Splunk Dashboards
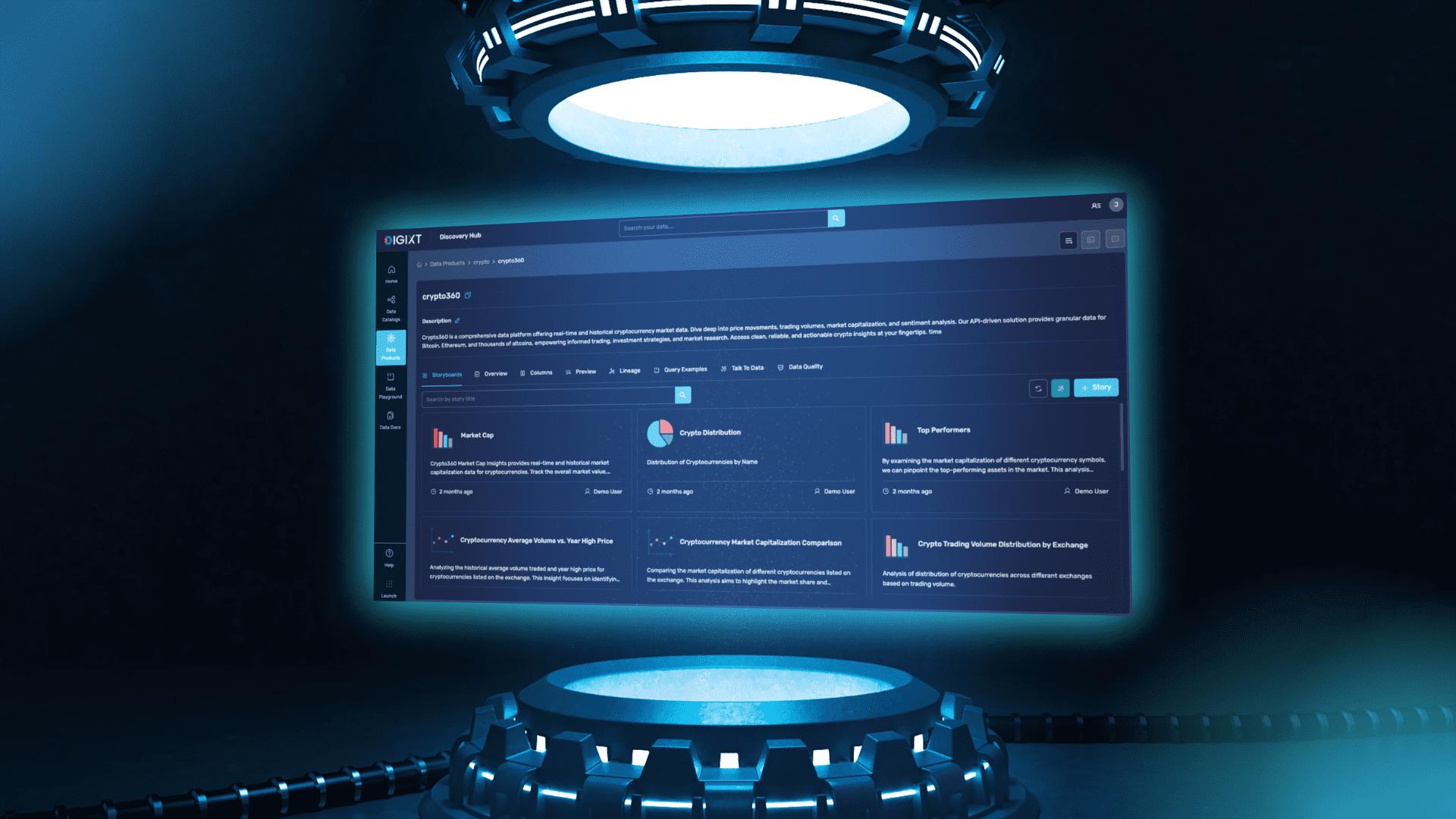
I created these dashboards for splunk to detect some attacks: Apache Error Log Monitoring Dashboard Apache Error Log Monitoring Dashboard Monitors Apache error logs for potential security events and path traversal attempts Amount Of Errors Over Time source="/var/log/apache2/error.log" sourcetype="apache_error" | eval mytime=strftime(_time,"%Y-%m-%d %H:%M") | stats count as error_count by mytime | sort -error_count -24h now pie none Error Activity Over Time source="/var/log/apache2/error.log" sourcetype="apache_error" | timechart span=5m count by host -24h now line none bottom Path Traversal Attempts source="/var/log/apache2/error.log" sourcetype="apache_error" "AH00126: Invalid URI" OR "/../" OR ".." OR "%2E%2E" | rex field=_raw "GET (?[^ ]+) HTTP" | table _time client request_path | sort -_time -24h now none Admin Page Probing source="/var/log/apache2/error.log" sourcetype="apache_error" "admin" OR "administrator" OR "login" OR "cp" OR "controlpanel" | rex field=_raw "script '(?[^']+)'" | stats count by requested_script | sort -count -24h now bar none default bottom Top Client IPs source="/var/log/apache2/error.log" sourcetype="apache_error" | rex field=_raw "\[client (?[^\:]+)\:(?\d+)\]" | stats count by client_ip | sort -count -24h now column none Process IDs with Errors source="/var/log/apache2/error.log" sourcetype="apache_error" | rex field=_raw "\[pid (?\d+)\]" | stats count by process_id | sort -count -24h now pie none Recent Critical Events source="/var/log/apache2/error.log" sourcetype="apache_error" "Invalid URI" OR "/etc/shadow" OR "/etc/passwd" OR "../" OR "%2E%2E" OR "/.." | rex field=_raw "GET (?[^ ]+)" | rex field=_raw "\[client (?[^\:]+)\:(?\d+)\]" | table _time client_ip request_path | sort -_time -24h now 10 none Search for Suspicious Activity Search Term shadow source="/var/log/apache2/error.log" sourcetype="apache_error" "$search_term$" | table _time _raw | sort -_time -24h now 5 none Path Traversal Attempts Path Traversal Attempts Top Missing Scripts index=main sourcetype=apache_error "not found or unable to stat" | rex field=_raw "script '(?[^']+)' not found" | stats count by script_path | sort -count bar right 250 Path Traversal Attempts index=main sourcetype=apache_error "Invalid URI" | regex _raw="(\.\./){2,}" | stats count by host, source, _time | sort -_time column 250 Recent PHP Errors index=main sourcetype=apache_error "php7:error" | rex field=_raw "script '(?