How to Share Financial Reports Securely Online
Writing Highlights Secure financial reports to prevent breaches. PDFs ensure integrity and security. Use trusted tools for PDF to Word conversion. Reapply encryption after editing. Use AES-256 encryption and strong passwords. Restrict access and track usage with audit trails. Within the digital arena of today, financial reports are prone to dangerous exposure to such information capable of inflicting extreme financial and reputational devastation. Protecting these reports has, therefore, become an increasing concern in this age where businesses are greatly reliant on digital communication. Uncontrolled file-sharing contributes to innumerable risks such as inter alia, breach of data confidentiality and security, unauthorized access, or financial fraud. Cybercriminals resort to hacking financial documents to purloin confidential information, thereby necessitating secure sharing practices. Failure to implement appropriate security could render an organization subject to data protection legislation and encourage enforcement action against it. Protection of financial reports necessitates confidentiality and immunity against any form of infestation, which in turn demands the business to perform such best practices as encrypting, password-protecting, and controlling access. Well-chosen file formats, secure sharing platforms, and digital signatures create additional layers of protection. Complying with such strategies allows the organization to protect and keep the flow of financial data while carrying on with efficient collaboration. Choosing the Right File Format for Security By undertaking the steps outlined here, you should be able to convert and modify financial reports without concerns for security or accuracy. Reasons for PDF Being the Most Widely Used for Financial Reports PDF or Portable Document Format has been the widely accepted format for sharing financial reports as it guarantees the integrity and security of the documents. It retains the exact layout of the work on different platforms, ensuring that the financial data appears neat and professional. Moreover, there are PDF features that provide encryption and password protection against unauthorized alteration. Nearly 85% of businesses rely on PDF file formats to share information for their ability to maintain the integrity and formatting of the document. This property makes it particularly valuable for financial reports, in which accuracy and protection from being tampered with are very important. How to Securely Change PDF to Word? Security of information and accurate formatting are paramount in transforming financial reports. With these notes in mind, here are some general tips to change PDF to DOC securely: Employ reputable conversion tools: Choose proven software that offers encryption during the conversion process, thus securing sensitive financial data. Check conversion for formatting errors: Ensure that during conversion, tables, financial statements, and figures are kept whole from misinterpretation. Avoid public or unverified online converters: Free online tools might offer the convenience of conversion but they may store or disclose your confidential information. On the other hand, a professional alternative with data protection protocols is recommended. Reapplying Security After Conversion Once the necessary edits are done, security measures should be reapplied before sending the document. The Word file should be converted back into PDF format, with password protection added, and encryption ensured to protect the report from tampering. By following these recommendations, organizations can promote the integrity of financial data while permitting modification when required. Secure File Encryption and Password Protection Encryption and password protection are important for restricting access to unauthorized users attempting to read sensitive data on financial reports. Otherwise, financial documents remain open to integrity breaches and unauthorized modification. Password Protection for Financial Reports The securing of financial reports begins by implementing password protection. When applying password protection to a financial report: Password complexity is maximized through the use of the uppercase alphabet, lowercase alphabet, numbers, and special characters in combinations. Avoid using any words that can be easily related to you or information that is easily accessible to others. Safely keep your passwords, preferably in a password manager, to ensure they cannot be lost or shared unauthorizedly. Strong Encryption Methods (AES-256) Will Be Implemented With encryption, another layer of protection is rendered to provide the maximum possible protection to financial reports against unauthorized viewing. The choice of the AES-256 encryption standard is mostly recommended owing to the following features: It is a military-grade encryption that

Writing Highlights
- Secure financial reports to prevent breaches.
- PDFs ensure integrity and security.
- Use trusted tools for PDF to Word conversion.
- Reapply encryption after editing.
- Use AES-256 encryption and strong passwords.
- Restrict access and track usage with audit trails.
Within the digital arena of today, financial reports are prone to dangerous exposure to such information capable of inflicting extreme financial and reputational devastation. Protecting these reports has, therefore, become an increasing concern in this age where businesses are greatly reliant on digital communication.
Uncontrolled file-sharing contributes to innumerable risks such as inter alia, breach of data confidentiality and security, unauthorized access, or financial fraud. Cybercriminals resort to hacking financial documents to purloin confidential information, thereby necessitating secure sharing practices. Failure to implement appropriate security could render an organization subject to data protection legislation and encourage enforcement action against it.
Protection of financial reports necessitates confidentiality and immunity against any form of infestation, which in turn demands the business to perform such best practices as encrypting, password-protecting, and controlling access. Well-chosen file formats, secure sharing platforms, and digital signatures create additional layers of protection. Complying with such strategies allows the organization to protect and keep the flow of financial data while carrying on with efficient collaboration.
