How to Track Advanced Persistent Threats (APT) Using Threat Intelligence Lookup Tool
An Advanced Persistent Threat (APT) is a sophisticated and stealthy cyberattack designed to gain unauthorized, long-term access to a target’s network. These attacks are meticulously planned and executed by highly skilled threat actors, often state-sponsored groups or organized crime syndicates, to steal sensitive data, conduct espionage, or disrupt operations. Technical Breakdown of APTs Stages of […] The post How to Track Advanced Persistent Threats (APT) Using Threat Intelligence Lookup Tool appeared first on Cyber Security News.

An Advanced Persistent Threat (APT) is a sophisticated and stealthy cyberattack designed to gain unauthorized, long-term access to a target’s network.
These attacks are meticulously planned and executed by highly skilled threat actors, often state-sponsored groups or organized crime syndicates, to steal sensitive data, conduct espionage, or disrupt operations.
Technical Breakdown of APTs
- Advanced Techniques: APTs employ cutting-edge methods such as custom malware, zero-day exploits, and social engineering to infiltrate networks. Attackers continuously adapt their tools to evade detection.
- Persistence: The attackers aim to remain undetected for extended periods, sometimes months or years, by creating multiple backdoors and redundant entry points.
- Targeted Approach: APTs focus on high-value targets like government agencies, critical infrastructure, and large corporations with sensitive data.
Stages of an APT Attack
Here is the information presented in a table format for clarity:
Stage Description Reconnaissance – Attackers gather intelligence on the target using open-source intelligence (OSINT), social media, and network scanning.
– They identify vulnerabilities in software, hardware, or human behavior.Initial Compromise – Common methods include spear phishing emails containing malicious links or attachments.
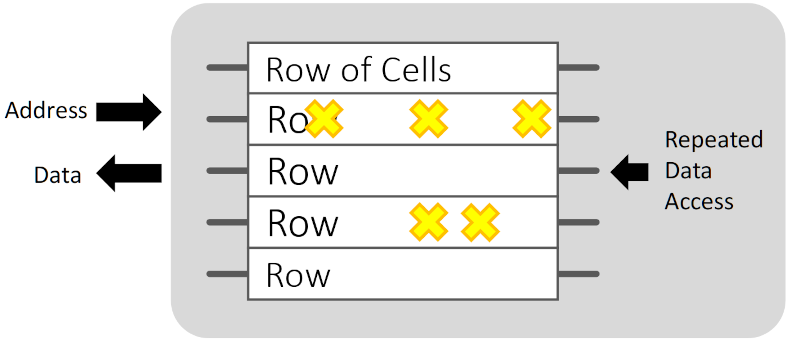
– Exploitation of zero-day vulnerabilities or watering hole attacks (compromising websites frequented by the target).Establishing a Foothold – Attackers deploy malware to create backdoors or tunnels for undetected movement within the network.
– Credential theft through keylogging or phishing enables lateral movement.Privilege Escalation – Attackers gain administrative rights using password cracking or exploiting vulnerabilities.
– This allows them broader control over systems and deeper access to sensitive data.Lateral Movement – Once inside the network, attackers map its structure and move across systems to identify valuable assets.
– Command-and-control (C2) servers are used to manage compromised systems remotely.Data Exfiltration – Sensitive data is collected, encrypted, and transferred to external servers controlled by the attackers.
– Stealth techniques like encrypted communication channels are used to avoid detection.Sustained Presence – Attackers ensure long-term access by installing additional backdoors and evasion mechanisms.
– They may remain dormant for periods to avoid triggering alarms.
Techniques Used
- Spear Phishing: Highly targeted emails designed to deceive individuals into executing malicious code.
- Zero-Day Exploits: Exploitation of unknown software vulnerabilities before patches are available.
- Watering Hole Attacks: Infecting websites frequently visited by the target group.
- Supply Chain Attacks: Compromising third-party vendors or software updates to infiltrate the target’s network.
- Evasion Tactics: Using legitimate tools, code obfuscation, and anti-forensic measures to bypass detection systems.
Why APTs Are Dangerous
Long-Term Impact: The extended dwell time often months allows attackers ample opportunity to steal data or sabotage operations without immediate detection.
High-Level Targets: APTs often focus on critical sectors like defense, finance, energy, healthcare, and technology, where breaches can have national or global consequences.
Resource Intensive: These attacks are backed by significant funding and expertise, making them difficult to counter with conventional security measures.
Collect intelligence on active APTs with ANY.RUN’s TI Lookup - Get free requests to test it
The Power of Threat Intelligence Lookup
ANY.RUN’s Threat Intelligence Lookup: A Powerful Tool for Tracking APTs
Cybersecurity researchers and analysts now have a robust tool to enhance their threat-hunting capabilities with ANY.RUN’s Threat Intelligence (TI) Lookup.
This state-of-the-art search engine allows users to query an extensive database of malware indicators and attack patterns, leveraging over 40 search parameters to extract actionable intelligence.
Designed for threat researchers, SOC teams, and security professionals, TI Lookup provides detailed insights into Indicators of Compromise (IOCs), malware behaviors, and attack methodologies.
With millions of analyzed malware and phishing samples, the database serves as a vital resource for detecting, preventing, and mitigating cyber threats, including Advanced Persistent Threats (APTs).
How TI Lookup Helps Track APTs
APT41 (Wicked Panda): Exploiting Registry Keys for Persistence
Recent investigations into APT41, a China-based cyber espionage group, reveal its use of a PowerShell backdoor to infiltrate systems.
The attack chain involves modifying a Windows registry entry (HKCU\Environment\UserInitMprLogonScript), allowing malicious code execution during user logins.
Additionally, APT41 abuses Microsoft’s forfiles.exe utility, enabling stealthy execution of their payloads. This behavior can be identified using a TI Lookup query:
registryKey:"HKEY_CURRENT_USER\ENVIRONMENT" AND registryValue:"forfiles.exe" AND
threatName:"backdoor" AND registryName:"USERINITMPRLOGONSCRIPT"
Analysts can use this search to identify associated IOCs such as file hashes or mutexes, enabling proactive threat detection and response.

