Securing Digital Interactions: Understanding RSA Encryption
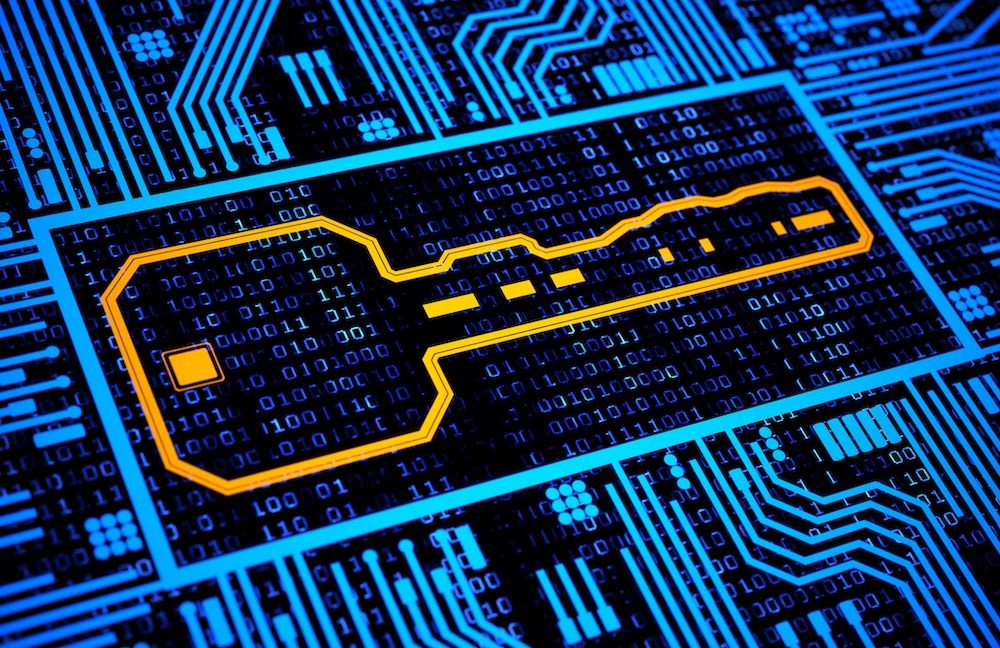
In today’s digital world, safeguarding sensitive information is more critical than ever. Whether online banking, secure emails, or encrypted messages, RSA encryption plays a vital role in protecting our data. As one of the most widely used public-key cryptosystems, RSA ensures confidentiality, integrity, and authenticity across countless applications. The Power of Asymmetric Cryptography RSA operates on asymmetric encryption, meaning it uses two mathematically linked keys: ✅ A public key for encryption (shared freely) ✅ A private key for decryption (kept secret) This approach eliminates the need for pre-shared secrets, making secure communication simpler and more scalable. How RSA Encryption Works: A Step-by-Step Breakdown Key Generation: The Security Foundation

In today’s digital world, safeguarding sensitive information is more critical than ever. Whether online banking, secure emails, or encrypted messages, RSA encryption plays a vital role in protecting our data. As one of the most widely used public-key cryptosystems, RSA ensures confidentiality, integrity, and authenticity across countless applications.
The Power of Asymmetric Cryptography
RSA operates on asymmetric encryption, meaning it uses two mathematically linked keys:
✅ A public key for encryption (shared freely)
✅ A private key for decryption (kept secret)
This approach eliminates the need for pre-shared secrets, making secure communication simpler and more scalable.
How RSA Encryption Works: A Step-by-Step Breakdown
- Key Generation: The Security Foundation









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)







































































































































































































































.jpg?#)








































































































































![YouTube Announces New Creation Tools for Shorts [Video]](https://www.iclarified.com/images/news/96923/96923/96923-640.jpg)

