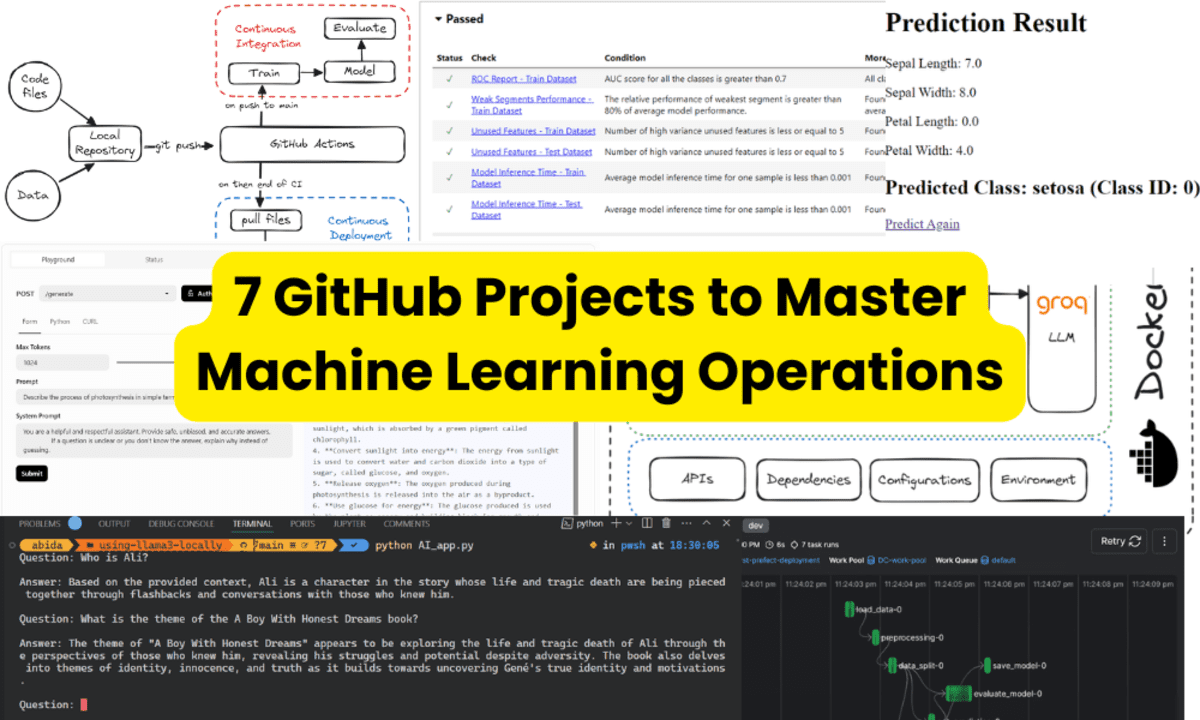
Gootloader Malware Attacking Users Via Google Search Ads Using Weaponized Documents
The notorious Gootloader malware has reemerged with evolved tactics, now leveraging Google Search advertisements to target users seeking legal document templates. This sophisticated campaign specifically promotes “free” legal templates, primarily non-disclosure agreements, through sponsored search results that appear legitimate to unsuspecting users. Upon clicking these advertisements, victims are directed to lawliner[.]com where they are prompted […] The post Gootloader Malware Attacking Users Via Google Search Ads Using Weaponized Documents appeared first on Cyber Security News.