MuddyWater APT: Tracking Backdoor Operations via Mutexes
The MuddyWater APT group, linked to Iran, employs a unique technique to establish persistence using mutexes in their BugSleep backdoor. The malware is typically deployed via phishing emails, after which it creates a mutex and decrypts its configuration to connect to command-and-control (C2) servers.
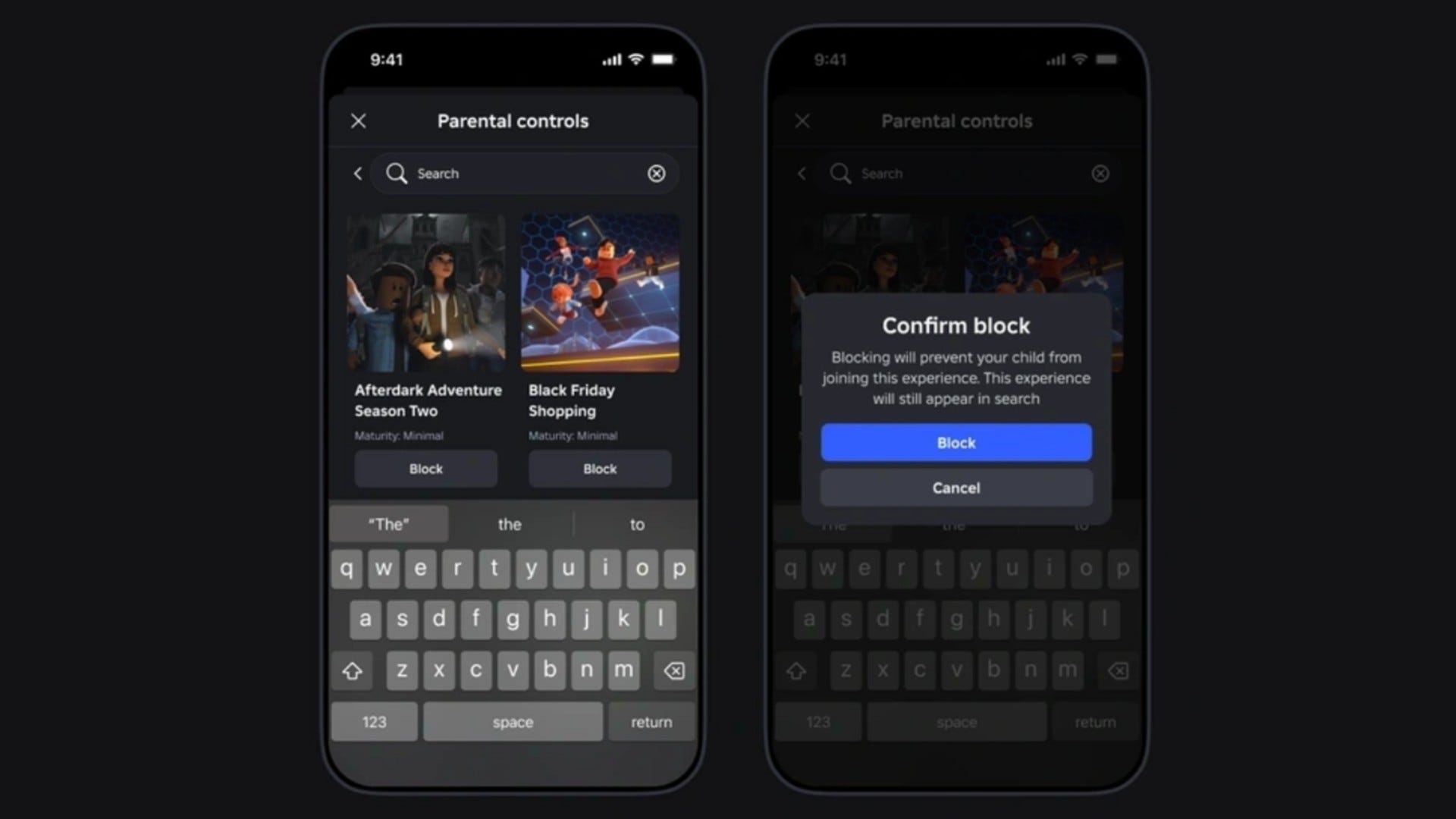
Security teams can detect MuddyWater infections by searching for these mutexes in TI Lookup:
.webp)
(syncObjectName:"PackageManager" OR syncObjectName:"DocumentUpdater")
AND syncObjectOperation:"Create" AND threatName:"muddywater"
By analyzing sandbox session related to these mutexes, security teams can further investigate BugSleep’s behavior and identify new malware variants.

