RedMike Hackers Exploited 1000+ Cisco Devices to Gain Admin Access
Researchers observed a sophisticated cyber-espionage campaign led by the Chinese state-sponsored group known as “Salt Typhoon,” also referred to as “RedMike.” Between December 2024 and January 2025, the group exploited over 1,000 unpatched Cisco network devices globally, targeting telecommunications providers and universities. The campaign highlights the ongoing vulnerability of critical infrastructure and the strategic intelligence […] The post RedMike Hackers Exploited 1000+ Cisco Devices to Gain Admin Access appeared first on Cyber Security News.

Researchers observed a sophisticated cyber-espionage campaign led by the Chinese state-sponsored group known as “Salt Typhoon,” also referred to as “RedMike.”
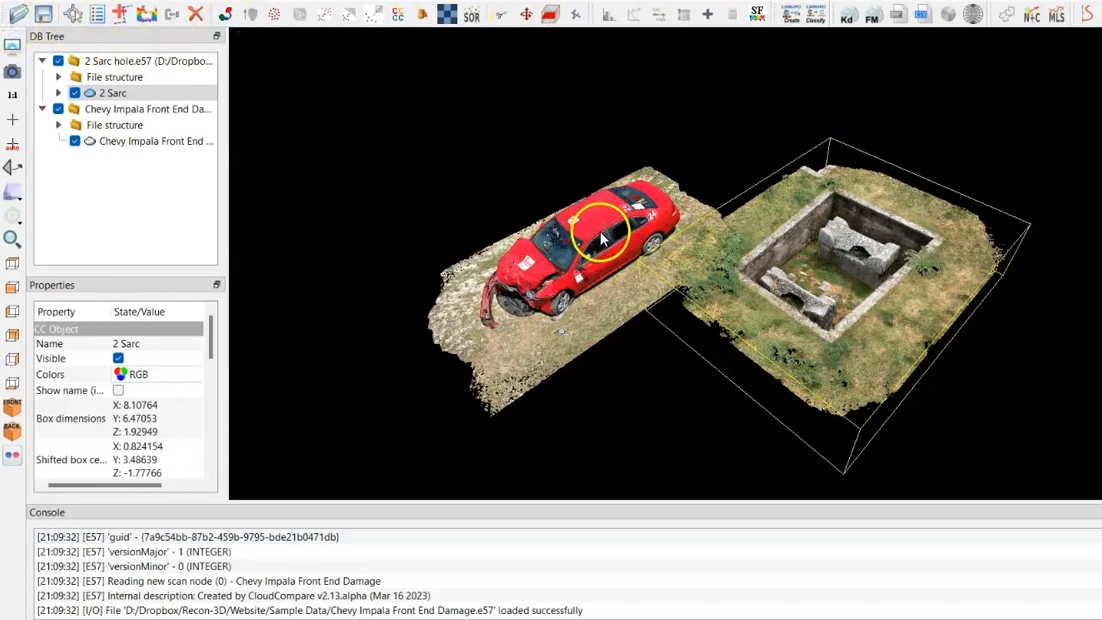
Between December 2024 and January 2025, the group exploited over 1,000 unpatched Cisco network devices globally, targeting telecommunications providers and universities.
The campaign highlights the ongoing vulnerability of critical infrastructure and the strategic intelligence threats posed by state-backed cyber actors.
Technical Exploitation Overview
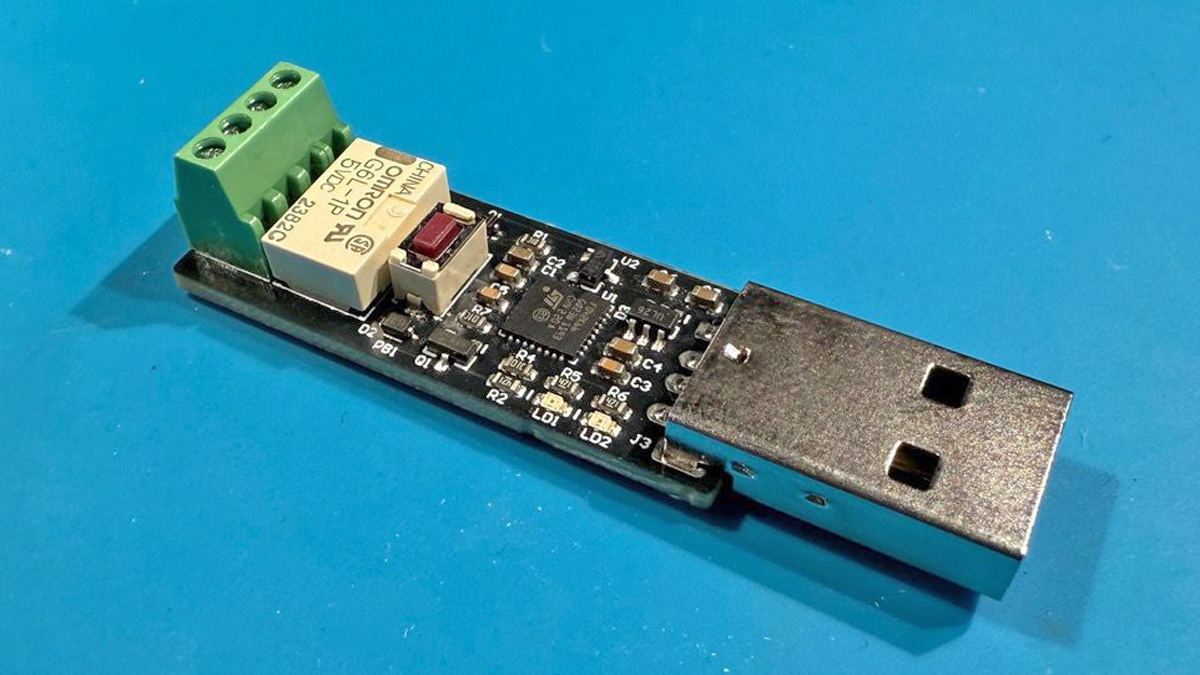
Salt Typhoon exploited two privilege escalation vulnerabilities in Cisco IOS XE software: CVE-2023-20198 and CVE-2023-20273.
These vulnerabilities, disclosed in October 2023, allowed attackers to gain initial access via the web user interface (UI) and escalate privileges to root-level access.
Once compromised, attackers reconfigured devices to establish Generic Routing Encapsulation (GRE) tunnels, enabling persistent access and covert data exfiltration.
The GRE tunneling protocol, a standard feature in Cisco devices, was leveraged to bypass firewalls and intrusion detection systems.
This allowed Salt Typhoon to maintain stealthy communication channels between compromised devices and their command-and-control infrastructure.
Targeted Organizations
Insikt Group stated that the campaign primarily targeted telecommunications providers but extended to universities across multiple countries. Key victims included:
Telecommunications Providers: A U.S.-based affiliate of a U.K. telecom provider, South African telecommunications company, and ISPs in Italy and Thailand.
Universities: Institutions in Argentina, Bangladesh, Indonesia, Malaysia, Mexico, the Netherlands, Thailand, Vietnam, and the U.S., including UCLA and TU Delft.
These targets were likely chosen for their association with cutting-edge research in telecommunications, engineering, and technology.