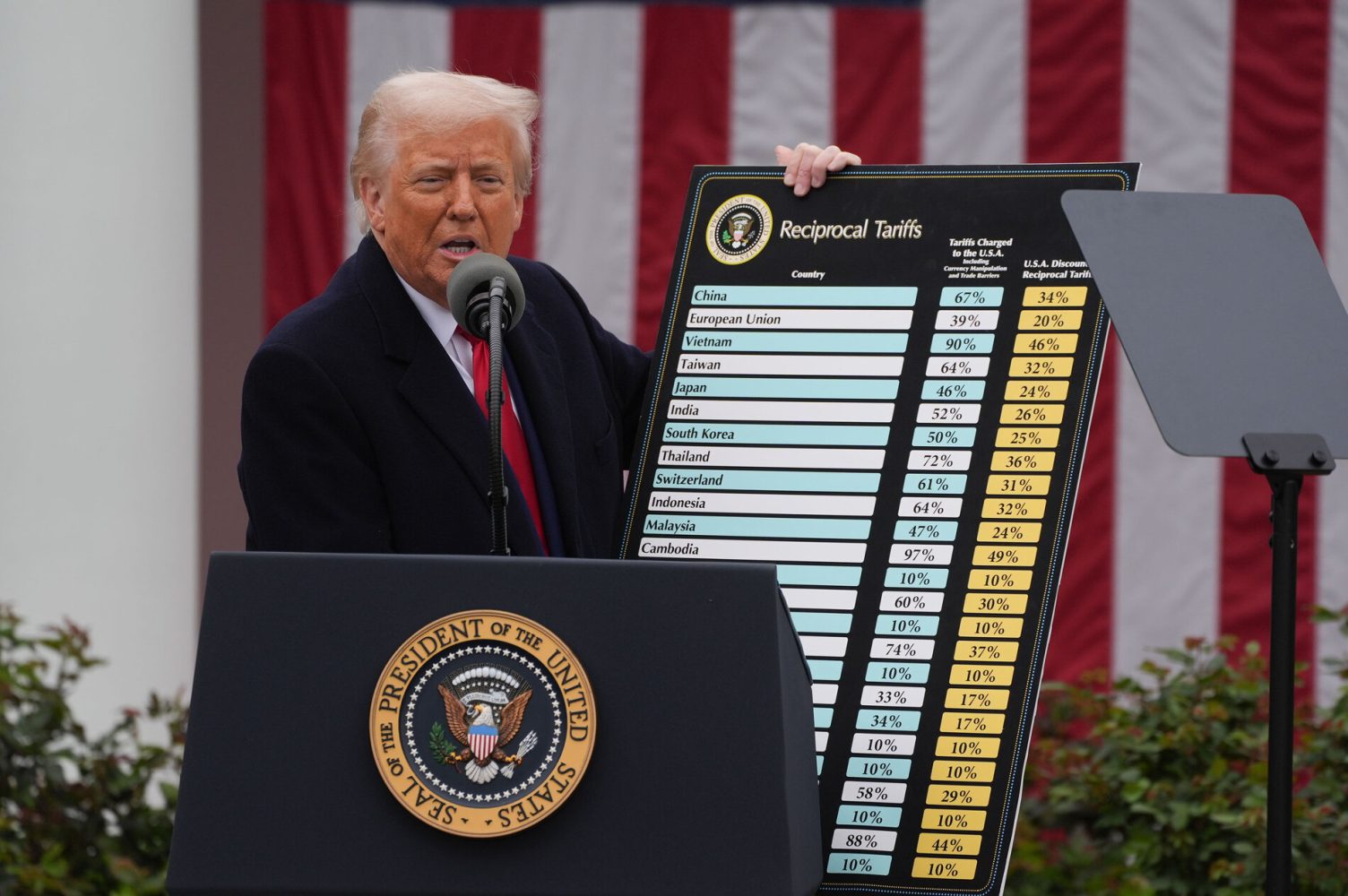
![Apple Faces New Tariffs but Has Options to Soften the Blow [Kuo]](https://www.iclarified.com/images/news/96921/96921/96921-640.jpg)