Beware! AI-Assisted Fake GitHub Repositories Steal Sensitive Data Including Login Credentials
A sophisticated malware campaign leveraging artificial intelligence to create deceptive GitHub repositories has been observed distributing SmartLoader payloads that ultimately deploy Lumma Stealer, a dangerous information-stealing malware. This operation exploits GitHub’s trusted reputation to bypass security defenses, targeting users seeking gaming mods, cracked software, and cryptocurrency tools through AI-generated documentation and strategically obfuscated scripts. GitHub […] The post Beware! AI-Assisted Fake GitHub Repositories Steal Sensitive Data Including Login Credentials appeared first on Cyber Security News.

A sophisticated malware campaign leveraging artificial intelligence to create deceptive GitHub repositories has been observed distributing SmartLoader payloads that ultimately deploy Lumma Stealer, a dangerous information-stealing malware.
This operation exploits GitHub’s trusted reputation to bypass security defenses, targeting users seeking gaming mods, cracked software, and cryptocurrency tools through AI-generated documentation and strategically obfuscated scripts.
GitHub Malware Campaign Exploits AI and Obfuscation
According to Trend Micro reports, the threat actors behind this campaign, tracked as Water Kurita, have shifted tactics from hosting malicious files in GitHub attachments to creating full repositories with AI-generated README files.
These repositories mimic legitimate projects through polished documentation, structured content with emojis, and hyperlinked logos – all hallmarks of generative AI output designed to bypass human scrutiny.
The repositories contain only a README file in their main branch, with malicious ZIP archives (e.g., Release.zip) hidden in the Releases section to evade automated code scanning.
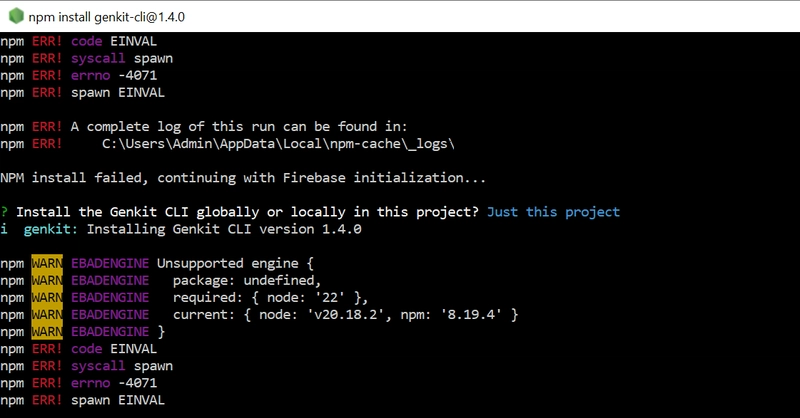
When users download and extract these archives, they encounter four components:
- lua51.dll – A legitimate LUAJIT runtime interpreter
- luajit.exe – The Lua loader executable
- userdata.txt – Obfuscated malicious Lua script
- Launcher.bat – Batch file executing luajit.exe userdata.txt
The batch file initiates a multi-stage attack chain where the Lua script connects to command-and-control (C&C) servers, downloads additional payloads, and establishes persistence via scheduled tasks.
This technique allows the malware to survive system reboots while conducting system reconnaissance using commands like:
These commands probe for the presence of security software from vendors like Avast, Bitdefender, and ESET.
Lumma Stealer and its Tactics
SmartLoader employs multiple obfuscation layers, including Prometheus Obfuscator and Lua’s foreign function interface (FFI), to hinder analysis.
The loader retrieves two critical files from GitHub – lmd.txt and l.txt – renaming them to search.exe (Lumma Stealer) and debug.lua (secondary script).
The attack culminates with the execution of a weaponized AutoIt interpreter named Research.com that decrypts and runs malicious code hidden within fake Excel files:
This concatenation process reassembles the encrypted Lumma Stealer payload from distributed fragments.
The malware then initiates browser debugging sessions to bypass security controls:
This technique enables unauthorized access to browser data and extensions, particularly targeting cryptocurrency wallets like MetaMask and 2FA tools such as Authy.
Data Exfiltration and Operational Impact
Lumma Stealer establishes communication with its C&C server at pasteflawded[.]world, exfiltrating:
- Browser credentials and session cookies
- Cryptocurrency wallet seeds and private keys
- Two-factor authentication extension data
- Screenshots and clipboard contents
- System metadata for targeted follow-up attacks
The malware’s modular architecture allows operators to dynamically update payloads, with recent versions incorporating anti-analysis checks that detect virtual machines and sandbox environments.
This adaptability has made Lumma Stealer a preferred tool in cybercriminal forums, where stolen data fetches prices ranging from $500 for browser credentials to $5,000 for comprehensive digital identity packages.
Mitigation Strategies and Defense
To counter these evolving threats, cybersecurity firm Trend Micro recommends:
- Implementing application allowlisting to block unauthorized scripts
- Deploying behavior-based detection for Lua script execution patterns
- Restricting GitHub API access to prevent automated repository cloning
- Configuring email security gateways to intercept phishing lures promoting fake repositories
- Enforcing mandatory code review processes for third-party dependencies
This campaign demonstrates the growing sophistication of AI-assisted cyber threats, where attackers combine generative AI with legitimate development tools to create convincing attack vectors.
As Water Kurita continues to refine its tactics, organizations must adopt zero-trust principles for third-party code and enhance monitoring of scripting language activity.
The shift from simple file hosting to full repository clones signals a new era of supply chain attacks that demand equally innovative defense strategies.
You can found the indicators of compromise here.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Beware! AI-Assisted Fake GitHub Repositories Steal Sensitive Data Including Login Credentials appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)