More than half of the targeted devices were located in the U.S., South America, and India.
Researchers identified over 12,000 exposed Cisco devices globally but noted that Salt Typhoon’s campaign was highly selective, focusing on approximately 8% of these devices.
Reconnaissance activities were also observed against Myanmar-based telecom provider Mytel in December 2024. These scans suggest broader ambitions to infiltrate regional networks for espionage purposes.
Salt Typhoon’s activities extend beyond technical exploitation to strategic intelligence objectives. Persistent access to telecommunications networks enables state-backed actors to:
- Monitor Communications: Real-time interception of sensitive conversations.
- Disrupt Services: Potential sabotage during geopolitical conflicts.
- Manipulate Data Flows: Alteration of critical information for intelligence or propaganda purposes.
The group’s focus on lawful intercept systems and high-profile U.S. political figures underscores its intent to exploit vulnerabilities for national security threats.
Mitigation Measures
To counter such threats, organizations must adopt proactive cybersecurity measures:
- Apply updates for vulnerabilities like CVE-2023-20198 and CVE-2023-20273 immediately.
- Restrict exposure of web UIs on public-facing devices.
- Detect unauthorized configuration changes or GRE tunnel activity.
- Use end-to-end encryption for sensitive communications.
Government agencies like CISA and the FBI have emphasized the importance of encrypted messaging applications to mitigate eavesdropping risks.
The U.S. The Treasury Department recently sanctioned Sichuan Juxinhe Network Technology Co., Ltd., a Chinese contractor linked to the Salt Typhoon’s activities.
While this marks a strong stance against state-sponsored cyber espionage, experts stress that international collaboration is essential for combating such persistent threats effectively.
Salt Typhoon’s exploitation of Cisco devices exemplifies the growing trend of targeting unpatched infrastructure for initial access. As state-backed actors continue to refine their techniques, organizations must remain vigilant against evolving cyber threats.
Find this Story Interesting! Follow us on Google News, LinkedIn, and X to Get More Instant Updates
The post RedMike Hackers Exploited 1000+ Cisco Devices to Gain Admin Access appeared first on Cyber Security News.










































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)




.jpg?#)































_Christophe_Coat_Alamy.jpg?#)






































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)