What is a Software-defined Perimeter?
As cyber threats evolve and businesses embrace cloud-based and remote work environments, traditional security models like VPNs are proving insufficient. Software-Defined Perimeter (SDP) is an advanced security framework designed to control access dynamically, reducing the attack surface and ensuring that only authorized users can access specific network resources. What is Software-Defined Perimeter (SDP)? SDP is a security framework that enforces strict access controls based on user identity and device security posture. Unlike traditional network security models that grant broad access once a user is authenticated, SDP operates on a Zero Trust principle—meaning no one is trusted by default, and access is granted only after thorough verification. By using software-defined rules instead of hardware-based perimeters, SDP ensures that network infrastructure remains hidden from unauthorized users. Even if an attacker manages to breach part of the system, they cannot move laterally across the network since they are only granted access to specific applications instead of the entire network. How Does SDP Work? SDP relies on three core components to ensure secure access: End Device: The user's device (laptop, phone, or tablet) must install a client that authenticates and verifies the device before granting access. SDP Controller: This acts as the security gatekeeper, validating user identity, checking device security posture, and determining access permissions. SDP Gateway: If authentication is successful, this gateway creates an encrypted one-to-one connection between the user and the required application, ensuring a secure, invisible pathway. Key Benefits of SDP 1. Stronger Security with Zero Trust Unlike VPNs, which assume trust after authentication, SDP ensures every request is verified before granting access. This minimizes unauthorized access risks and prevents lateral movement within the network. 2. Reduced Attack Surface With SDP, network resources remain invisible to unauthorized users, making it significantly harder for attackers to locate and target sensitive systems. 3. Seamless Multi-Cloud Protection SDP is ideal for businesses using multiple cloud services, ensuring secure access across AWS, Azure, Google Cloud, and private data centers without relying on complex network configurations. 4. Simplified Remote Access As companies move toward hybrid work models, SDP provides secure, seamless access for remote employees without the performance bottlenecks and security risks of traditional VPNs. 5. Better Control Over Third-Party Access Organizations can define granular access controls, ensuring external vendors and contractors only access the specific applications they need—without exposing the broader network. Why SDP is Replacing VPNs While VPNs were once the go-to remote access solution, they lack granular control and expose the entire network to authenticated users. SDP, in contrast, operates with least privilege access, isolates applications, and minimizes risks. It also scales effortlessly, making it a better fit for modern cloud-driven enterprises. Final Thoughts As cyber threats grow more sophisticated, businesses must rethink traditional security approaches. SDP provides stronger, more flexible, and scalable access control, reducing vulnerabilities while improving performance. Adopting SDP enhances security, simplifies access management, and ensures that organizations stay ahead in a cloud-first world.
As cyber threats evolve and businesses embrace cloud-based and remote work environments, traditional security models like VPNs are proving insufficient. Software-Defined Perimeter (SDP) is an advanced security framework designed to control access dynamically, reducing the attack surface and ensuring that only authorized users can access specific network resources.
What is Software-Defined Perimeter (SDP)?
SDP is a security framework that enforces strict access controls based on user identity and device security posture. Unlike traditional network security models that grant broad access once a user is authenticated, SDP operates on a Zero Trust principle—meaning no one is trusted by default, and access is granted only after thorough verification.
By using software-defined rules instead of hardware-based perimeters, SDP ensures that network infrastructure remains hidden from unauthorized users. Even if an attacker manages to breach part of the system, they cannot move laterally across the network since they are only granted access to specific applications instead of the entire network.
How Does SDP Work?
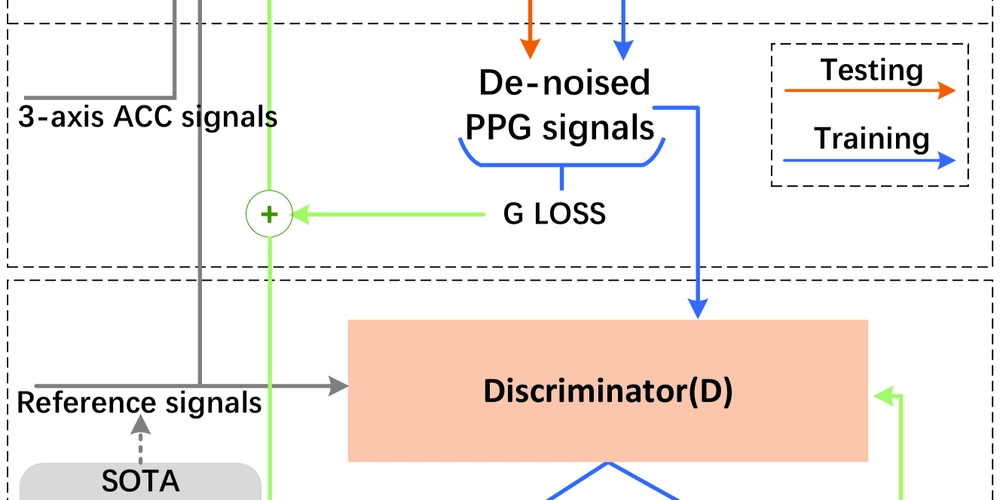
SDP relies on three core components to ensure secure access:
- End Device: The user's device (laptop, phone, or tablet) must install a client that authenticates and verifies the device before granting access.
- SDP Controller: This acts as the security gatekeeper, validating user identity, checking device security posture, and determining access permissions.
- SDP Gateway: If authentication is successful, this gateway creates an encrypted one-to-one connection between the user and the required application, ensuring a secure, invisible pathway.
Key Benefits of SDP
1. Stronger Security with Zero Trust
Unlike VPNs, which assume trust after authentication, SDP ensures every request is verified before granting access. This minimizes unauthorized access risks and prevents lateral movement within the network.
2. Reduced Attack Surface
With SDP, network resources remain invisible to unauthorized users, making it significantly harder for attackers to locate and target sensitive systems.
3. Seamless Multi-Cloud Protection
SDP is ideal for businesses using multiple cloud services, ensuring secure access across AWS, Azure, Google Cloud, and private data centers without relying on complex network configurations.
4. Simplified Remote Access
As companies move toward hybrid work models, SDP provides secure, seamless access for remote employees without the performance bottlenecks and security risks of traditional VPNs.
5. Better Control Over Third-Party Access
Organizations can define granular access controls, ensuring external vendors and contractors only access the specific applications they need—without exposing the broader network.
Why SDP is Replacing VPNs
While VPNs were once the go-to remote access solution, they lack granular control and expose the entire network to authenticated users. SDP, in contrast, operates with least privilege access, isolates applications, and minimizes risks. It also scales effortlessly, making it a better fit for modern cloud-driven enterprises.
Final Thoughts
As cyber threats grow more sophisticated, businesses must rethink traditional security approaches. SDP provides stronger, more flexible, and scalable access control, reducing vulnerabilities while improving performance. Adopting SDP enhances security, simplifies access management, and ensures that organizations stay ahead in a cloud-first world.










































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)




.jpg?#)































_Christophe_Coat_Alamy.jpg?#)






































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)