Hackers Scanning From 24,000 IPs to Gain Access to Palo Alto Networks GlobalProtect Portals
Researchers have detected an alarming surge in malicious scanning activity targeting Palo Alto Networks’ GlobalProtect VPN portals. Over a 30-day period, nearly 24,000 unique IP addresses have attempted to access these critical security gateways, suggesting a coordinated effort to probe network defenses and identify vulnerable systems. The campaign began on March 17, 2025, with activity […] The post Hackers Scanning From 24,000 IPs to Gain Access to Palo Alto Networks GlobalProtect Portals appeared first on Cyber Security News.

Researchers have detected an alarming surge in malicious scanning activity targeting Palo Alto Networks’ GlobalProtect VPN portals.
Over a 30-day period, nearly 24,000 unique IP addresses have attempted to access these critical security gateways, suggesting a coordinated effort to probe network defenses and identify vulnerable systems.
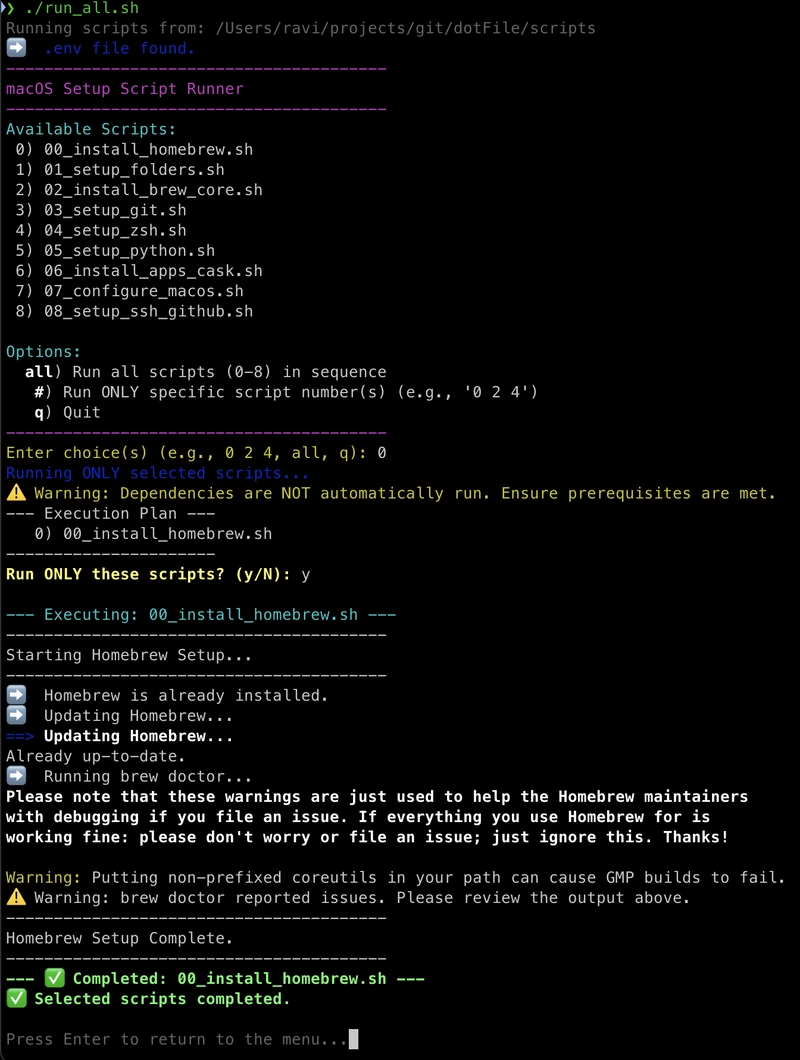
The campaign began on March 17, 2025, with activity rapidly escalating to approximately 20,000 unique IPs per day before tapering off after March 26.
Surge in Suspicious Activity Targeting PAN-OS Devices
GreyNoise has classified most sources (23,800 IPs) as suspicious, with 154 IP addresses definitively tagged as malicious.
“Over the past 18 to 24 months, we’ve observed a consistent pattern of deliberate targeting of older vulnerabilities or well-worn attack and reconnaissance attempts against specific technologies,” explained Bob Rudis, VP of Data Science at GreyNoise.
“These patterns often coincide with new vulnerabilities emerging 2 to 4 weeks later.”
This scanning surge raises significant concerns following the discovery of CVE-2024-3400 last year, a critical command injection vulnerability in PAN-OS GlobalProtect that allowed unauthenticated attackers to execute arbitrary code with root privileges on affected firewalls.
The vulnerability received the maximum CVSS score of 10.0, highlighting its severity.
Through technical analysis, researchers identified three distinct JA4h network fingerprint hashes linked to the login scanner tool:
- po11nn11enus_967778c7bec7_000000000000_000000000000
- po11nn09enus_fb8b2e7e6287_000000000000_000000000000
- po11nn060000_c4f66731b00d_000000000000_000000000000
These fingerprints enable security teams to identify and correlate separate login attempts originating from the same toolkit, even as attackers change their source IPs.
Geographically, the scanning originated predominantly from the United States (16,249 IPs) and Canada (5,823 IPs), with additional sources in Finland, the Netherlands, and Russia. The vast majority targeted systems in the United States (23,768 IPs).
A substantial portion of the traffic (20,010 IPs) has been linked to infrastructure associated with 3xK Tech GmbH under ASN200373, with additional contributions from PureVoltage Hosting Inc., Fast Servers Pty Ltd., and Oy Crea Nova Hosting Solution Ltd.
The activity appears connected to other PAN-OS reconnaissance efforts, with a spike in “PAN-OS Crawler” traffic observed on March 26 involving 2,580 unique source IPs.
Security experts have noted similarities to a 2024 espionage campaign that targeted perimeter network devices.
Organizations using Palo Alto Networks products should immediately review their March logs, implement enhanced monitoring, conduct thorough threat hunting, ensure all security patches are applied, and consider blocking identified malicious IPs.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post Hackers Scanning From 24,000 IPs to Gain Access to Palo Alto Networks GlobalProtect Portals appeared first on Cyber Security News.












































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






















































































































![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)










































































































































_Anthony_Brown_Alamy.jpg?#)
_Hanna_Kuprevich_Alamy.jpg?#)




.png?#)




































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)