Lazarus Group: North Korea’s Persistent Cyber Threat
Among the most prolific APT groups, Lazarus, attributed to North Korea, has been responsible for multiple cyber espionage campaigns. Recently, the group engaged in fake job interview schemes targeting tech professionals to distribute malware.

Using TI Lookup, researchers can monitor Lazarus-related indicators with a simple query:
threatName:"lazarus"Furthermore, TI Lookup offers a subscription feature, allowing analysts to receive real-time notifications whenever new samples related to specific threats emerge in the database.
Empowering Threat Intelligence with TI Lookup
ANY.RUN’s TI Lookup continues to provide cutting-edge cybersecurity intelligence, enabling security professionals to track, analyze, and respond to emerging threats. With detailed sandbox analyses, real-time updates, and extensive threat hunting capabilities, the platform enhances APT tracking and threat mitigation across industries.











































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)








































































































































_Anthony_Brown_Alamy.jpg?#)
_Hanna_Kuprevich_Alamy.jpg?#)




.png?#)

















































































![Hands-on: We got to play Nintendo Switch 2 for nearly six hours yesterday [Video]](https://i0.wp.com/9to5toys.com/wp-content/uploads/sites/5/2025/04/Switch-FI-.jpg.jpg?resize=1200%2C628&ssl=1)
![Fitbit redesigns Water stats and logging on Android, iOS [U]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2023/03/fitbit-logo-2.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)













![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)