New Botnet Dubbed “Eleven11bot” Hacked 30,000 Webcams
A newly identified botnet, tracked as Eleven11bot, has compromised approximately 30,000 internet-connected devices—primarily security cameras and network video recorders (NVRs)—to launch distributed denial-of-service (DDoS) attacks against critical infrastructure. Discovered by Nokia Deepfield’s Emergency Response Team (ERT) on February 26, 2025, the botnet has since been linked to multi-day campaigns targeting telecom providers, gaming platforms, and […] The post New Botnet Dubbed “Eleven11bot” Hacked 30,000 Webcams appeared first on Cyber Security News.

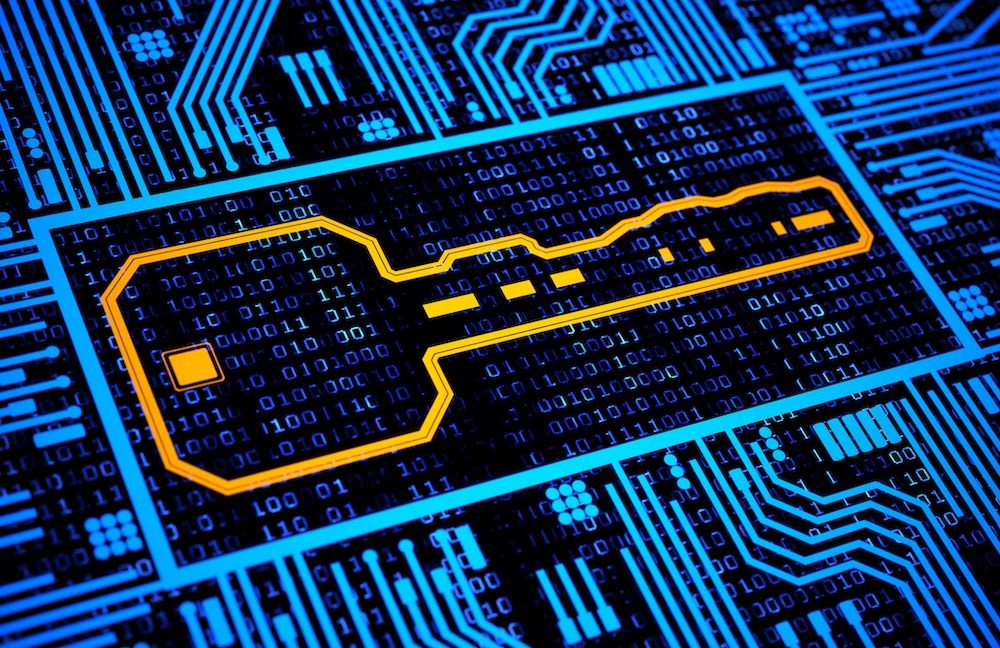
A newly identified botnet, tracked as Eleven11bot, has compromised approximately 30,000 internet-connected devices—primarily security cameras and network video recorders (NVRs)—to launch distributed denial-of-service (DDoS) attacks against critical infrastructure.
Discovered by Nokia Deepfield’s Emergency Response Team (ERT) on February 26, 2025, the botnet has since been linked to multi-day campaigns targeting telecom providers, gaming platforms, and enterprise networks.
Security researcher Jérôme Meyer, who contributed to its analysis, described it as “one of the largest known DDoS botnet campaigns observed since the invasion of Ukraine in February 2022”.
Mirai Variant with HiSilicon Exploit
Eleven11bot is not a standalone botnet but a Mirai variant leveraging a novel exploit against HiSilicon-based IoT devices, particularly those running the TVT-NVMS9000 video management software.
The malware exploits default credentials and unpatched vulnerabilities in firmware to gain control of devices.
Unlike earlier Mirai iterations, Eleven11bot uses a refined scanning algorithm to identify exposed Telnet (Port 23) and SSH (Port 22) services, followed by brute-force attacks using credential dictionaries tailored to IoT manufacturers like VStarcam.
GreyNoise Intelligence analyzed 1,400 IPs associated with the botnet, confirming 1,042 as actively malicious.
Of these, 96% originate from non-spoofable, geolocatable devices, with 61% (636 IPs) traced to Iran.
The botnet’s command-and-control (C2) infrastructure uses encrypted channels to distribute attack payloads, including UDP flood and HTTP/HTTPS amplification vectors, with observed attack intensities ranging from 100,000 to over 500 million packets per second (pps).
Initial reports estimated 86,400 infected devices based on a misinterpreted network signature—“head[…]1111”—detected in traffic logs.
This signature was later attributed to the HiSilicon SDK protocol, a legitimate component of remote device management in white-labeled IoT hardware.
Revised analysis by GreyNoise suggests fewer than 5,000 devices are actively compromised, though the botnet’s concentrated firepower remains significant.
The botnet’s surge coincided with renewed U.S. economic sanctions against Iran on March 5, 2025, though GreyNoise cautions against direct attribution.
Compromised devices in Iran largely belong to residential ISPs and small businesses using outdated firmware.
Eleven11bot’s operators have prioritized targets in the telecommunications sector, with attacks disrupting latency-sensitive services like VoIP and cloud gaming.
Notably, the botnet avoids targeting networks protected by Nokia Deepfield’s Defender platform, which uses real-time traffic analysis to filter malicious payloads.
Meyer emphasized that Deepfield customers were “fully shielded” due to preemptive botnet IP blocklisting and behavioral anomaly detection.
Mitigation Strategies for Organizations
GreyNoise recommends the following actions to counter Eleven11bot and similar threats:
Network-Level Blocking: Deploy firewalls or intrusion prevention systems (IPS) to block traffic from the 1,042 malicious IPs identified by GreyNoise.
IoT Hardening: Disable remote administration, change default credentials, and apply firmware updates for HiSilicon-based devices. The TVT-NVMS9000 software requires immediate patching to CVE-2024-32899 (unauthenticated RCE).
DDoS Mitigation: Enable rate-limiting for UDP/53 (DNS) and UDP/123 (NTP) protocols, and deploy cloud-based scrubbing services during attacks.
Behavioral Monitoring: Use SIEM tools to flag repeated login attempts on Telnet/SSH ports and unexpected outbound traffic from IoT devices.
While Eleven11bot’s initial infection numbers were overstated, its capacity for high-pps DDoS attacks poses a tangible risk to unsecured networks.
The incident underscores the critical need for firmware updates and zero-trust policies in IoT environments.
As researchers continue to monitor the botnet’s 305 actively malicious IPs, organizations are urged to audit their device landscapes and adopt proactive threat-hunting measures.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post New Botnet Dubbed “Eleven11bot” Hacked 30,000 Webcams appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






































































































































































































































.jpg?#)










































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)





















































































































 To Hack Windows Systems.webp?#)



