Why do I need an authorisation server if my micro services can validate JWTs directly?
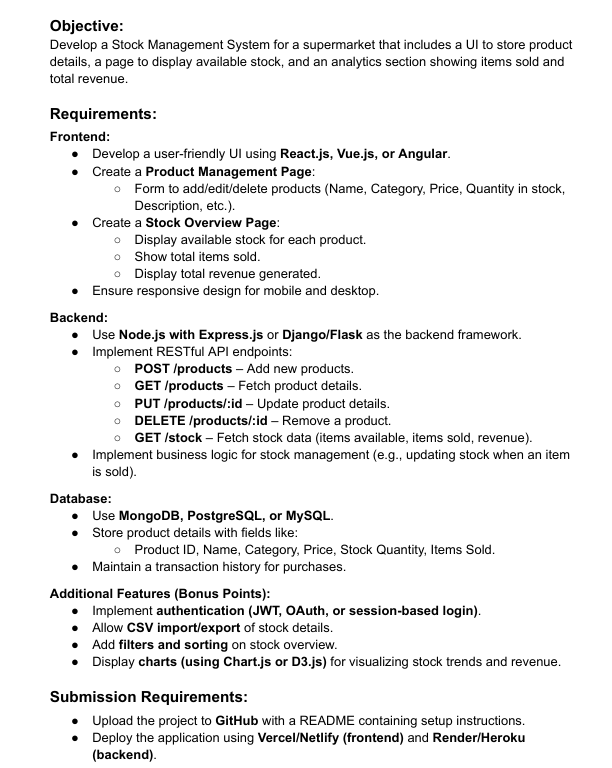
I'm working on a Spring-based micro service project and considering different approaches for handling authentication and authorisation. Instead of setting up a dedicated authorisation server, I’m thinking of implementing JWT validation directly within each micro service. Proposed Approach Each microservice will contain a JWT decoder bean to validate tokens locally. The public key for verifying JWT signatures will be retrieved from AWS Secrets Manager, allowing dynamic key rotation without service disruption. I plan to expose two authentication endpoints in my resource server: User authentication → Accepts a username and password to return a JWT access token and a refresh token. Service-to-service authentication → Issues a short-lived JWT to microservices. This could be implemented using either: A service name and secret pair. Mutual TLS (mTLS) for stronger security. Reasons for This Approach Cost efficiency – Avoids hosting a standalone authorization server just for issuing tokens. Improved availability – No single point of failure; each microservice can validate JWTs independently. Performance benefits – JWT validation is stateless, eliminating network calls to an external authorization server. Secure key management – Fetching the public key from AWS Secrets Manager enables dynamic key rotation. OAuth2 might be unnecessary – My system has no third-party applications, only: Internal microservices communicating with each other. A dashboard that retrieves user data using JWT authentication. Question Is this a valid approach? What are the potential pitfalls or improvements I should consider?
I'm working on a Spring-based micro service project and considering different approaches for handling authentication and authorisation. Instead of setting up a dedicated authorisation server, I’m thinking of implementing JWT validation directly within each micro service.
Proposed Approach
Each microservice will contain a JWT decoder bean to validate tokens locally. The public key for verifying JWT signatures will be retrieved from AWS Secrets Manager, allowing dynamic key rotation without service disruption. I plan to expose two authentication endpoints in my resource server:
- User authentication → Accepts a username and password to return a JWT access token and a refresh token.
- Service-to-service authentication → Issues a short-lived JWT to microservices. This could be implemented using either:
- A service name and secret pair.
- Mutual TLS (mTLS) for stronger security.
Reasons for This Approach
- Cost efficiency – Avoids hosting a standalone authorization server just for issuing tokens.
- Improved availability – No single point of failure; each microservice can validate JWTs independently.
- Performance benefits – JWT validation is stateless, eliminating network calls to an external authorization server.
- Secure key management – Fetching the public key from AWS Secrets Manager enables dynamic key rotation.
- OAuth2 might be unnecessary – My system has no third-party applications, only: Internal microservices communicating with each other. A dashboard that retrieves user data using JWT authentication.
Question
Is this a valid approach? What are the potential pitfalls or improvements I should consider?











































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)








































































































































_Anthony_Brown_Alamy.jpg?#)
_Hanna_Kuprevich_Alamy.jpg?#)




.png?#)

















































































![Hands-on: We got to play Nintendo Switch 2 for nearly six hours yesterday [Video]](https://i0.wp.com/9to5toys.com/wp-content/uploads/sites/5/2025/04/Switch-FI-.jpg.jpg?resize=1200%2C628&ssl=1)
![Fitbit redesigns Water stats and logging on Android, iOS [U]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2023/03/fitbit-logo-2.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)













![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)