What is non-human identity (NHI)?
Identity isn’t just for people anymore. With the rise of automation, interconnected systems and machines also need secure identities to access resources and communicate. A new concept, non-human Identity (NHI), was introduced to authenticate and authorise these machines and systems. What is NHI? Non-human identities are assigned to machines, services, and other digital entities that perform tasks without human intervention. These identities require secure authentication and authorisation mechanisms like human users to interact safely with systems and data. Why NHI Matters? Unlike humans, who can use passwords and multi-factor authentication, NHIs rely on tokens, certificates, and secret keys to prove their identity for security, observability, and compliance purposes. If these credentials are not properly secured and managed, they can be exploited, leading to unauthorised access and potential data breaches. Common NHI Use Cases CI/CD pipelines: Automated deployments often use service accounts or tokens to interact with infrastructure. Serverless functions and containers: This is needed to secure call APIs or access databases. IoT devices: Each device needs a unique identity for secure communication. Challenges of Managing NHIs Managing NHIs at scale presents several challenges: Without centralised monitoring and direct human oversight, it becomes challenging for security teams to maintain visibility into which NHIs are active, their permissions, and whether they are still needed. When NHIs are not correctly managed, they create unique security challenges that cyber attackers can exploit. Most non-human entities have more access than necessary, which increases the risk of misuse. Medium-to-large-sized organisations often create NHIs with