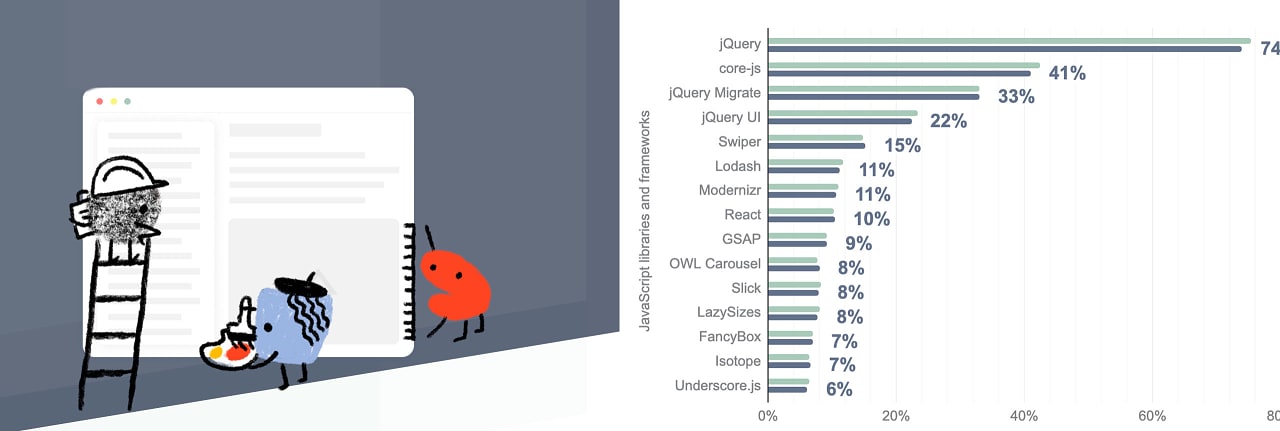
Technical projects undertaken by these operatives demonstrate considerable expertise, spanning traditional web development to advanced blockchain and AI applications.
Their work includes development using Next.js, React, CosmosSDK, Golang, and blockchain technologies such as Solana and Anchor/Rust smart contracts.
Exploitation of Virtualized Infrastructure
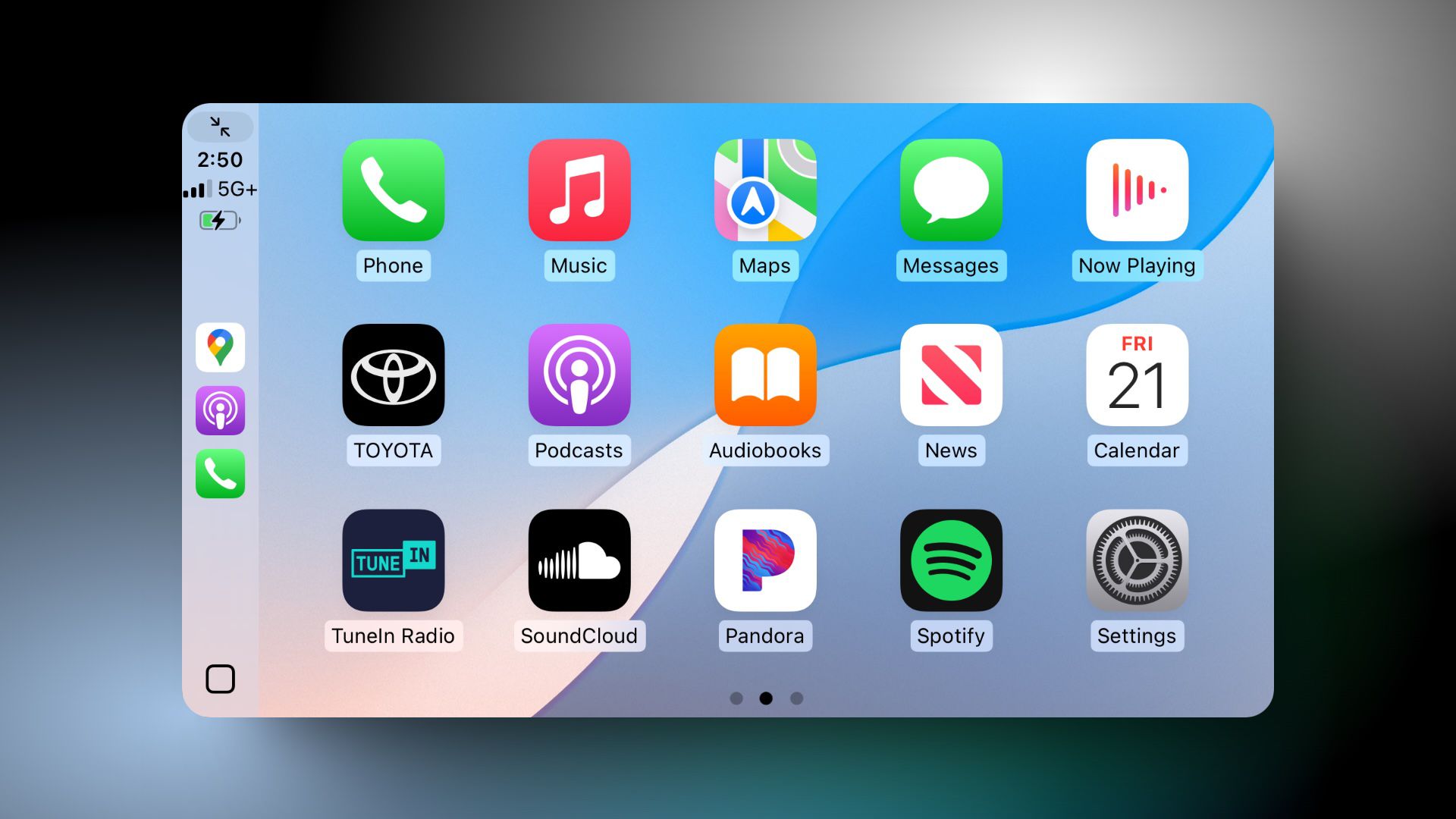
A particularly concerning development is the DPRK IT workers’ focus on bring your own device (BYOD) environments starting in January 2025.
These settings allow employees to access company systems through virtual machines on personal devices, creating significant security blind spots.
Unlike corporate laptops that contain monitoring software, personal devices operating under BYOD policies typically lack traditional security and logging tools, making their activities substantially harder to track.
This environment eliminates conventional evidence trails such as corporate laptop shipping addresses and endpoint software inventories.
Without these detection mechanisms, the IT workers can operate with minimal risk of discovery while accessing sensitive corporate resources.
Security analysts note that this approach represents a strategic evolution, as the operatives have identified these virtualized environments as particularly vulnerable to their infiltration schemes.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post North Korean IT Workers Attacking European Organizations to Infiltrate Corporate Infrastructure appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






































































































































































































































.jpg?#)










































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)