Linux X.509 Certificate-Based User Login Flaws Let Attackers Bypass Authentication
Three critical vulnerabilities have been identified in the PAM-PKCS#11 module, a widely used Linux-PAM login module that facilitates X.509 certificate-based user authentication. These vulnerabilities, cataloged under CVE-2025-24032, CVE-2025-24531, and CVE-2025-24031, pose significant risks by allowing attackers to bypass authentication mechanisms, potentially leading to unauthorized access and system disruptions. CVE-2025-24032 – Authentication Bypass via Token Hijacking […] The post Linux X.509 Certificate-Based User Login Flaws Let Attackers Bypass Authentication appeared first on Cyber Security News.

Three critical vulnerabilities have been identified in the PAM-PKCS#11 module, a widely used Linux-PAM login module that facilitates X.509 certificate-based user authentication.
These vulnerabilities, cataloged under CVE-2025-24032, CVE-2025-24531, and CVE-2025-24031, pose significant risks by allowing attackers to bypass authentication mechanisms, potentially leading to unauthorized access and system disruptions.
CVE-2025-24032 – Authentication Bypass via Token Hijacking
The first vulnerability, CVE-2025-24032, affects versions of PAM-PKCS#11 prior to 0.6.13. Here, if the cert_policy is set to none (which is the default setting), the module only verifies if a user can log into the token without checking the private key’s signature.
This flaw allows an attacker to create a token with the user’s public certificate and a known PIN, thereby logging in as the user without needing the private key.
This vulnerability has been classified as high severity due to its potential for unauthorized access. The fix involves upgrading to version 0.6.13 or later, where the default behavior has been changed to require a signature check.
CVE-2025-24531 – Authentication Bypass in Error Situations
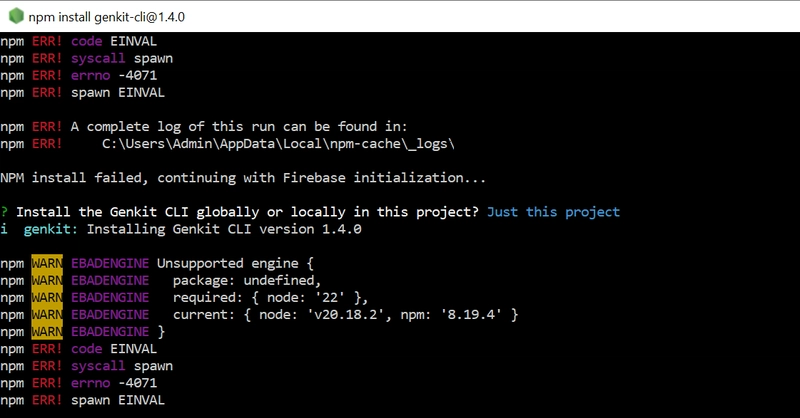
The second issue, CVE-2025-24531, was introduced in version 0.6.12 of PAM-PKCS#11 and fixed in version 0.6.13. This vulnerability allows for an authentication bypass in error situations, particularly when memory allocation fails or during incorrect privilege changes.
The module returns PAM_IGNORE, which can lead to an authentication bypass if the nouserok option is enabled, allowing attackers to log in without proper verification.
CVE-2025-24031 – Segmentation Fault on PIN Entry
Lastly, CVE-2025-24031 affects versions 0.6.12 and prior, where the module segfaults if a user cancels the PIN entry process (by pressing ctrl-c or ctrl-d). This leads to a denial of service as the system crashes, impacting availability. The recommended mitigation is to update to version 0.6.13 or later, which includes a patch for this issue.
Mitigation and Recommendations
To mitigate these vulnerabilities, users are urged to:
- Upgrade to PAM-PKCS#11 version 0.6.13 or later to address all three vulnerabilities.
- Configure
cert_policy = signature;inpam_pkcs11.confas a workaround for CVE-2025-24032. - Monitor and restart affected services if they crash due to CVE-2025-24031.
- Implement additional access controls and educate users about the risks of canceling PIN entry.
These vulnerabilities underscore the importance of regular updates and careful configuration of authentication modules in Linux environments to prevent unauthorized access and ensure system integrity.
Users and system administrators should take immediate action to secure their systems against these potential threats.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post Linux X.509 Certificate-Based User Login Flaws Let Attackers Bypass Authentication appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)