Cisco Smart Licensing Utility Vulnerabilities Let Attackers Gain Admin Access
Two critical vulnerabilities were actively exploited in Cisco Smart Licensing Utility, potentially allowing attackers to gain administrative access to affected systems. Organizations running vulnerable software versions are urged to apply patches immediately as exploitation attempts continue to increase. According to recent reports from the SANS Internet Storm Center, two critical security flaws tracked as CVE-2024-20439 […] The post Cisco Smart Licensing Utility Vulnerabilities Let Attackers Gain Admin Access appeared first on Cyber Security News.
.webp?#)
Two critical vulnerabilities were actively exploited in Cisco Smart Licensing Utility, potentially allowing attackers to gain administrative access to affected systems.
Organizations running vulnerable software versions are urged to apply patches immediately as exploitation attempts continue to increase.
According to recent reports from the SANS Internet Storm Center, two critical security flaws tracked as CVE-2024-20439 and CVE-2024-20440 in Cisco Smart Licensing Utility are currently being exploited in the wild.
The vulnerabilities, discovered in September 2024 but now seeing active exploitation as of March 2025, could allow unauthorized attackers to gain administrative control over affected systems.
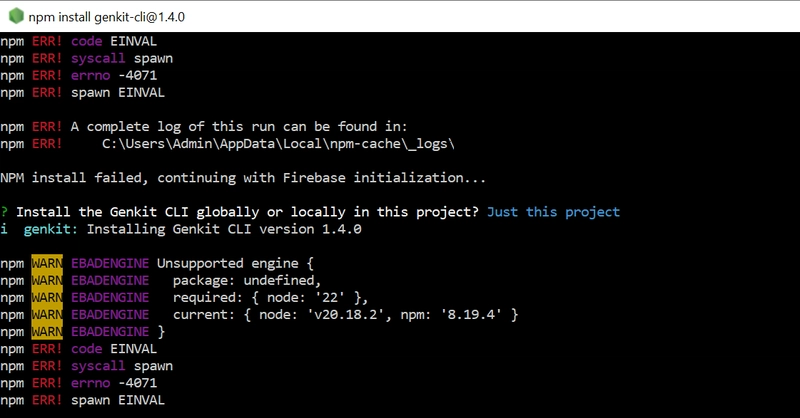
CVE-2024-20439 (CVSS score: 9.8)
An undocumented, static administrative credential hardcoded in CSLU versions 2.0.0–2.2.0.
Unauthenticated attackers can log into affected systems with full administrative privileges over the CSLU API, enabling complete system compromise.
It requires CSLU to be actively running (not a background service by default). Attackers use static credentials to bypass authentication.
CVE-2024-20440 (CVSS score: 9.8)
Excessive verbosity in debug logs, allowing attackers to retrieve log files containing API credentials via crafted HTTP requests.
The impact includes exposure of sensitive data, including credentials for lateral movement or persistent access. The flaw often chained with CVE-2024-20439 to escalate privileges and extract credentials from logs
“The vulnerabilities are not dependent on one another,” Cisco stated in its security advisory. “Exploitation of one of the vulnerabilities is not required to exploit the other vulnerability.”
The summary of the vulnerabilities is given below:
Risk Factors CVE-2024-20439 CVE-2024-20440 Affected Products Cisco Smart Licensing Utility versions 2.0.0, 2.1.0, 2.2.0 Cisco Smart Licensing Utility versions 2.0.0, 2.1.0, 2.2.0 Impact Full administrative access via hard coded static credentials Sensitive data exposure (e.g., API credentials) via verbose debug logs Exploit Prerequisites CSLU must be manually started and actively running CSLU must be running; attacker sends crafted HTTP requests CVSS 3.1 Score 9.8 (Critical) 9.8 (Critical)
Impact and Affected Systems
These vulnerabilities affect Cisco Smart Licensing Utility versions 2.0.0, 2.1.0, and 2.2.0. Version 2.3.0 is not affected by these security flaws. It’s worth noting that exploitation is only possible when the utility is actively running.
Johannes B. Ullrich, Dean of Research at SANS Technology Institute, confirmed that unidentified threat actors are actively exploiting these vulnerabilities, alongside other flaws, including what appears to be an information disclosure vulnerability (CVE-2024-0305) in Guangzhou Yingke Electronic Technology Ncast.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2024-20439 to its Known Exploited Vulnerabilities (KEV) catalog on March 31, 2025, requiring federal agencies to implement necessary fixes by April 21, 2025. This listing underscores the severity and active exploitation of these vulnerabilities.
Cisco has released software updates addressing these vulnerabilities, but there are no workarounds available. Organizations must upgrade to version 2.3.0 of the Cisco Smart License Utility, which is not vulnerable to these issues.
“In light of active abuse, it’s imperative that users apply the necessary patches for optimal protection,” security researchers emphasized.
The vulnerabilities were initially discovered by Eric Vance of Cisco during internal security testing. Although found in September 2024, exploitation attempts weren’t observed until March 2025, highlighting the persistent risk of unpatched vulnerabilities.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post Cisco Smart Licensing Utility Vulnerabilities Let Attackers Gain Admin Access appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)