Fluent Bit 0-day Vulnerabilities Exposes Billions of Production Environments to Cyber Attacks
Researchers uncovered critical zero-day vulnerabilities in Fluent Bit, a ubiquitous logging utility embedded in cloud infrastructure across major providers like AWS, Google Cloud, and Microsoft Azure. The flaws tracked as CVE-2024-50608 and CVE-2024-50609 (CVSS 8.9), exploit null pointer dereference weaknesses in Fluent Bit’s Prometheus Remote Write and OpenTelemetry plugins. With over 15 billion downloads and […] The post Fluent Bit 0-day Vulnerabilities Exposes Billions of Production Environments to Cyber Attacks appeared first on Cyber Security News.

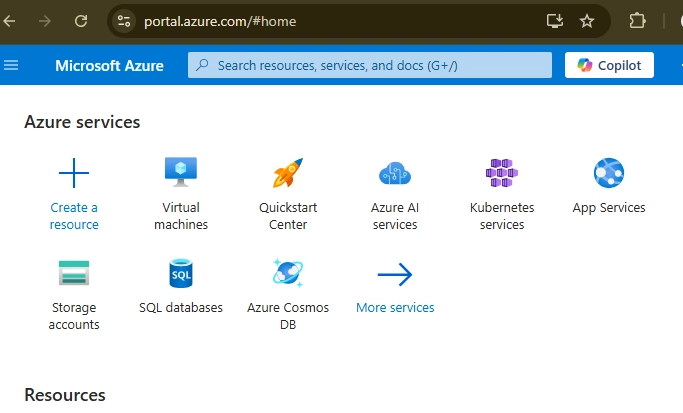
Researchers uncovered critical zero-day vulnerabilities in Fluent Bit, a ubiquitous logging utility embedded in cloud infrastructure across major providers like AWS, Google Cloud, and Microsoft Azure.
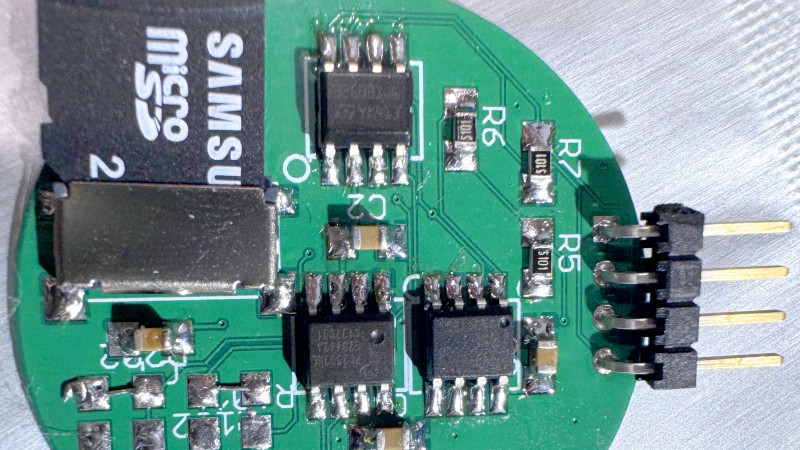
The flaws tracked as CVE-2024-50608 and CVE-2024-50609 (CVSS 8.9), exploit null pointer dereference weaknesses in Fluent Bit’s Prometheus Remote Write and OpenTelemetry plugins.
With over 15 billion downloads and 10 million daily deployments, these vulnerabilities threaten global enterprise and cloud ecosystems.
Exploit Mechanics and Attack Surface
The Prometheus Remote Write vulnerability allows unauthenticated attackers to crash Fluent Bit servers by sending an HTTP POST request with Content-Length: 0.
This triggers a null pointer dereference in the process_payload_metrics_ng() function when parsing metrics data. A proof-of-concept curl command demonstrates the simplicity of exploitation:
Similarly, the OpenTelemetry plugin fails to validate input types in trace configuration requests. Sending non-string values (e.g., integers) to the /api/v1/traces endpoint corrupts heap memory, enabling DoS or partial secret leakage.
Tenable’s lab tests confirmed adjacent memory exposure, occasionally revealing sensitive metrics data.
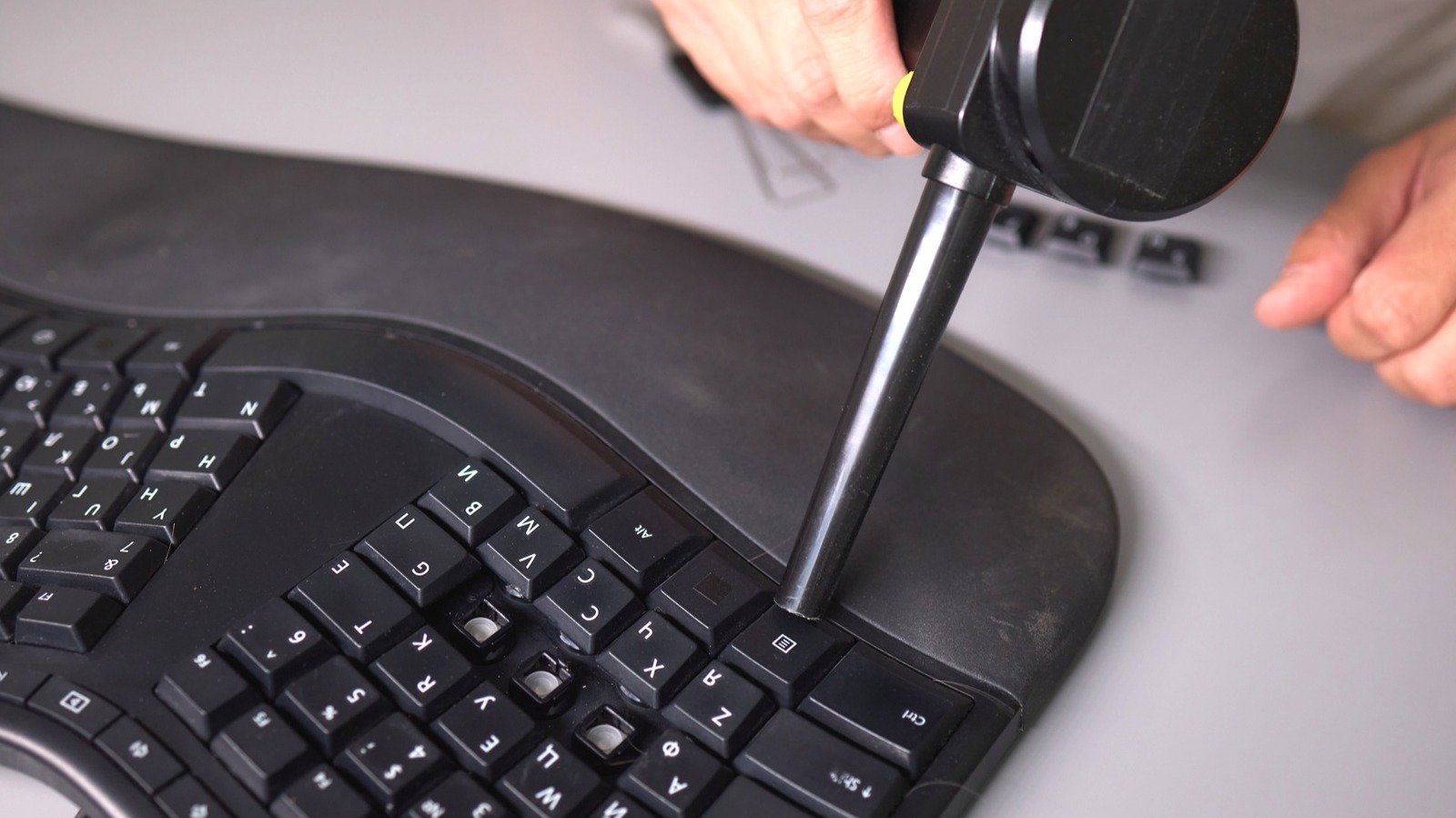
