Sophisticated QR Code Phishing Attack Targeting Microsoft 365 Users to Steal Logins
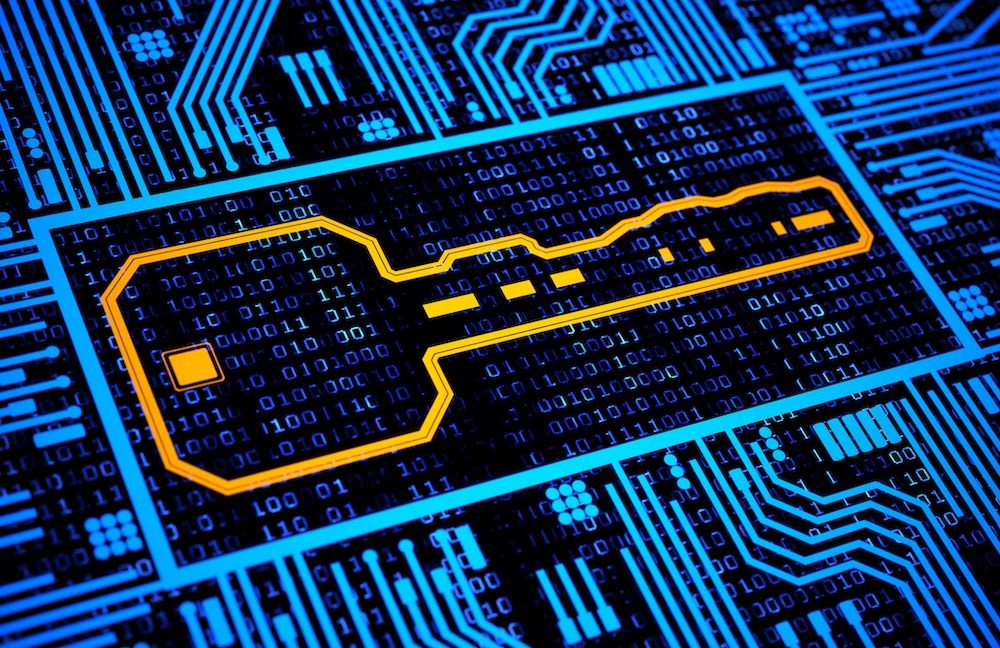
A new sophisticated phishing campaign leveraging QR codes to steal Microsoft 365 login credentials has emerged in the cybersecurity landscape. This attack represents a significant evolution in phishing tactics, combining social engineering with technical sophistication to bypass traditional email security measures. The campaign specifically targets corporate users, exploiting the increasing normalization of QR codes in […] The post Sophisticated QR Code Phishing Attack Targeting Microsoft 365 Users to Steal Logins appeared first on Cyber Security News.

A new sophisticated phishing campaign leveraging QR codes to steal Microsoft 365 login credentials has emerged in the cybersecurity landscape.
This attack represents a significant evolution in phishing tactics, combining social engineering with technical sophistication to bypass traditional email security measures.
The campaign specifically targets corporate users, exploiting the increasing normalization of QR codes in daily business operations.
The attack begins with victims receiving seemingly legitimate emails purporting to come from Microsoft or IT departments, claiming that users need to verify their accounts or that their passwords are expiring.