The notorious Gootloader malware has reemerged with evolved tactics, now leveraging Google Search advertisements to target users seeking legal document templates.
This sophisticated campaign specifically promotes “free” legal templates, primarily non-disclosure agreements, through sponsored search results that appear legitimate to unsuspecting users.
Upon clicking these advertisements, victims are directed to lawliner[.]com where they are prompted to enter their email address to receive the requested document.
.webp)
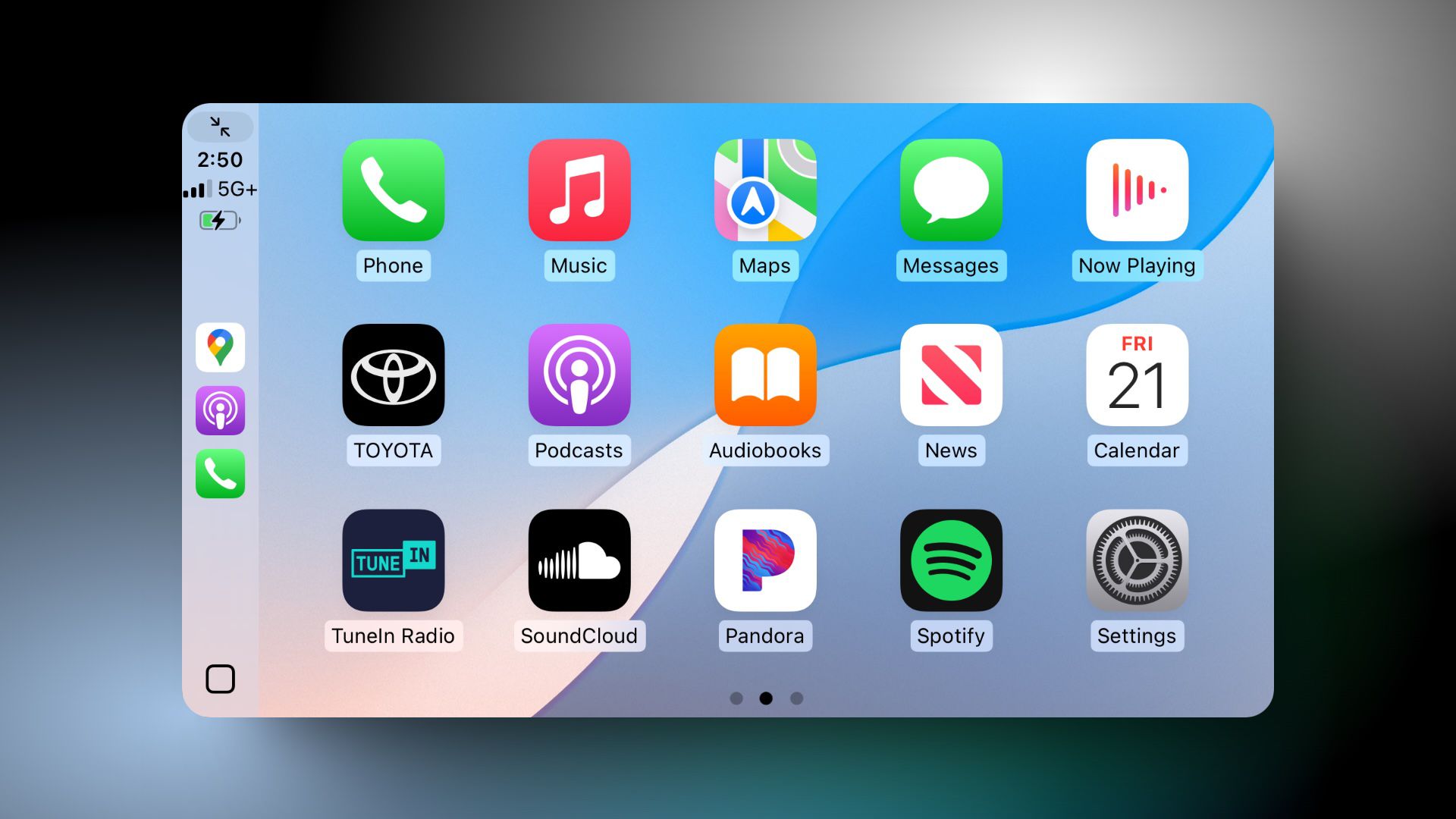
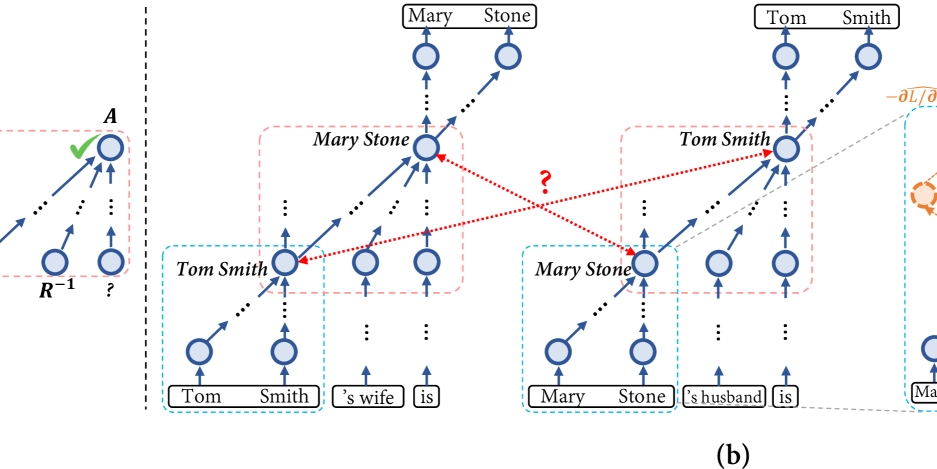
The attack chain begins innocuously with users searching for terms like “non disclosure agreement template” and encountering sponsored ads from domains that appear to offer legitimate legal services.
These advertisements are reportedly being delivered through “MED MEDIA GROUP LIMITED,” which security experts believe may have been compromised to facilitate this campaign.
A security analyst identified that after submitting their email address, victims receive a message from lawyer@skhm[.]org containing a download link that purportedly leads to the requested document.
However, instead of receiving a legitimate .docx file, users unwittingly download a compressed JavaScript file disguised as the legal document they requested.
The infection mechanism demonstrates sophisticated social engineering techniques.
When executed, the malicious JavaScript creates a scheduled task pointing to another .JS file in the user’s AppData\Roaming folder.
This persistence mechanism ensures the malware remains active across system reboots.
The script then executes PowerShell commands to establish connections with multiple WordPress blogs, approximately 10 in total, with 1-2 being genuinely compromised servers while others serve as decoys to complicate analysis.
.webp)
Security professionals recommend implementing immediate security measures including blocking web traffic to lawliner[.]com and skhm[.]org, filtering email communications from skhm[.]org, and conducting retrospective threat hunting for any historical interactions with these malicious domains to identify potentially compromised systems within organizational networks.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post Gootloader Malware Attacking Users Via Google Search Ads Using Weaponized Documents appeared first on Cyber Security News.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)






































































































































































































































.jpg?#)










































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)