[^']+)' not found" | table _time, script, client, host 10 Uncommon Events index=main sourcetype=apache_error | rare _raw | table _time, _raw 10 SSH Brute Force Attack Dashboard SSH Brute Force Attack Dashboard Monitor and detect SSH brute force activities in real time SSH Login Attempts Over Time index=* sourcetype="auth" | search "ssh*" AND ("Failed password" OR "authentication failure" OR "Invalid user") | bucket span=1m _time | stats count as login_attempts by _time -24h@h now line Top Attacking IPs index=* sourcetype="auth" | search "ssh*" AND ("Failed password" OR "authentication failure" OR "Invalid user") | eval src_ip=coalesce(src_ip, source_ip, src, clientip, rhost) | stats count by src_ip | sort -count | head 10 -24h@h now bar
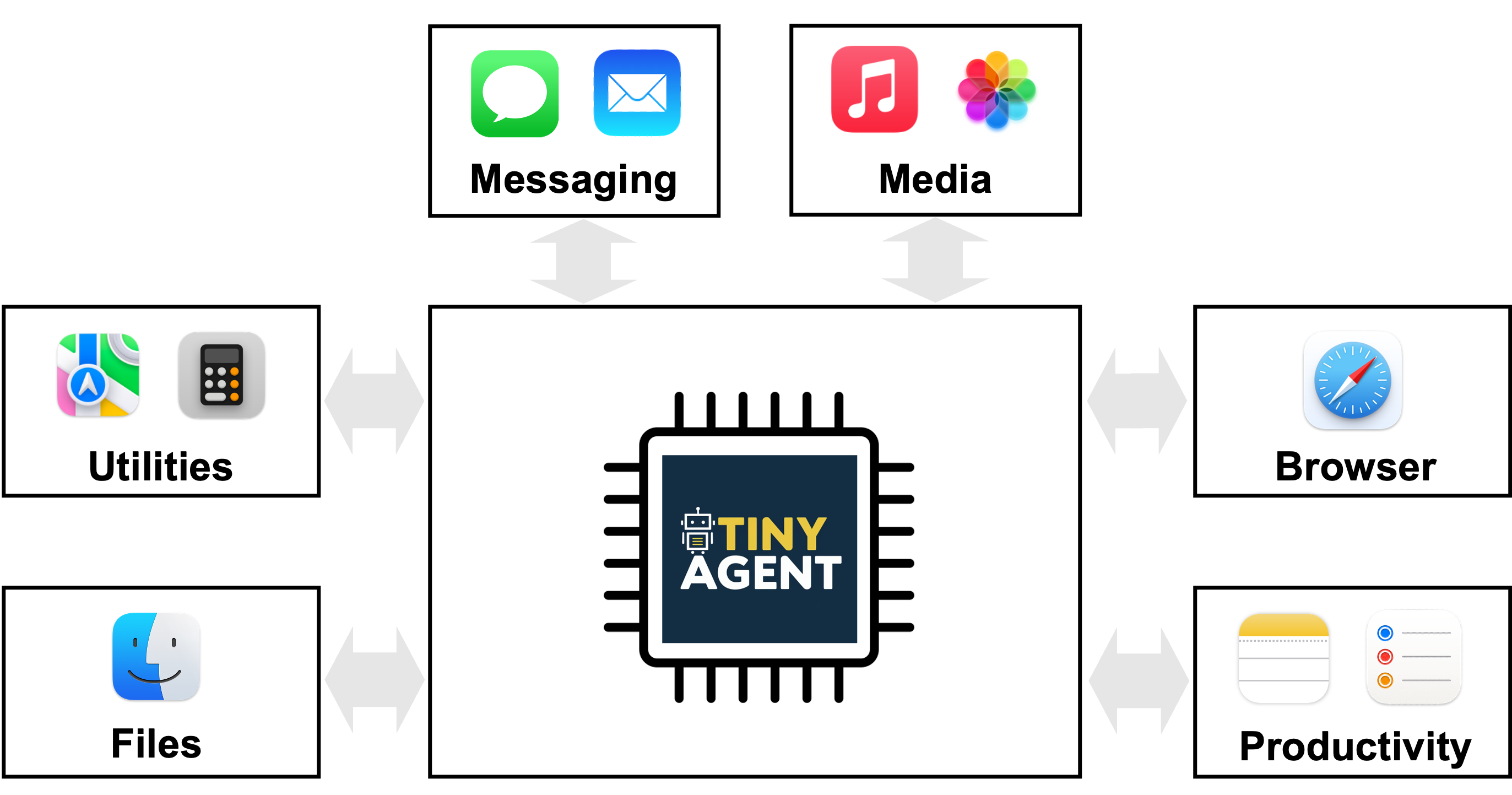
I created these dashboards for splunk to detect some attacks:
Apache Error Log Monitoring Dashboard
version="1.1" theme="dark">
Apache Error Log Monitoring Dashboard
submitButton="false" autoRun="true">
|
</span>Amount Of Errors Over Time<span class="nt">
name="charting.chart">pie
name="charting.drilldown">none
</span>Error Activity Over Time<span class="nt">
name="charting.chart">line
name="charting.drilldown">none
name="charting.legend.placement">bottom
|
</span>Path Traversal Attempts<span class="nt">
name="drilldown">none
|
</span>Admin Page Probing<span class="nt">
name="charting.chart">bar
name="charting.drilldown">none
name="charting.chart.stackMode">default
name="charting.legend.placement">bottom
|
</span>Top Client IPs<span class="nt">
name="charting.chart">column
name="charting.drilldown">none
</span>Process IDs with Errors<span class="nt">
name="charting.chart">pie
name="charting.drilldown">none
|
</span>Recent Critical Events<span class="nt">
name="count">10
name="drilldown">none
|
</span>Search for Suspicious Activity<span class="nt">
type="text" token="search_term" searchWhenChanged="true">
Search Term
name="count">5
name="drilldown">none
Path Traversal Attempts
version="1.1" theme="dark">
Path Traversal Attempts
|
</span>Top Missing Scripts<span class="nt">
name="charting.chart">bar
name="charting.legend.placement">right
name="height">250
</span>Path Traversal Attempts<span class="nt">
name="charting.chart">column
name="height">250
|
</span>Recent PHP Errors<span class="nt">
name="count">10
</span>Uncommon Events<span class="nt">
name="count">10
SSH Brute Force Attack Dashboard
version="1.1" theme="light">
SSH Brute Force Attack Dashboard
|
</span>SSH Login Attempts Over Time<span class="nt">
name="charting.chart">line
</span>Top Attacking IPs<span class="nt">
name="charting.chart">bar
|
</span>Top Targeted Usernames<span class="nt">
name="charting.chart">pie
</span>Success vs Failure Attempts<span class="nt">
name="charting.chart">pie
|
</span>Detailed SSH Brute Force Attempts<span class="nt">


















































































































