Choosing the Right File Format for Security
By undertaking the steps outlined here, you should be able to convert and modify financial reports without concerns for security or accuracy.
Reasons for PDF Being the Most Widely Used for Financial Reports
PDF or Portable Document Format has been the widely accepted format for sharing financial reports as it guarantees the integrity and security of the documents. It retains the exact layout of the work on different platforms, ensuring that the financial data appears neat and professional. Moreover, there are PDF features that provide encryption and password protection against unauthorized alteration.
Nearly 85% of businesses rely on PDF file formats to share information for their ability to maintain the integrity and formatting of the document. This property makes it particularly valuable for financial reports, in which accuracy and protection from being tampered with are very important.
How to Securely Change PDF to Word?
Security of information and accurate formatting are paramount in transforming financial reports. With these notes in mind, here are some general tips to change PDF to DOC securely:
Employ reputable conversion tools: Choose proven software that offers encryption during the conversion process, thus securing sensitive financial data.
Check conversion for formatting errors: Ensure that during conversion, tables, financial statements, and figures are kept whole from misinterpretation.
Avoid public or unverified online converters: Free online tools might offer the convenience of conversion but they may store or disclose your confidential information. On the other hand, a professional alternative with data protection protocols is recommended.
Reapplying Security After Conversion
Once the necessary edits are done, security measures should be reapplied before sending the document. The Word file should be converted back into PDF format, with password protection added, and encryption ensured to protect the report from tampering. By following these recommendations, organizations can promote the integrity of financial data while permitting modification when required.
Secure File Encryption and Password Protection
Encryption and password protection are important for restricting access to unauthorized users attempting to read sensitive data on financial reports. Otherwise, financial documents remain open to integrity breaches and unauthorized modification.
Password Protection for Financial Reports
The securing of financial reports begins by implementing password protection. When applying password protection to a financial report:
Password complexity is maximized through the use of the uppercase alphabet, lowercase alphabet, numbers, and special characters in combinations.
Avoid using any words that can be easily related to you or information that is easily accessible to others.
Safely keep your passwords, preferably in a password manager, to ensure they cannot be lost or shared unauthorizedly.
Strong Encryption Methods (AES-256) Will Be Implemented
With encryption, another layer of protection is rendered to provide the maximum possible protection to financial reports against unauthorized viewing. The choice of the AES-256 encryption standard is mostly
recommended owing to the following features:
It is a military-grade encryption that renders decryption an impossible invention unless the correct key is provided.
Even if the encrypted financial reports were intercepted during transmission, they would stay secure.
Numerous document management tools and secure cloud storage providers support AES-256 encryption.
Setting Password Protection and Encryption in PDF Tools
Here is how you can protect your financial reports in the PDF format:
Password Protect: Use any trusted PDF editor to apply password protection.
Encrypt: Use the encryption settings and select AES-256 for maximum security.
Access: Set different levels of access (such as editing, printing, or copying restrictions).
Best Practices for Secure File Encryption
Change the security password and encryption key regularly.
For transferring encrypted files, do not rely on non-secure channels; instead, use the encrypted email or secure cloud platform.
Encryption should be applied before uploading any financial report into the shared storage.
Through strong encryption and password protection, the financial data of any organization could be made safe from cyber threats, unauthorized access, and data breaches.
Safe Online Sharing Methods
Sharing financial reports online needs to ensure the utmost security to prevent unauthorized access and data breaches. Controlled access to sensitive financial data can be maintained through encryption and secure transmission. The key strategies to ensure safe online sharing are listed below.
Using Secure Cloud Storage Services with Access Controls
Cloud storage is an excellent solution to securely store and share financial reports, provided it is configured adequately. Select a vendor that offers strong encryption, multi-factor authentication, and audit logs.
Access Controls: Limit document access to sanctioned users only with related permissions subjected to roles assigned (exclusively view, edit, download, etc.).
End-to-end encryption: Keep files encrypted throughout storage and transfer to avoid unwanted interceptions.
Audit Trails: Enable tracking features that track who accessed, edited, or downloaded the reports.
Avoid free or unverified cloud services, which usually implement weak security measures. With these, financial data will be at serious risk.
Restricting Sharing Options
Rather than send financial reports as unrestricted files, use controlled sharing features to limit exposure.
View-only mode would prevent recipients from downloading, copying, or editing financial documents.
Set automatic expiration dates for access links, limiting their time of exposure.
Permission-based access will only grant others editing access on a need basis.
These methods will help to mitigate the risks against unauthorized distribution or data leaks.
Best Secure Email Practices
Email is still an acceptable mode of sharing financial reports, but security must be guaranteed to avert interception.
