Critical Windows Remote Desktop Services Vulnerability Lets Attackers Execute Malicious Code
Microsoft has released its March security update, addressing 57 vulnerabilities across its product range, including six critical flaws. Among the critical vulnerabilities are CVE-2025-24035 and CVE-2025-24045, both Remote Code Execution (RCE) vulnerabilities in Windows Remote Desktop Services (RDS). Each vulnerability has been assigned a CVSSv3 score of 8.1 and is rated as critical. Windows Remote […] The post Critical Windows Remote Desktop Services Vulnerability Lets Attackers Execute Malicious Code appeared first on Cyber Security News.

Microsoft has released its March security update, addressing 57 vulnerabilities across its product range, including six critical flaws.
Among the critical vulnerabilities are CVE-2025-24035 and CVE-2025-24045, both Remote Code Execution (RCE) vulnerabilities in Windows Remote Desktop Services (RDS). Each vulnerability has been assigned a CVSSv3 score of 8.1 and is rated as critical.
Windows Remote Desktop Services enables users to remotely access Windows applications and desktops from different devices via a network connection.
CVE-2025-24035 is caused by sensitive data storage in improperly locked memory. CVE-2025-24045 is a more complex vulnerability to exploit, requiring an attacker to win a race condition.
An attacker must win a race condition to exploit either of these flaws successfully. Despite this requirement, Microsoft has assessed both flaws as “Exploitation More Likely.”
Successful exploitation of these vulnerabilities could allow an unauthorized attacker to execute code over a network, potentially leading to complete system compromise with high-severity impacts on system confidentiality, integrity, and availability. The vulnerability affects multiple Windows server and desktop versions, making it a widespread risk.
Microsoft has released patches for these vulnerabilities as part of its March Patch Tuesday update7. Users and organizations are advised to apply the updates as soon as possible to mitigate the risk.
In addition to the RDS vulnerabilities, the March update addresses other critical flaws, including:
- CVE-2025-26645: A remote code execution vulnerability in the Remote Desktop Client that allows an unauthorized attacker to execute code over a network via relative path traversal when a vulnerable client connects to a malicious Remote Desktop Protocol (RDP) server.
- CVE-2025-24057: A heap-based buffer overflow in Microsoft Office that could allow an unauthorized attacker to execute code remotely.
- CVE-2025-24064: A use-after-free flaw in Windows DNS Server that may allow an unauthorized attacker to execute code over a network.
- CVE-2025-24084: A remote code execution vulnerability in Windows Subsystem for Linux kernel.
Microsoft has also addressed six vulnerabilities that have been actively exploited in the wild. These include vulnerabilities in Microsoft Management Console, Windows NTFS, and Windows Fast FAT system drivers.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Critical Windows Remote Desktop Services Vulnerability Lets Attackers Execute Malicious Code appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






































































































































































































































.jpg?#)










































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

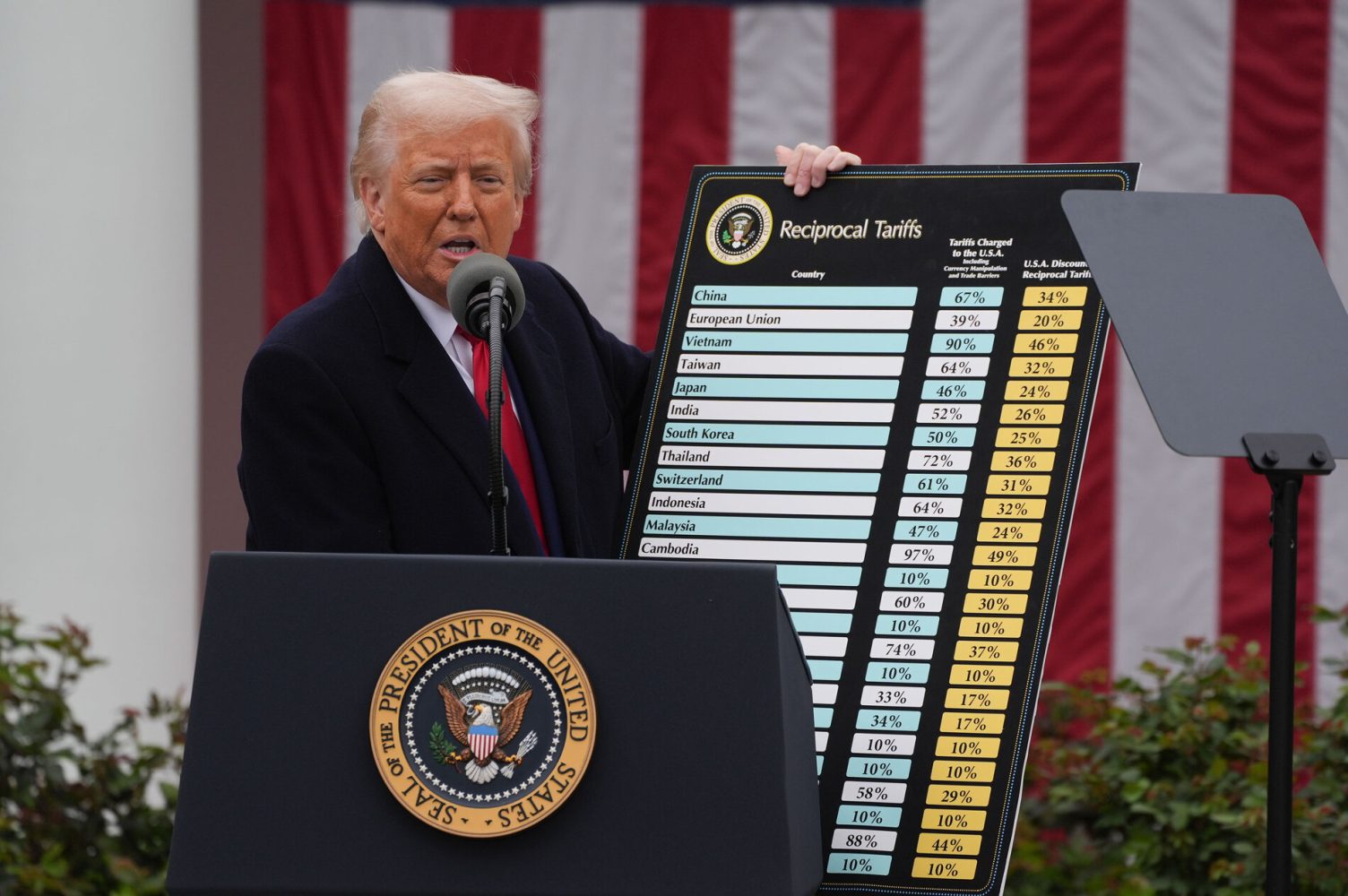
![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)