AWS IAM Username Enumeration Vulnerabilities Let Attackers Detect Valid Users
Two critical username enumeration vulnerabilities were identified in the AWS Web Console, exposing all console-enabled Identity and Access Management (IAM) users to potential risk. These vulnerabilities, discovered by Rhino Security Labs, highlight security issues on AWS’s side of the Shared Responsibility Model, contrasting with the usual focus on customer-side security (“Security in the Cloud”). While […] The post AWS IAM Username Enumeration Vulnerabilities Let Attackers Detect Valid Users appeared first on Cyber Security News.

Two critical username enumeration vulnerabilities were identified in the AWS Web Console, exposing all console-enabled Identity and Access Management (IAM) users to potential risk.
These vulnerabilities, discovered by Rhino Security Labs, highlight security issues on AWS’s side of the Shared Responsibility Model, contrasting with the usual focus on customer-side security (“Security in the Cloud”).
While one vulnerability (CVE-2025-0693) was acknowledged and patched by AWS, the other was deemed an “accepted risk.”
Username Enumeration for Users with MFA
According to Rhino Security Labs report, when Multi-Factor Authentication (MFA) is enabled for an IAM user, the login flow inadvertently reveals whether a user exists. After submitting credentials, the application forks into two distinct states:
- If the user exists, the next page prompts for an MFA code.
- If the user does not exist, an error message explicitly states that the user does not exist.
This discrepancy allows attackers to confirm valid usernames without needing specialized tools. Such behavior is surprising for a major cloud provider like AWS, where consistent error messaging is typically expected to prevent such enumeration risks.
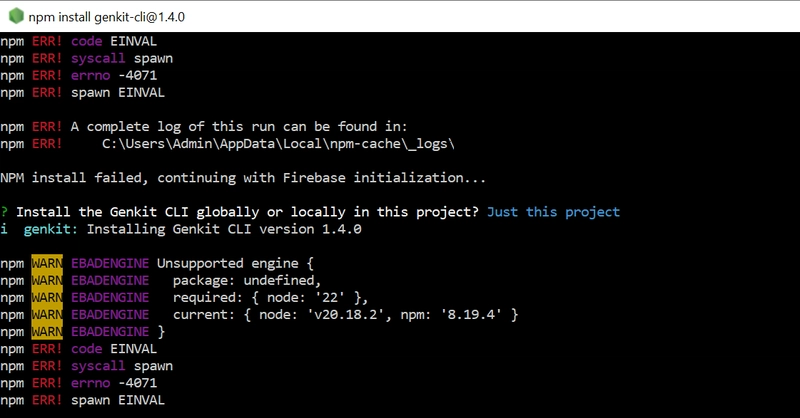
Timing Attack-Based Username Enumeration (CVE-2025-0693)
The second vulnerability, exploits timing differences during login attempts for non-MFA users. When a single-factor user submits credentials, two outcomes are possible:
- Error: If either the username or password is incorrect.
- Logged In: If both credentials are correct.
Simulating an attacker scenario using tools like Burp Suite, researchers observed that server response times varied based on username validity.
Specifically, for valid usernames, additional time was spent validating passwords.
For invalid usernames, the server exited early (“quick exit”), resulting in faster responses.
By measuring these timing differences using Burp Suite’s Intruder tool with controlled concurrency settings, researchers demonstrated that even a ~100ms delay could reliably indicate valid usernames. This vulnerability was promptly patched by AWS.
Technical Prevention Measures
To mitigate such vulnerabilities, authentication systems must ensure uniform server behavior for both valid and invalid usernames.
This approach eliminates timing discrepancies by processing both valid and invalid usernames equivalently.
Both vulnerabilities generate distinct “ConsoleLogin” events in AWS CloudTrail:
Invalid usernames trigger errorMessage: “No username found in supplied account”.
Valid usernames with incorrect passwords or missing MFA trigger errorMessage: “Failed Authentication”.
Organizations should monitor these events for patterns indicative of enumeration attempts, such as repeated login failures from diverse IP addresses or over extended periods.
These findings underscore the importance of securing IAM login flows against enumeration attacks.
While AWS has patched CVE-2025-0693 by introducing uniform response delays across all authentication failures, organizations must remain vigilant by enabling MFA and monitoring CloudTrail logs for unusual activity.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post AWS IAM Username Enumeration Vulnerabilities Let Attackers Detect Valid Users appeared first on Cyber Security News.




















































%20Abstract%20Background%20112024%20SOURCE%20Amazon.jpg)





















































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)





















































































































































































































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)





















_Anna_Berkut_Alamy.jpg?#)












































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)




































































![[Weekly funding roundup March 29-April 4] Steady-state VC inflow pre-empts Trump tariff impact](https://images.yourstory.com/cs/2/220356402d6d11e9aa979329348d4c3e/WeeklyFundingRoundupNewLogo1-1739546168054.jpg)