![[The AI Show Episode 145]: OpenAI Releases o3 and o4-mini, AI Is Causing “Quiet Layoffs,” Executive Order on Youth AI Education & GPT-4o’s Controversial Update](https://www.marketingaiinstitute.com/hubfs/ep%20145%20cover.png)






















































































![[FREE EBOOKS] Learn Computer Forensics — 2nd edition, AI and Business Rule Engines for Excel Power Users & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)





![From Art School Drop-out to Microsoft Engineer with Shashi Lo [Podcast #170]](https://cdn.hashnode.com/res/hashnode/image/upload/v1746203291209/439bf16b-c820-4fe8-b69e-94d80533b2df.png?#)


























































































(1).jpg?#)






























_Inge_Johnsson-Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale#)


































































































![Apple to Split iPhone Launches Across Fall and Spring in Major Shakeup [Report]](https://www.iclarified.com/images/news/97211/97211/97211-640.jpg)
![Apple to Move Camera to Top Left, Hide Face ID Under Display in iPhone 18 Pro Redesign [Report]](https://www.iclarified.com/images/news/97212/97212/97212-640.jpg)
![Apple Developing Battery Case for iPhone 17 Air Amid Battery Life Concerns [Report]](https://www.iclarified.com/images/news/97208/97208/97208-640.jpg)
![AirPods 4 On Sale for $99 [Lowest Price Ever]](https://www.iclarified.com/images/news/97206/97206/97206-640.jpg)



























![[Updated] Samsung’s 65-inch 4K Smart TV Just Crashed to $299 — That’s Cheaper Than an iPad](https://www.androidheadlines.com/wp-content/uploads/2025/05/samsung-du7200.jpg)