Critical Ivanti CSA Vulnerability Let Attackers Execute Arbitrary Code Remotely
Ivanti has issued critical updates for its Cloud Services Application (CSA) to address two significant vulnerabilities, one of which could allow attackers to execute arbitrary code remotely. The vulnerabilities, identified as CVE-2024-47908 and CVE-2024-11771, affect CSA versions 5.0.4 and earlier. Ivanti strongly urges customers to update to version 5.0.5 immediately to mitigate these risks. The […] The post Critical Ivanti CSA Vulnerability Let Attackers Execute Arbitrary Code Remotely appeared first on Cyber Security News.

Ivanti has issued critical updates for its Cloud Services Application (CSA) to address two significant vulnerabilities, one of which could allow attackers to execute arbitrary code remotely.
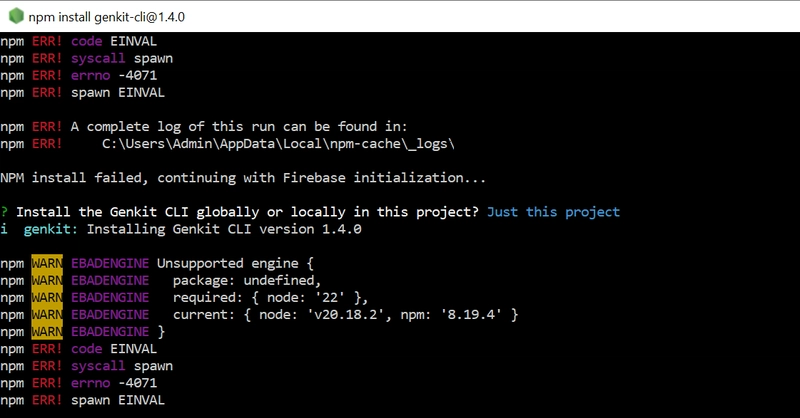
The vulnerabilities, identified as CVE-2024-47908 and CVE-2024-11771, affect CSA versions 5.0.4 and earlier. Ivanti strongly urges customers to update to version 5.0.5 immediately to mitigate these risks.
The most severe of the two vulnerabilities, CVE-2024-47908, is an operating system command injection flaw in the admin web console of Ivanti CSA.
This vulnerability allows a remote authenticated attacker with administrative privileges to execute arbitrary code on the affected system. With a CVSS score of 9.1 (Critical), this flaw poses a significant threat if exploited. The vulnerability is classified under CWE-78 (Improper Neutralization of Special Elements used in an OS Command).
The second vulnerability, CVE-2024-11771, involves a path traversal issue that permits a remote unauthenticated attacker to access restricted functionality within the application.
Although less severe than the first, this vulnerability still carries a CVSS score of 5.3 (Medium) and is categorized under CWE-22 (Path Traversal). Both vulnerabilities have been resolved in CSA version 5.0.5.
Successful exploitation of CVE-2024-47908 could allow attackers to gain full control over the affected system, potentially leading to data theft, system compromise, or further exploitation within the network.
Meanwhile, CVE-2024-11771 could enable attackers to bypass access controls and interact with restricted areas of the application.
Despite the critical nature of these vulnerabilities, Ivanti has confirmed that there have been no known cases of exploitation prior to their public disclosure. The vulnerabilities were responsibly disclosed through Ivanti’s internal program.
Affected Versions and Resolution
The vulnerabilities impact all CSA versions up to and including 5.0.4. To address these issues, Ivanti has released CSA version 5.0.5, which is now available for download via the company’s portal.
Product Name Affected Versions Resolved Version Ivanti CSA 5.0.4 and prior 5.0.5
Customers are advised to upgrade their systems immediately to ensure protection against potential exploitation.
Ivanti recommends that all users running affected versions take the following actions:
- Upgrade to CSA version 5.0.5 by downloading it from the official portal.
- Review their systems for any signs of unusual activity or compromise.
- Contact Ivanti support via the Success Portal if assistance is required during the update process.
Ivanti is not aware of any customers being exploited by these vulnerabilities prior to public disclosure. These vulnerabilities were disclosed through our responsible disclosure program.
Are you from SOC/DFIR Team? - Join 500,000+ Researchers to Analyze Cyber Threats with ANY.RUN Sandbox - Try for Free
The post Critical Ivanti CSA Vulnerability Let Attackers Execute Arbitrary Code Remotely appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)