different policy levels, with some granting excessive permissions. Without a centralised policy, these minor inconsistencies can weaken security and even increase compliance issues in the future. Best Practices To secure NHIs, organisations should adopt centralized secrets management, enforce least privilege access, and implement automated credential rotation. Tools like Doppler help streamline secret management and reduce the attack surface associated with machine identities. Please read Doppler's detailed article about NHI here.
Identity isn’t just for people anymore. With the rise of automation, interconnected systems and machines also need secure identities to access resources and communicate. A new concept, non-human Identity (NHI), was introduced to authenticate and authorise these machines and systems.
What is NHI?
Non-human identities are assigned to machines, services, and other digital entities that perform tasks without human intervention. These identities require secure authentication and authorisation mechanisms like human users to interact safely with systems and data.
Why NHI Matters?
Unlike humans, who can use passwords and multi-factor authentication, NHIs rely on tokens, certificates, and secret keys to prove their identity for security, observability, and compliance purposes. If these credentials are not properly secured and managed, they can be exploited, leading to unauthorised access and potential data breaches.
Common NHI Use Cases
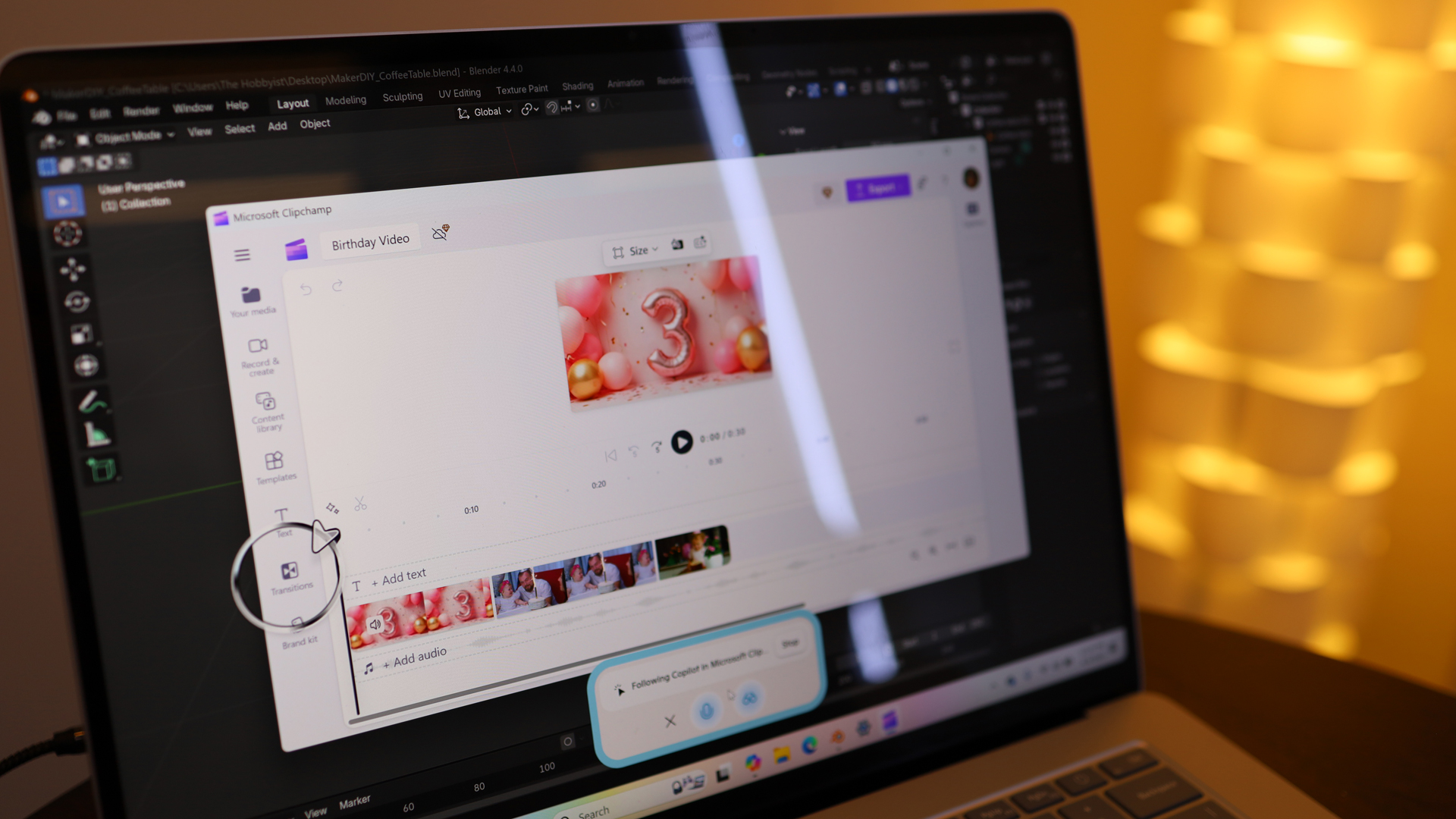
CI/CD pipelines: Automated deployments often use service accounts or tokens to interact with infrastructure.
Serverless functions and containers: This is needed to secure call APIs or access databases.
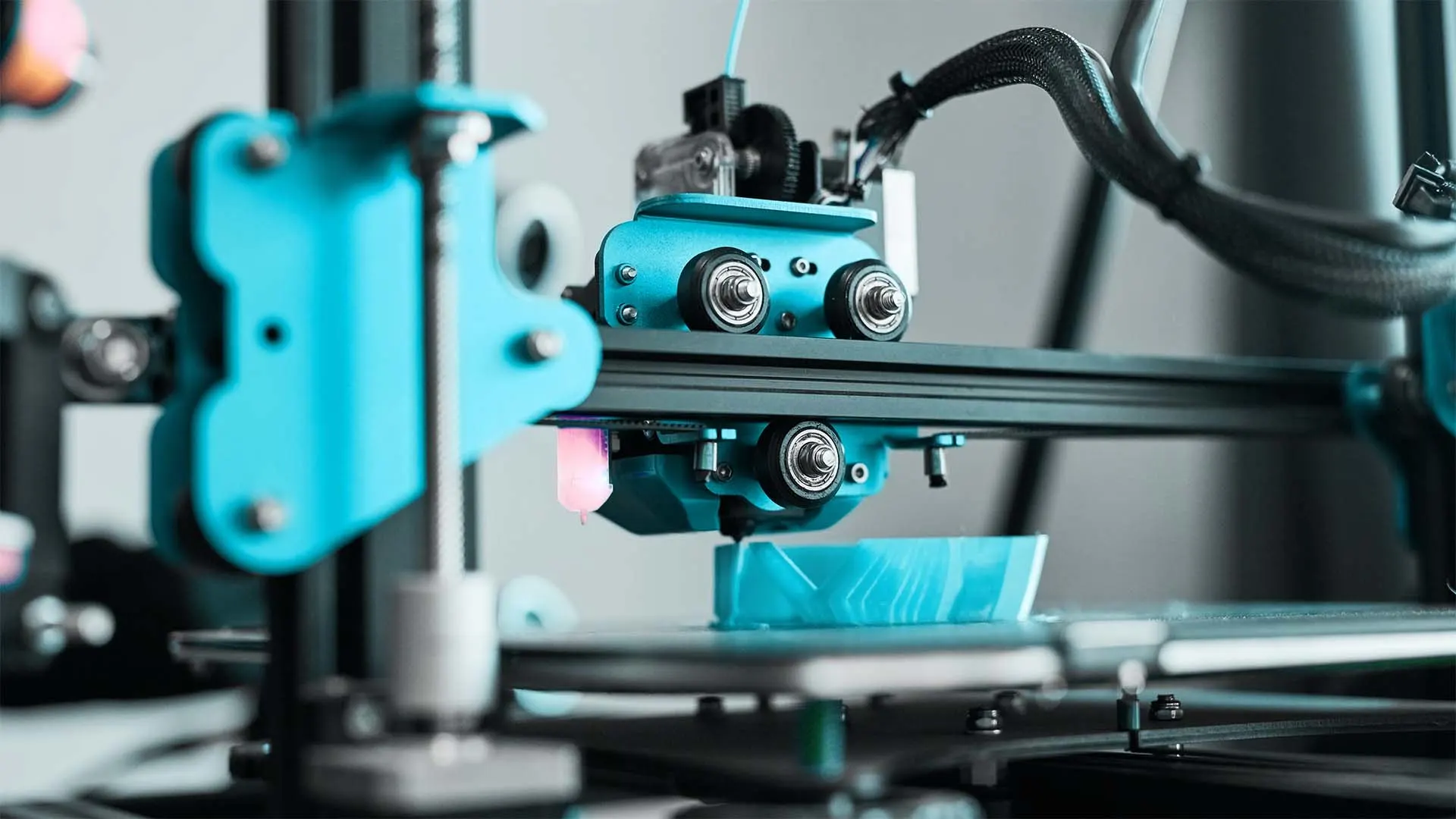
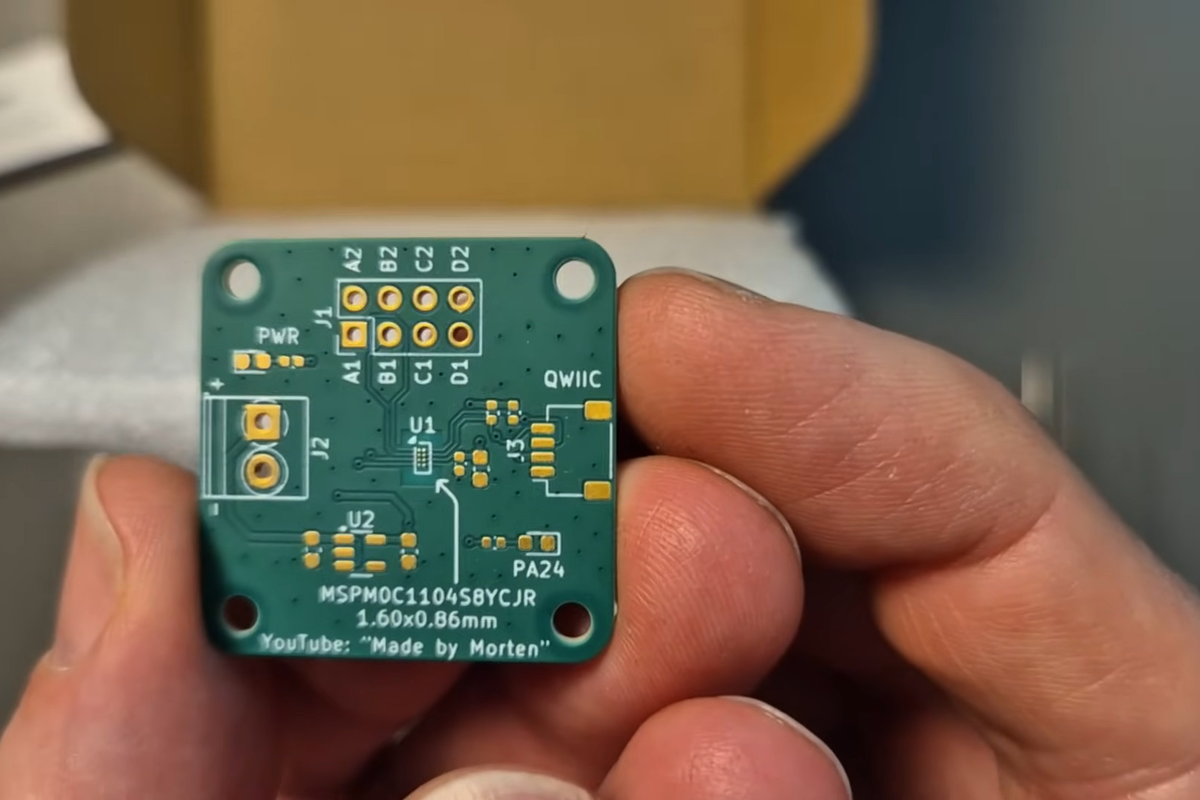
IoT devices: Each device needs a unique identity for secure communication.
Challenges of Managing NHIs
Managing NHIs at scale presents several challenges:
Without centralised monitoring and direct human oversight, it becomes challenging for security teams to maintain visibility into which NHIs are active, their permissions, and whether they are still needed.When NHIs are not correctly managed, they create unique security challenges that cyber attackers can exploit. Most non-human entities have more access than necessary, which increases the risk of misuse.
Medium-to-large-sized organisations often create NHIs with different policy levels, with some granting excessive permissions. Without a centralised policy, these minor inconsistencies can weaken security and even increase compliance issues in the future.
Best Practices
To secure NHIs, organisations should adopt centralized secrets management, enforce least privilege access, and implement automated credential rotation. Tools like Doppler help streamline secret management and reduce the attack surface associated with machine identities.
Please read Doppler's detailed article about NHI here.






















































.jpg)
%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)



















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)
































































































































![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)


































































































.png?#)





.jpg?#)































_Christophe_Coat_Alamy.jpg?#)







































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)