End-to-End Encryption: Secure email services and/or secure attachments are a must, ensuring only the intended recipient can access the data.
Do not attach to Plain Email: Instead of attaching files to emails directly, send secure cloud links with restricted access.
Password-Protect Attachments: If email sharing must happen, encrypt files with strong passwords and share the password through different means.
Never email unprotected financial documents, as email servers can be open to breach.
Using Secure File Transfer Protocols (SFTP)
Most standard file-sharing techniques cannot manage large or extremely confidential financial reports. They are best served by SFTP or Secure File Transfer Protocol.
Encrypted Data Transmission: In contrast to the typical FTP, SFTP encrypts data before transfers, offering a high level of protection.
Authentication Measures: All file access requires a login credential or SSH keys, preventing unauthorized use.
Grants Better Access Control for Manageable File: Create exact permissions for different users.
It is impossible with SFTP to transfer documents from unsecured channels and use proper financial documentation internally.
Digital Rights Management Application
Digital Rights Management comes with added protection layers for the most sensitive financial reports.
Restrains Printing & Copying: Prevents unauthorized copies of financial reports.
Track Access to Document: It keeps a record of who opened the document and when to mitigate potential risks.
Deny Access Remotely: Allows businesses to revoke access if they find unauthorized sharing has taken place.
DRM provides more control over financial reports even after they are shared.
Digital Signatures and Watermarking for Integrity
Companies can keep their financial reports secure and make sure that those reports are guarded by the life cycle integrity of access controls, and audit trails, where digital signatures, waters, and tamper-evident measures have included parts.
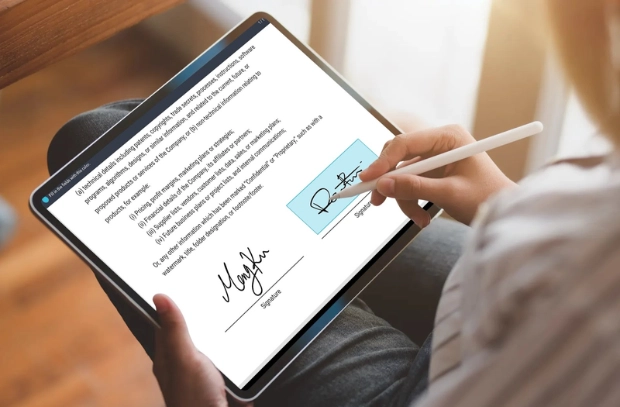
Using Digital Signatures to Authenticate Financial Statements
Digital signatures are the electronic equivalents of handwritten signatures and guarantee that the financial report is genuine and unaltered. Through the application of the digital signature, the sender asserts the document's origin, and the recipients can assure themselves of non-tampering since signing.
It lends a very high degree of trust and security to the transaction, especially in financial reports, since any change to the computerized document after signing would cause the signature to be deemed invalid and would inform the recipients of possible fraud.
Ensuring Document Authenticity via Tamper Proofing
Moving beyond digital signatures and watermarks, other tamper-proof measures can be used to guarantee the integrity of financial reports. A common practice is to make use of hash values or checksums, which are unique codes derived from the contents of a document. Any alteration in the contents of the report will yield a change in its hash value, thus indicating that tampering has occurred.
Secure Access Control for Enhanced Integrity
Secure access control ensures that only approved individuals will be permitted to view or edit the financial reports. Role-based access management permits organizations to designate certain privileges to particular users, thereby conveniently restricting their authority to edit, copy, or print sensitive reports. Thus, access is to be restricted based on the criteria of 'need-to-know', which lessens the risk of unauthorized distribution or manipulation of the data.
Audit Trails for Monitoring Changes
Another important measure for guaranteeing document integrity is the development of audit trails. The audit trails can record every action that is accomplished within a document: who accessed the document, at what time it was accessed, and what changes were made. This level of trial is quite valuable along compliance lines, especially in the finance industries, where regulations call for a clear account of the data lifecycle.
The audit trail stands for a clear traceable record of the whole lifecycle of the document, ensuring that organizations can trace any unauthorized acts.
Bottom Line
The utmost imperative is securing financial reports from breaches, hacking, and data tampering. Strong encryption, password usage, as well as secure sharing methods are the best ways to keep any data leak. All these should be carried out with regulatory compliance. Rightly chosen file formats like PDF ensure the integrity of a document while tools like digital signatures, watermarks, and audit trails ensure security and traceability.
Through such best practices, companies can thus disseminate their financial reports efficiently and without any compromise as far as confidentiality, accuracy, or trust is concerned.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)

























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)





































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)