.webp)
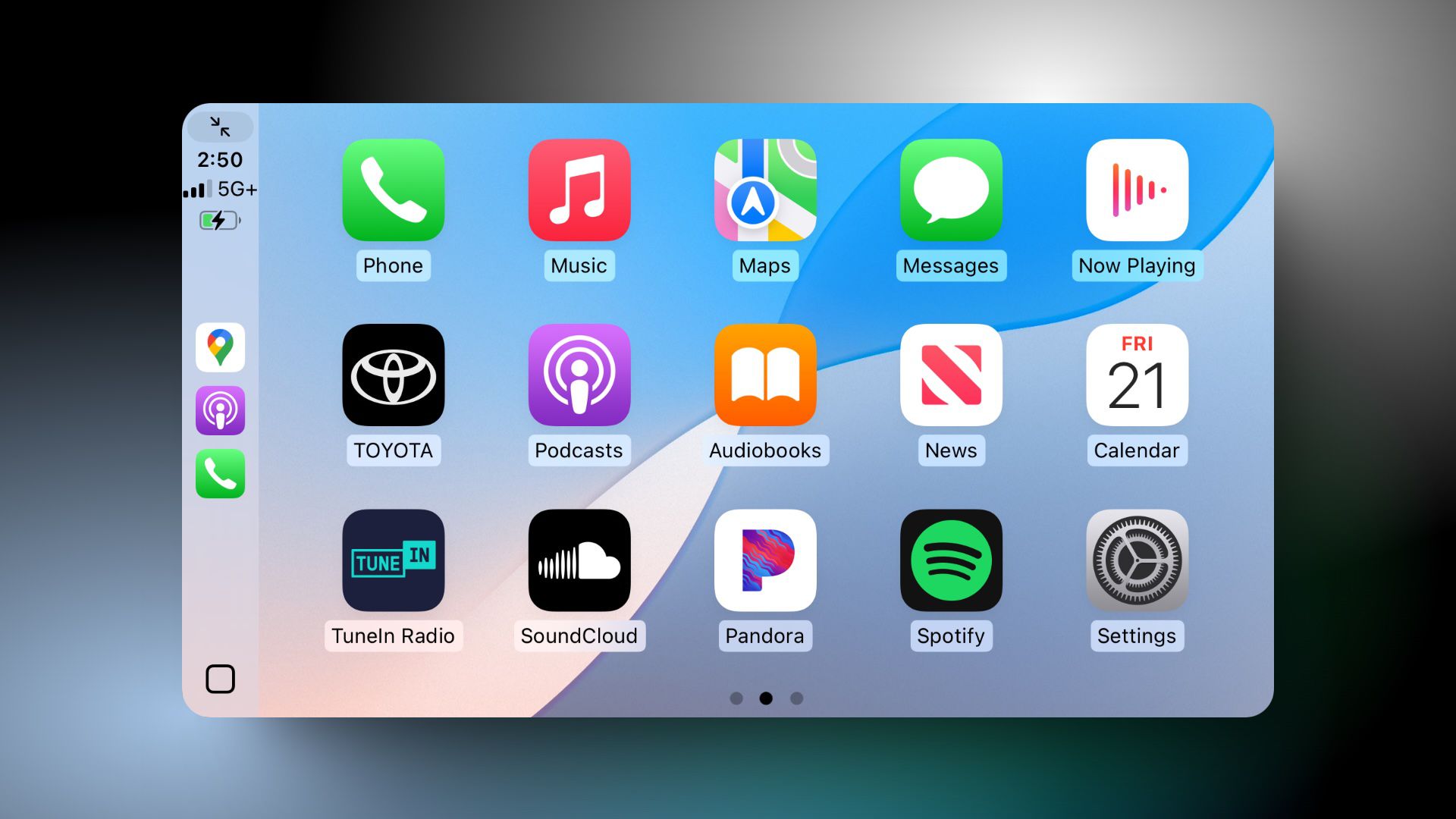
Rather than including suspicious links that might trigger security alerts, these emails contain QR codes that victims are instructed to scan with their mobile devices.
This approach cleverly circumvents many email security solutions that scan for malicious URLs or attachments.
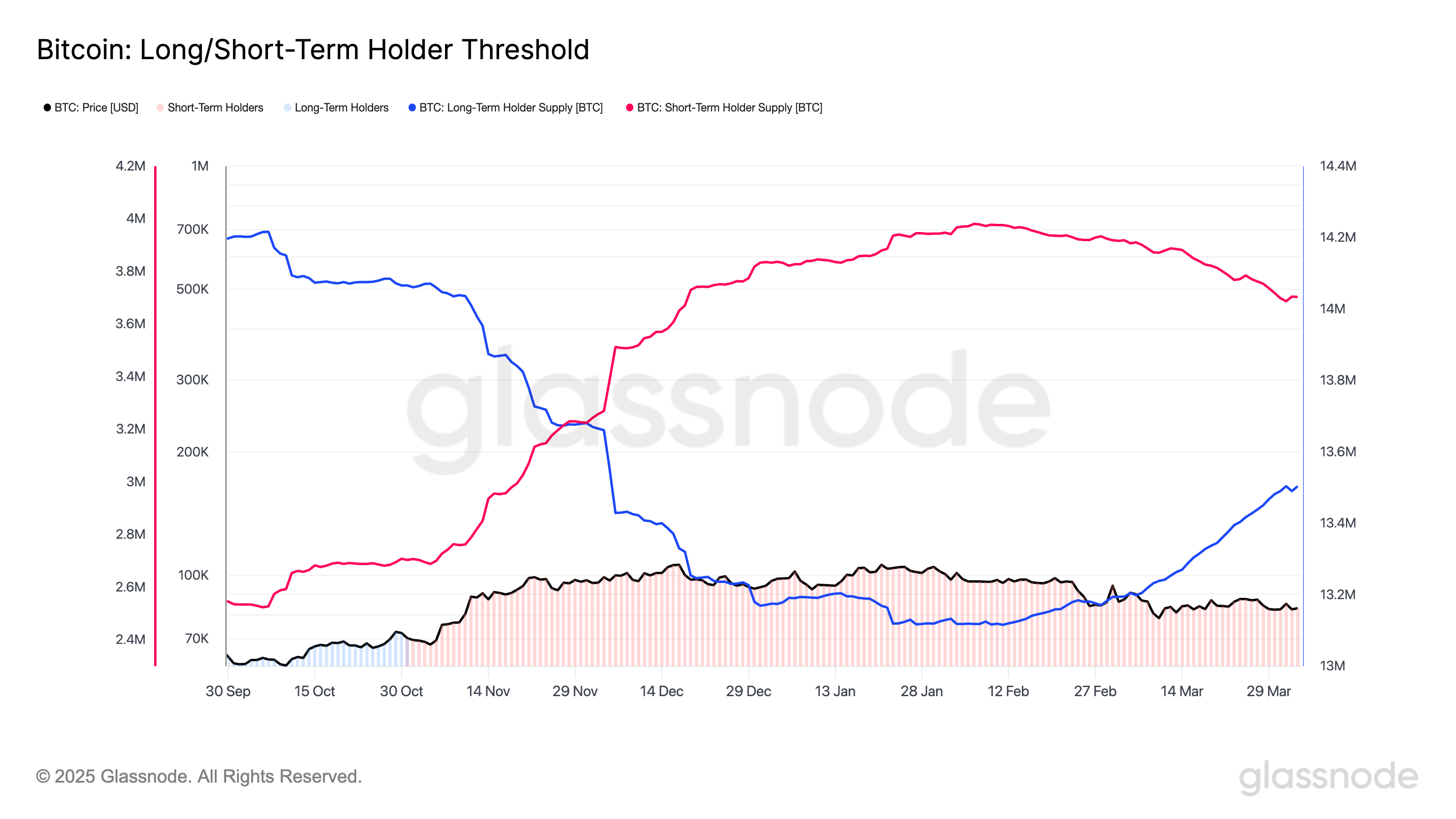
Palo Alto Networks security researchers identified this threat in early March 2025, noting a substantial increase in QR code-based phishing attempts targeting enterprise users.
Their analysis reveals that this campaign has successfully compromised credentials from organizations across multiple sectors, with financial services and healthcare being particularly affected.
When scanned, the QR code redirects users to convincing replica login pages designed to harvest Microsoft 365 credentials.
.webp)
The sophistication of these pages is notable, with attackers implementing JavaScript that validates email formats before submission, creating a more believable user experience while filtering out low-quality targets.
Technical Analysis of QR Redirection Mechanism
The QR codes embed specialized URLs that initiate a complex redirection chain to evade detection.
The initial redirect passes through seemingly benign domains before landing on the phishing page.
.webp)
Examination of the phishing site’s source code reveals sophisticated obfuscation techniques:-
function validateCredentials() {
const email = document.getElementById('email').value;
const password = document.getElementById('password').value;
if(email.match(/^[^\s@]+@[^\s@]+\.[^\s@]+$/) && password.length > 5) {
sendData(email, password);
window.location = "https://outlook.office.com/mail/";
} else {
document.getElementById('error-message').style.display = 'block';
}
}This code snippet demonstrates how the attack validates and exfiltrates user credentials while redirecting victims to legitimate Microsoft services post-compromise, leaving users unaware of the breach.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post Sophisticated QR Code Phishing Attack Targeting Microsoft 365 Users to Steal Logins appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)




















































































































































































































































































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)