SolarWinds Web Help Desk Vulnerability Let Hackers Access Stored Passwords – PoC Released
A critical vulnerability in SolarWinds’ Web Help Desk software (CVE-2024-28989) allowed attackers to decrypt sensitive credentials, including database passwords and LDAP/SMTP authentication secrets, through cryptographic weaknesses in its AES-GCM implementation. Patched in version 12.8.5, the flaw stemmed from predictable encryption keys and nonce reuse, enabling practical decryption of stored secrets even without direct system access. […] The post SolarWinds Web Help Desk Vulnerability Let Hackers Access Stored Passwords – PoC Released appeared first on Cyber Security News.
.webp?#)
A critical vulnerability in SolarWinds’ Web Help Desk software (CVE-2024-28989) allowed attackers to decrypt sensitive credentials, including database passwords and LDAP/SMTP authentication secrets, through cryptographic weaknesses in its AES-GCM implementation.
Patched in version 12.8.5, the flaw stemmed from predictable encryption keys and nonce reuse, enabling practical decryption of stored secrets even without direct system access.
Cryptographic Design Flaws in Web Help Desk
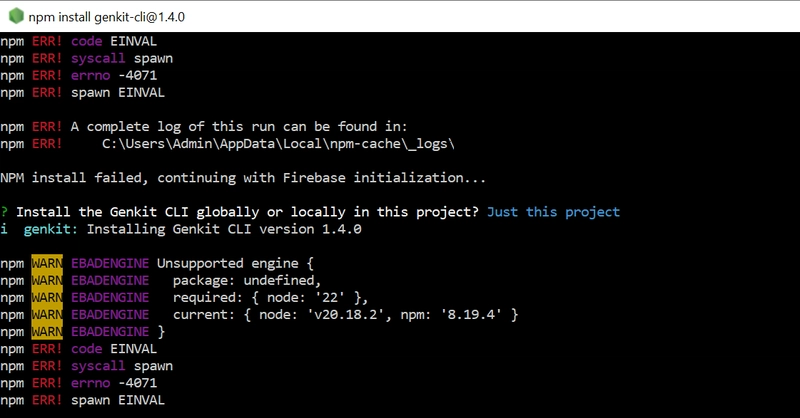
According to NetSPI’s team, the vulnerability resides on the com.solarwinds.whd.symmetric.AESGCMSymetricCryptoProvider class, which managed AES-GCM encryption for credentials stored in database backups and configuration files.
Two primary flaws were identified:
Static and Predictable Encryption Keys:
The default AES-GCM key (defaultKey) was hardcoded in cryptconfig.properties within the whd-crypto.jar file. This allowed trivial decryption of secrets marked as {AES} For example, the embedded PostgreSQL password in .whd.properties used this key:
A second key derivation mechanism compounded the risk. The SecretKeyServiceImpl class generated keys using init_code values from the database XORed with a static hex value (0xBABEFACE).
With init_code typically ranging below 0x10000, brute-forcing became computationally trivial:
AES-GCM’s security relies on unique nonces per encryption. However, Web Help Desk reused nonces across operations, enabling keystream recovery via known plaintext-ciphertext pairs.
Attackers could XOR a known credential (e.g., Password1) with its ciphertext to extract the keystream, then decrypt other secrets encrypted under the same nonce:
Extract Hardcoded Keys: Decompile JAR files to retrieve defaultKey from cryptconfig.properties. For example, decrypting frcLMeS3nchpg_Ucxz… with key 19950 revealed Password1, demonstrating how low entropy keys enabled practical attacks.
During a penetration test, NetSPI’s team decrypted an oauth2_client_secret and LDAP query account password. These granted Azure AD access via Connect-AzAccount and lateral movement capabilities within the network.
Upgrade to v12.8.5: SolarWinds patched the key generation logic and enforced proper nonce randomization. While patching eliminates immediate risks, organizations must adopt defense-in-depth strategies monitoring for credential leaks, segmenting backup storage, and implementing robust key lifecycle management.
As attackers increasingly weaponize cryptographic misconfigurations, proactive hardening of encryption practices becomes indispensable.
The post SolarWinds Web Help Desk Vulnerability Let Hackers Access Stored Passwords – PoC Released appeared first on Cyber Security News. Nonce Reuse and Keystream Recovery
Exploitation Pathways
Brute-Force Transformed Keys: Compute init_code ^ 0xBABEFACE for subscriber IDs (≤ 65,535 possibilities).
Decrypt Secrets: Use derived keys to decrypt AES-GCM ciphertexts from backups or .whd.properties.
Mitigations
Restrict Backup Access: Limit .zip and .properties file permissions to necessary personnel.
Rotate All Embedded Secrets: Reset database passwords, API keys, and LDAP/SMTP credentials post-upgrade.
Audit AES-GCM Usage: Ensure nonces are unique per encryption (e.g., using counter-based or random nonces with 96-bit entropy).
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)


























































.webp?#)

