How to Track Configuration Changes and Compliance of AWS Resources
AWS Config is the most comprehensive service for tracking configuration changes and compliance. Key Features: Resource Configuration Tracking: Monitors and records configurations of supported AWS resources over time. Change History: Stores historical configuration data and changes. Compliance Auditing: Uses Config Rules to assess compliance with desired configurations. Automatic Remediation: Triggers AWS Systems Manager Automation to correct non-compliant resources. Setup Steps: First, go to AWS Config. If it's not enabled, it will be shown as bellow. Hit Get started. Then, we get into the first step and we have to select Recording strategy. There are two options from which one should be selected. I'm selecting the first option (All resource types with customisable overrides). All resource types with customisable overrides Specific resource type When selecting one out of these two, we should consider our use case and the pricing. Next, we have to select Recording frequency. Here also, there are two options from which one should be selected. Here also, I'm selecting the first option (Continuous recording). Continuous recording Daily recording When selecting one out of these two, we should consider our use case and the pricing. Then, we have the option Override settings where we can override settings. By default, we get one override as shown in the bellow. According to our use case we can remove it or add more. Next, we can select existing role or let to create a new role for this service. It's under Data governance. Next, we can select an existing s3 bucket or let to create a new s3 bucket for storing configuration history and snapshots. It's under Delivery channel. Then, we have optional setting to set up SNS topic. I'm not selecting a SNS topic here and hit Next. Next, we come into the second step, where we have to Rules. I'm selecting restricted-ssh rule which is an AWS managed rule. However, We can create Custom Rules using AWS Lambda for specific use cases. Then, hit the Next and we come into the third step where we can review. If everything is fine, we can hit Confirm. Next, it will be shown as bellow. For my account currently, there are no noncompliant rules or resources. Therefore, I'm launch an EC2 instance allowing SSH access from any IP. Next, again check AWS config dashboard. If it's same as it was earlier, refresh after some time. Then, we'll be able to see it like this. Note that now we can see that there are one noncompliant rule and one noncompliant resource. We can use Aggregators to collect data across multiple accounts/regions (if we're using AWS Organizations).
AWS Config is the most comprehensive service for tracking configuration changes and compliance.
Key Features:
Resource Configuration Tracking: Monitors and records configurations of supported AWS resources over time.
Change History: Stores historical configuration data and changes.
Compliance Auditing: Uses Config Rules to assess compliance with desired configurations.
Automatic Remediation: Triggers AWS Systems Manager Automation to correct non-compliant resources.
Setup Steps:
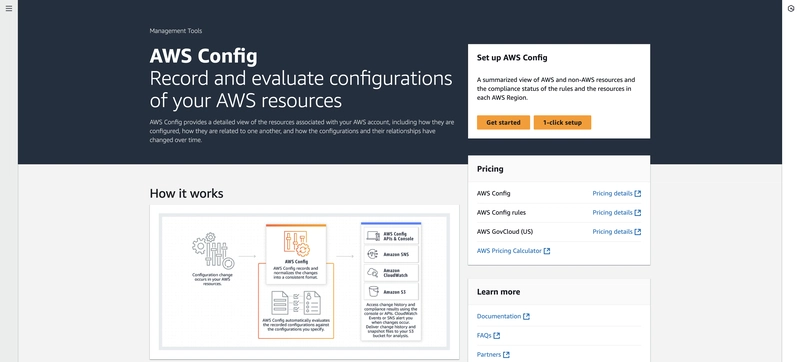
- First, go to AWS Config. If it's not enabled, it will be shown as bellow. Hit Get started.
