Practical GraphQL Scanning: Modern API Attack Surface Under the Microscope
GraphQL APIs offer flexibility and efficiency — but that same flexibility often introduces security blind spots. Unlike traditional REST, GraphQL exposes an entire query language to the client — and thus to attackers. This post walks through a practical GraphQL security testing workflow using Burp Suite + community tools, with a focus on precision, stealth, and clarity. 1. Reconnaissance: Is It GraphQL? Look for signs like: Endpoints like /graphql, /api/graphql, /gql Content-Type: application/json POST requests with query fields in body Example: { "query": "{ __typename }" } A successful response with HTTP 200 and a "data" field confirms GraphQL is live. 2. Introspection Enabled? Send the classic introspection query: { "query": "{ __schema { types { name } } }" } If enabled, it reveals the full schema — including queries, mutations, and types. You can also use tools like: python3 graphql-introspection.py -u https://target.com/graphql Or Burp extension: GraphQL Raider 3. Use Burp GraphQL Raider Extension Install via: Burp → BApp Store → GraphQL Raider Capabilities: Visual query builder Introspection analysis Auto fuzzing Token replacement Send any GraphQL POST to Repeater → "Send to GraphQL Raider" 4. Attack Vectors Now that you understand the schema, focus on key attack classes: ① Excessive Data Exposure query { users { id email passwordHash } } ② Broken Access Control Try sending the same query as a different role or unauthenticated. Check if sensitive objects are still returned. ③ Injection Attacks While SQL injection is rare in well-configured resolvers, try: query { search(term: "\" OR \"1\"=\"1") } Also test for: NoSQLi (Mongo-style payloads) SSTI (in template-powered GraphQL backends) ④ Denial of Service (DoS) Use deeply nested recursive queries: query { a { a { a { a { a { a } } } } } } Some servers crash or timeout. 5. Automated Scanning (Optional) GraphQL endpoints can be integrated into active scanning tools, but be cautious with rate-limiting and introspection-heavy payloads. Recommended: Manual + Raider for schema-aware fuzzing Intruder for token/session tests Passive detection of disclosure/misconfig 6. Defensive Tips (Bonus) If you're defending a GraphQL API: Disable introspection in production Apply query depth and complexity limiting Enforce RBAC on fields, not just endpoints Log and rate-limit abusive patterns Final Notes GraphQL flips the security model: the client controls the query shape. This demands fine-grained testing, schema awareness, and thoughtful payload design. In upcoming posts: Bypassing depth limits Field-level access control fuzzing Using GraphQL Voyager for visualization and mapping Understand the graph. Map the logic. Exploit the edges.
GraphQL APIs offer flexibility and efficiency — but that same flexibility often introduces security blind spots.
Unlike traditional REST, GraphQL exposes an entire query language to the client — and thus to attackers.
This post walks through a practical GraphQL security testing workflow using Burp Suite + community tools, with a focus on precision, stealth, and clarity.
1. Reconnaissance: Is It GraphQL?
Look for signs like:
- Endpoints like
/graphql,/api/graphql,/gql - Content-Type:
application/json - POST requests with
queryfields in body
Example:
{
"query": "{ __typename }"
}
A successful response with HTTP 200 and a "data" field confirms GraphQL is live.
2. Introspection Enabled?
Send the classic introspection query:
{
"query": "{ __schema { types { name } } }"
}
If enabled, it reveals the full schema — including queries, mutations, and types.
You can also use tools like:
python3 graphql-introspection.py -u https://target.com/graphql
Or Burp extension: GraphQL Raider
3. Use Burp GraphQL Raider Extension
Install via:
Burp → BApp Store → GraphQL Raider
Capabilities:
- Visual query builder
- Introspection analysis
- Auto fuzzing
- Token replacement
Send any GraphQL POST to Repeater → "Send to GraphQL Raider"
4. Attack Vectors
Now that you understand the schema, focus on key attack classes:
① Excessive Data Exposure
query {
users {
id
email
passwordHash
}
}
② Broken Access Control
Try sending the same query as a different role or unauthenticated.
Check if sensitive objects are still returned.
③ Injection Attacks
While SQL injection is rare in well-configured resolvers, try:
query {
search(term: "\" OR \"1\"=\"1")
}
Also test for:
- NoSQLi (Mongo-style payloads)
- SSTI (in template-powered GraphQL backends)
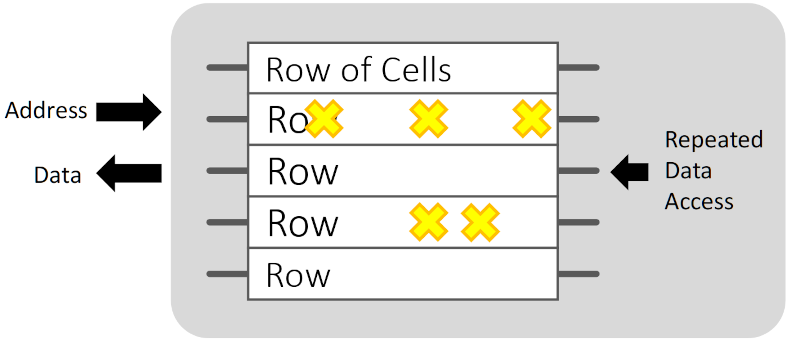
④ Denial of Service (DoS)
Use deeply nested recursive queries:
query {
a { a { a { a { a { a } } } } }
}
Some servers crash or timeout.
5. Automated Scanning (Optional)
GraphQL endpoints can be integrated into active scanning tools, but be cautious with rate-limiting and introspection-heavy payloads.
Recommended:
- Manual + Raider for schema-aware fuzzing
- Intruder for token/session tests
- Passive detection of disclosure/misconfig
6. Defensive Tips (Bonus)
If you're defending a GraphQL API:
- Disable introspection in production
- Apply query depth and complexity limiting
- Enforce RBAC on fields, not just endpoints
- Log and rate-limit abusive patterns
Final Notes
GraphQL flips the security model: the client controls the query shape.
This demands fine-grained testing, schema awareness, and thoughtful payload design.
In upcoming posts:
- Bypassing depth limits
- Field-level access control fuzzing
- Using GraphQL Voyager for visualization and mapping
Understand the graph. Map the logic. Exploit the edges.











































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)








































































































































_Anthony_Brown_Alamy.jpg?#)
_Hanna_Kuprevich_Alamy.jpg?#)




.png?#)

















































































![Hands-on: We got to play Nintendo Switch 2 for nearly six hours yesterday [Video]](https://i0.wp.com/9to5toys.com/wp-content/uploads/sites/5/2025/04/Switch-FI-.jpg.jpg?resize=1200%2C628&ssl=1)
![Fitbit redesigns Water stats and logging on Android, iOS [U]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2023/03/fitbit-logo-2.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)













![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)