Fortinet Addresses Multiple Vulnerabilities in Major Security Update
Fortinet has rolled out critical security updates to address multiple high-risk flaws across its product portfolio, including FortiOS, FortiProxy, FortiManager, and FortiAnalyzer. Fortinet warns of an already patched zero-day flaw (CVE-2024-55591 & new CVE-2025-24472), which allows attackers to bypass authentication and gain “super-admin” privileges on affected devices. Critical Zero-Day Exploited Since November 2024 The most […] The post Fortinet Addresses Multiple Vulnerabilities in Major Security Update appeared first on Cyber Security News.

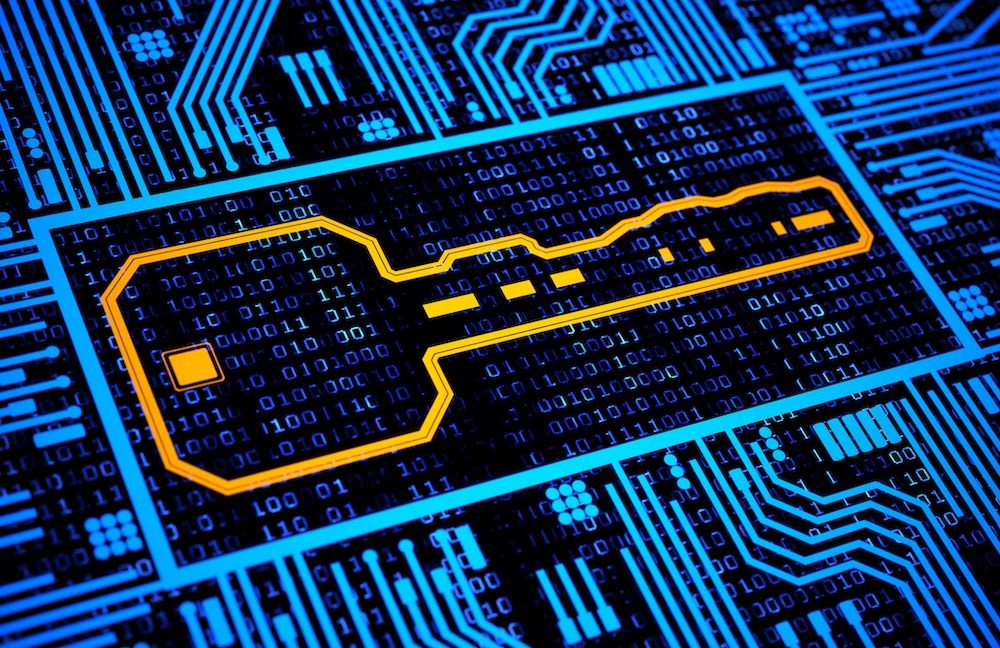
Fortinet has rolled out critical security updates to address multiple high-risk flaws across its product portfolio, including FortiOS, FortiProxy, FortiManager, and FortiAnalyzer.
Fortinet warns of an already patched zero-day flaw (CVE-2024-55591 & new CVE-2025-24472), which allows attackers to bypass authentication and gain “super-admin” privileges on affected devices.
Critical Zero-Day Exploited Since November 2024
The most urgent patch resolves CVE-2024-55591 & new CVE-2025-24472 (CVSS 9.6), an authentication bypass vulnerability in FortiOS and FortiProxy.
Attackers exploit this flaw by sending crafted requests to the Node.js websocket module, enabling unauthorized administrative access, account creation, SSL VPN configuration changes, and lateral movement within networks.
Arctic Wolf researchers first observed exploitation activity in mid-November 2024, with attacks targeting internet-exposed FortiGate firewall management interfaces.
With the update Fortinet acknowledged the CSRF vulnerability associated and added CVE.
Affected versions include:
- FortiOS 7.0.0 through 7.0.16 (fixed in 7.0.17+)
- FortiProxy 7.0.0 through 7.0.19 (fixed in 7.0.20+)
- FortiProxy 7.2.0 through 7.2.12 (fixed in 7.2.13+)
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added this flaw to its Known Exploited Vulnerabilities (KEV) catalog, mandating federal agencies to patch by January 21, 2025.
Additional High and Medium-Severity Vulnerabilities
The updates address 15+ vulnerabilities across Fortinet’s ecosystem, including:
Here’s a consolidated table of the 15 vulnerabilities addressed in Fortinet’s security updates based on the provided search results:
CVE ID Severity CVSS Affected Products Vulnerability Description Advisory ID CVE-2024-55591/ CVE-2025-24472 Critical 9.6 FortiOS 7.0.0–7.0.16, FortiProxy 7.0.0–7.0.19 & 7.2.0–7.2.12 Authentication bypass via Node.js websocket module allowing super-admin privileges FG-IR-24-535 CVE-2024-46666 High 7.5 FortiOS VPN Device DoS via apreq library flaws in file upload handling FG-IR-24-219 CVE-2024-52966 Low 4.1 FortiAnalyzer 7.4.1–7.6.0 Exposure of logs from unrelated ADOMs in Log View FG-IR-24-422 CVE-2023-40721 Medium 6.4 FortiOS, FortiProxy, FortiPAM Format string vulnerability in CLI commands FG-IR-23-261 CVE-2024-40585 Medium 5.9 FortiAnalyzer, FortiManager Sensitive data insertion into event logs FG-IR-24-311 CVE-2024-35279 High 7.5 FortiOS 7.4.0–7.4.4 Stack buffer overflow in CAPWAP control module FG-IR-24-160 CVE-2024-40591 High 8.0 FortiOS 7.4.1–7.6.0 Privilege escalation via security fabric misconfiguration FG-IR-24-302 CVE-2024-33504 Medium 5.3 FortiManager, FortiManager Cloud Use of hard-coded cryptographic keys FG-IR-24-094 N/A (FG-IR-24-259) High 7.1 FortiManager, FortiOS, FortiProxy Path traversal allowing file access/modification via security fabric interface FG-IR-24-259 N/A (FG-IR-24-282) Medium 6.4 FortiOS, FortiProxy, FortiSASE HTTP response splitting enabling cache poisoning FG-IR-24-282 N/A (FG-IR-24-221) High 8.0 FortiAnalyzer, FortiManager Brute-force authentication bypass in Security Fabric protocol FG-IR-24-221 N/A (FG-IR-23-494) Medium 4.1 FortiOS, FortiProxy, FortiMail, FortiSwitch Web cache poisoning via crafted HTTP requests FG-IR-23-494
Other resolved issues include path traversal, command injection, cross-site scripting (XSS), and denial-of-service (DoS) vulnerabilities. Fortinet recommends prioritizing patches for CVE-2024-55591, CVE-2023-37936, and CVE-2024-35279 due to their high exploit potential.
Mitigation and Response
Fortinet urges organizations to:
- Immediately patch affected systems to the latest firmware versions.
- Restrict access to management interfaces, ensuring they are not publicly exposed.
- Audit logs for indicators of compromise (IoCs), such as unexpected admin account creation or SSL VPN modifications.
- Enable multi-factor authentication (MFA) for administrative accounts.
This update follows a January 2025 dark web leak of 15,000 FortiGate firewall credentials from 2022, attributed to prior compromises like CVE-2022-40684. While the leaked data is older, it underscores the persistent targeting of Fortinet devices by advanced threat actors.
Are you from SOC/DFIR Team? - Join 500,000+ Researchers to Analyze Cyber Threats with ANY.RUN Sandbox - Try for Free
The post Fortinet Addresses Multiple Vulnerabilities in Major Security Update appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






































































































































































































































.jpg?#)










































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)