Notorious Black Basta Tactics, Techniques and Procedures Uncovered From Leak
A significant leak of internal chat logs from the Black Basta ransomware group has provided cybersecurity researchers with unprecedented insight into their operations. A Telegram user named ExploitWhispers unveiled the leak contained approximately 200,000 chat messages dated between September 2023 and June 2024. This security breach rivals the 2022 leaks that affected the Conti ransomware […] The post Notorious Black Basta Tactics, Techniques and Procedures Uncovered From Leak appeared first on Cyber Security News.

A significant leak of internal chat logs from the Black Basta ransomware group has provided cybersecurity researchers with unprecedented insight into their operations.
A Telegram user named ExploitWhispers unveiled the leak contained approximately 200,000 chat messages dated between September 2023 and June 2024.
This security breach rivals the 2022 leaks that affected the Conti ransomware gang and has given threat intelligence experts valuable information about Black Basta’s capabilities, tools, and motivations.
Black Basta, which emerged in 2022, operates under the Ransomware-as-a-Service (RaaS) model and has targeted numerous countries worldwide, including the United States, Japan, Australia, the United Kingdom, Canada, and New Zealand.
The financially motivated, Russian-speaking group employs a double extortion tactic whereby they not only encrypt victims’ data but also threaten to publish exfiltrated information if ransom demands are not met.
Their impact has been substantial, with over 500 entities across North America, Europe, and Australia affected between April 2022 and May 2024.
On May 10, 2024, a joint report from the Cybersecurity & Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) detailed Black Basta’s extensive activities.
The report highlighted that the group had targeted 12 out of 16 critical infrastructure sectors, with researchers noting an increased focus on healthcare organizations due to their size and potential impact.
This collaborative analysis, released in conjunction with the Department of Health and Human Services and the Multi-State Information Sharing and Analysis Center, provided crucial information about the group’s tactics, techniques, and procedures (TTPs) and indicators of compromise.
According to threat hunters at Intel471 who analyzed the leaked communications, Black Basta’s attack methodology begins with initial access primarily through phishing emails containing malicious attachments or links, compromised websites, or exploiting known vulnerabilities.
In recent campaigns, affiliates have been observed sending overwhelming amounts of spam emails to victims, followed by phone calls where actors pose as IT staff offering assistance with the spam problem. During these calls, victims are persuaded to download remote support tools, giving attackers access to their systems.
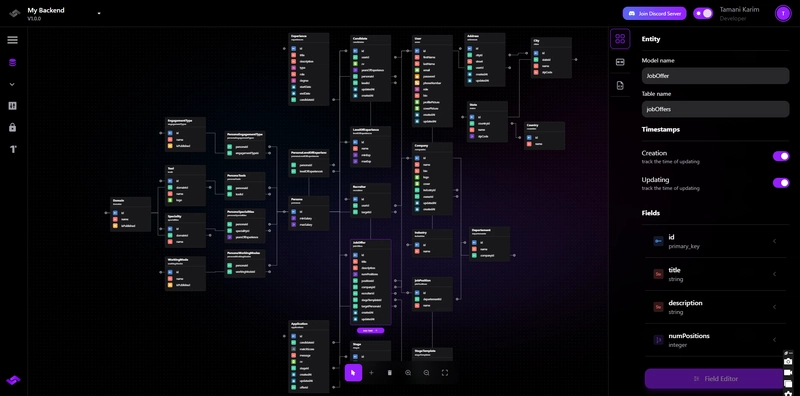
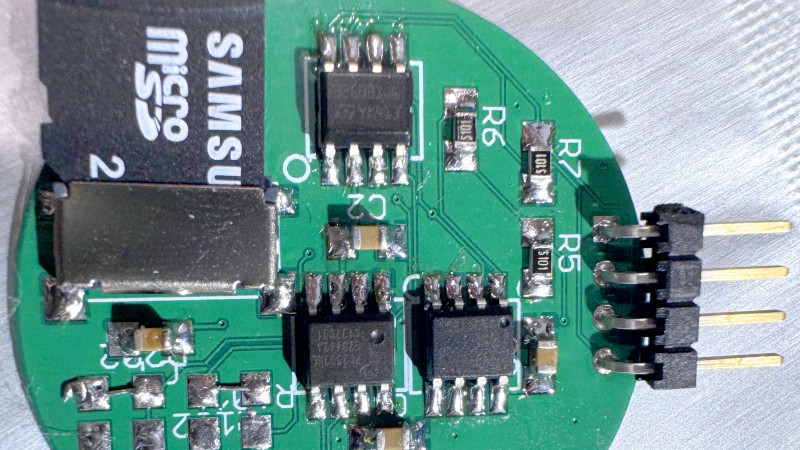
Technical Arsenal and Methodologies
The leak revealed a sophisticated technical arsenal employed by Black Basta operators. Their reconnaissance phase involves using discovery tools such as ifconfig.exe, netstat.exe, and ping.exe, along with WMIC abuse to gather information about target networks.
The SoftPerfect network scanner (netscan.exe) is specifically employed to survey victim networks.
For defense evasion, the group utilizes temporary directories, abuses the Background Intelligent Transfer Service (BITS) component, and tampers with Windows Defender.
A tool called Backstab is sometimes deployed to disable antivirus products that might interfere with their operations.
Command and control access is established via remote management tools like AnyDesk, while lateral movement is facilitated through BITSAdmin and PsExec.
Other tools observed in their arsenal include Splashtop, Screen Connect, and Cobalt Strike beacons.
For credential access, Black Basta operators leverage Mimikatz to scrape credentials and escalate privileges within compromised environments. PowerShell scripts are frequently abused for downloading files and execution of malicious payloads.
Data exfiltration, a crucial step in their double extortion scheme, is conducted primarily through the Rclone utility and sometimes WinSCP.
After securing the stolen data, operators begin encrypting files across local and network drives, appending the “.basta” extension to encrypted files, and dropping ransom notes containing instructions to contact the group via specified URLs.
To prevent recovery efforts, Black Basta actors delete volume shadow copies using the command “vssadmin.exe delete shadows /all /quiet” and implement persistence mechanisms through scheduled task creation.
The group maintains operational security through their chat communications, which included discussions about target selection and ransomware deployment techniques that have now been exposed through the leak.
The uncovered technical details provide cybersecurity defenders with valuable information to develop better detection and mitigation strategies against this notorious threat actor.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free
The post Notorious Black Basta Tactics, Techniques and Procedures Uncovered From Leak appeared first on Cyber Security News.












































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)
























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)





































































































































.png?#)