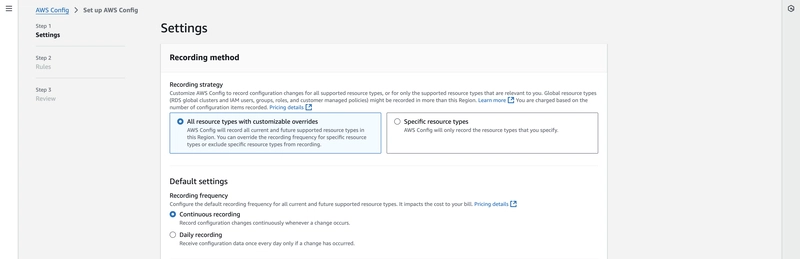
- Then, we get into the first step and we have to select Recording strategy. There are two options from which one should be selected. I'm selecting the first option (All resource types with customisable overrides).
- All resource types with customisable overrides
- Specific resource type
When selecting one out of these two, we should consider our use case and the pricing.
- Next, we have to select Recording frequency. Here also, there are two options from which one should be selected. Here also, I'm selecting the first option (Continuous recording).
- Continuous recording
- Daily recording
When selecting one out of these two, we should consider our use case and the pricing.
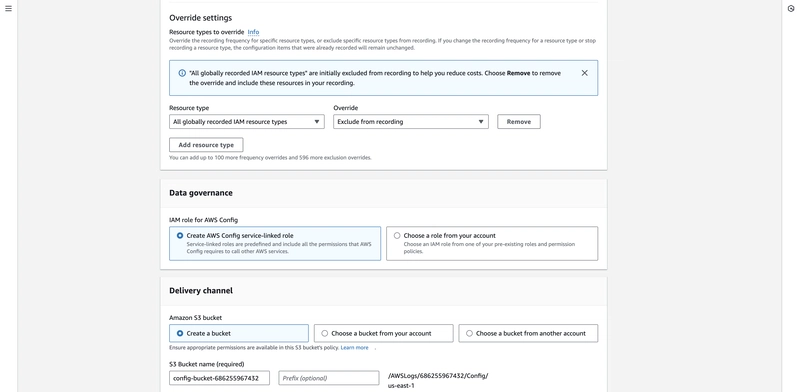
Then, we have the option Override settings where we can override settings. By default, we get one override as shown in the bellow. According to our use case we can remove it or add more.
Next, we can select existing role or let to create a new role for this service. It's under Data governance.
Next, we can select an existing s3 bucket or let to create a new s3 bucket for storing configuration history and snapshots. It's under Delivery channel.
- Then, we have optional setting to set up SNS topic.
I'm not selecting a SNS topic here and hit Next.
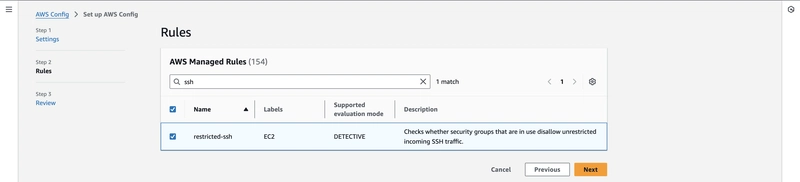
Next, we come into the second step, where we have to Rules. I'm selecting restricted-ssh rule which is an AWS managed rule. However, We can create Custom Rules using AWS Lambda for specific use cases.
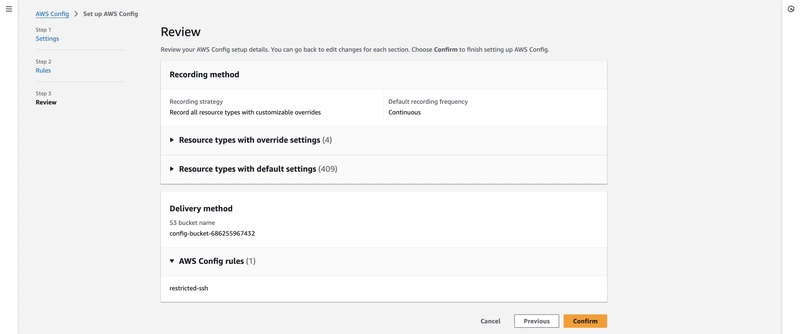
- Then, hit the Next and we come into the third step where we can review. If everything is fine, we can hit Confirm.
