SPAWNCHIMERA Malware Exploiting Ivanti Buffer Overflow Vulnerability By Applying A Fix
Ivanti disclosed a critical buffer overflow vulnerability (CVE-2025-0282) affecting its Connect Secure VPN appliances. This vulnerability, caused by improper handling of the strncpy function in the web server component, allowed attackers to execute arbitrary code remotely. JPCERT/CC confirmed multiple exploitation cases in Japan as early as December 2024, preceding Ivanti’s official advisory. Among these incidents, […] The post SPAWNCHIMERA Malware Exploiting Ivanti Buffer Overflow Vulnerability By Applying A Fix appeared first on Cyber Security News.

Ivanti disclosed a critical buffer overflow vulnerability (CVE-2025-0282) affecting its Connect Secure VPN appliances.
This vulnerability, caused by improper handling of the strncpy function in the web server component, allowed attackers to execute arbitrary code remotely.
JPCERT/CC confirmed multiple exploitation cases in Japan as early as December 2024, preceding Ivanti’s official advisory.
Among these incidents, cybersecurity researchers identified an evolved variant of the SPAWN malware family dubbed “SPAWNCHIMERA” that not only exploits this flaw but also deploys a self-contained fix to prevent competing threat actors from leveraging the same vulnerability.
SPAWNCHIMERA represents a modular upgrade to previous SPAWN malware variants (SPAWNANT, SPAWNMOLE, SPAWNSNAIL), combining their functionalities into a unified framework.
Its primary objectives include persistent access, lateral movement, and traffic interception via injected processes.
Key modifications include refined UNIX domain socket communication, stripped debug messages, and novel XOR-based decoding routines for stealthier operations.
.webp)
However, researchers noted that its most striking feature is a built-in vulnerability patch designed to monopolize exploitation of CVE-2025-0282.
Analysis of the Embedded Vulnerability Patch
SPAWNCHIMERA’s authors implemented an unconventional defense mechanism by hooking the vulnerable strncpy function.
.webp)
The malware dynamically modifies strncpy to limit buffer copies to 256 bytes, effectively neutralizing the buffer overflow vulnerability it exploits.
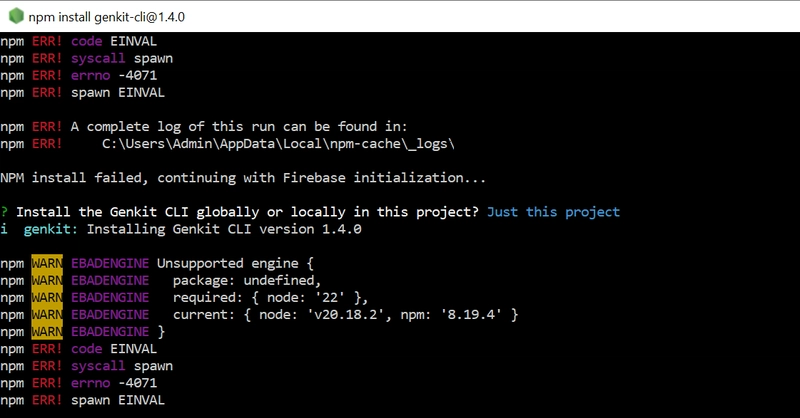
This hijacked function executes the following logic:-
- Process Validation: Checks if the running process name has a hexadecimal sum of
0x13E(corresponding to ASCII values of “web” [0x77 + 0x65 + 0x62]). - Size Restriction: Automatically truncates
strncpyoperations exceeding 256 bytes when targeting vulnerable processes. - Bypass Detection: Disables the patch if the source buffer’s first four bytes match
0x04050203, allowing selective exploitation by the malware operators.
n256 = size;
progname = *_progname;
// ... [process validation logic]
if (n0x13E == 0x13E && (dest & 0xFF000000) == 0xFF000000 && size > 256) {
if (*src == 3 && *(_WORD *)(src + 1) == 0x502) { // Check bypass signature
if (src[3] != 4) n256 = 256;
} else {
n256 = 256; // Enforce size limit
}
}This paradoxical approach—exploiting a vulnerability while patching it—serves two purposes: it destabilizes competing attacker campaigns and complicates incident response.
Security teams analyzing compromised systems might erroneously conclude the vulnerability is patched, overlooking SPAWNCHIMERA’s persistence mechanisms.
%20(Source%20-%20JP%20CERT).webp)
The malware further obscures operations by replacing plaintext SSH keys with XOR-encoded payloads and eliminating diagnostic messages.
Besides this, there is no definitive attribution exists, the tactic of “exploit monopolization” suggests involvement of state-aligned actors seeking to preserve access to critical infrastructure.
Cybersecurity analysts recommend immediately patching Ivanti appliances and inspecting for artifacts like the /home/runtime/tmp/.logsrv UNIX socket and suspicious shared objects (libdsupgrade.so).
With SPAWNCHIMERA’s hash (94b1087af3120ae22cea734d9eea88ede4ad5abe4bdeab2cc890e893c09be955) now public, organizations can hunt for this specific threat while remaining vigilant for further evolution of the SPAWN malware family.
Free Webinar: Better SOC with Interactive Malware Sandbox for Incident Response and Threat Hunting – Register Here
The post SPAWNCHIMERA Malware Exploiting Ivanti Buffer Overflow Vulnerability By Applying A Fix appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)