Fluent Bit’s architecture amplifies risks by spanning input parsing, filtering, and output routing. For example, misconfigured HTTP input plugins (below) expose APIs to malicious payloads:
Impact: Cloud Infrastructure and Enterprise Exposure
Fluent Bit’s integration into Kubernetes and cloud monitoring stacks means vulnerabilities cascade across services.
Cisco, Splunk, and VMware are major users, while hyperscalers like AWS Elastic Kubernetes Service (EKS) embed it by default.
Attackers exploiting these flaws could disrupt logging pipelines, paralyzing incident response and compliance workflows.
Ebryx’s fuzzing campaigns using Boofuzz revealed systemic issues. For instance, this script fuzzed the Prometheus plugin’s HTTP handler:
The lack of input validation in flb_sds_create_len() allowed trivial DoS attacks.
Mitigation and Industry Response
Fluent Bit maintainers released patches in v3.0.4, backported to v2.2.3. Key remediations include:
- Immediate patching of Fluent Bit instances.
- Restricting API access via network policies or authentication.
- Disabling unused endpoints like /api/v1/traces.
Enterprises must audit Fluent Bit configurations, segment monitoring networks, and adopt continuous fuzzing strategies.
As Tenable’s disclosure timeline shows, the industry’s collaborative patching effort, coordinated with AWS, Google, and Microsoft, prevented widespread exploitation.
However, with 10 million daily deployments at danger, unpatched systems have limited response time.
Free Webinar: Better SOC with Interactive Malware Sandbox for Incident Response and Threat Hunting – Register Here
The post Fluent Bit 0-day Vulnerabilities Exposes Billions of Production Environments to Cyber Attacks appeared first on Cyber Security News.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)

























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)





































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)