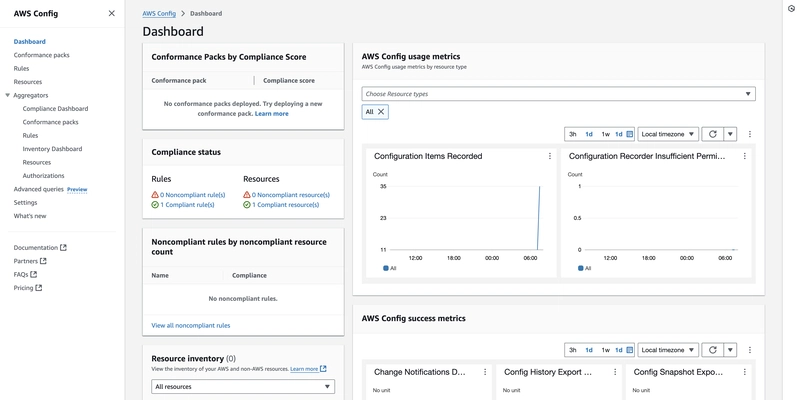
- Next, it will be shown as bellow.
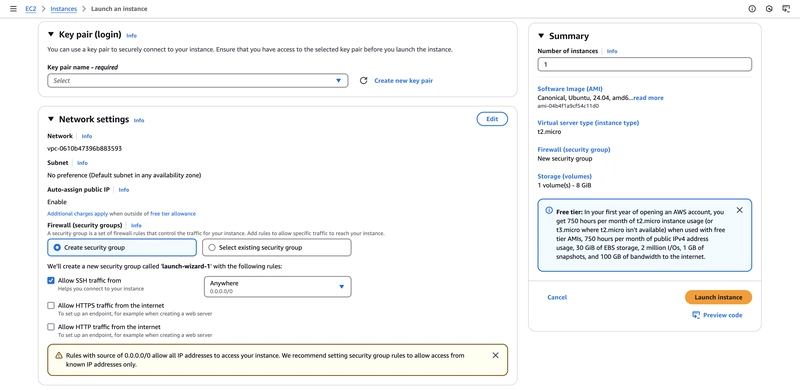
- For my account currently, there are no noncompliant rules or resources. Therefore, I'm launch an EC2 instance allowing SSH access from any IP.
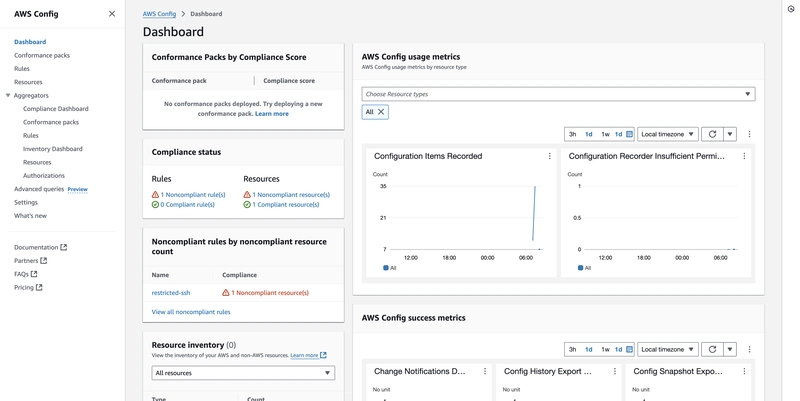
- Next, again check AWS config dashboard. If it's same as it was earlier, refresh after some time. Then, we'll be able to see it like this. Note that now we can see that there are one noncompliant rule and one noncompliant resource.
- We can use Aggregators to collect data across multiple accounts/regions (if we're using AWS Organizations).












































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)
























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)