AWS Security Tools for Your Environment.
Amazon Web Services enables organizations to build and scale applications quickly and securely. However, continuously adding new tools and services introduces new security challenges. According to reports, 70 percent of enterprise IT leaders are concerned about how secure they are in the cloud and 61 percent of small- to medium-sized businesses (SMBs) believe their cloud data is at risk. AWS provides security tools designed to improve both account security and application and service security. Top 6 AWS Account Security Tools 1. AWS Identity and Access Management (IAM): AWS IAM is essential for controlling access to your AWS resources. It enables you to create users and roles with permissions to specific resources in your AWS environment. Always assigning least-privilege permissions to these users and roles minimizes the impact of a breach where an attacker has gained access. AWS IAM also has multi-factor authentication and supports single sign-on (SSO) access to further secure and centralize user access. Use the IAM policy simulator to test and troubleshoot the extent of permissions you assign to your users and roles, and make sure you're following the principle of least privilege when configuring your IAM permissions. 2. Amazon GuardDuty: Amazon GuardDuty uses machine learning to look for malicious activity in your AWS environments. It combines your CloudTrail event logs, VPC Flow Logs, S3 event logs, and DNS logs to continuously monitor and analyze all activity. GuardDuty identifies issues such as privilege escalation, exposed credentials, and communication with malicious IP addresses and domains. It can also detect when your EC2 instances are serving malware or mining bitcoin. In addition, GuardDuty can detect anomalies in your access patterns such as API calls in new regions. Pricing is based on the amount of data analyzed, so costs will increase linearly as your AWS environments grow. 3. Amazon Macie: Amazon Macie discovers and protects your sensitive data stored in AWS S3 buckets. It first identifies sensitive data in your buckets, such as personally-identifiable information or personal health information, through discovery jobs. You can schedule these jobs to monitor new data added to your buckets. After it finds sensitive data, Macie continuously evaluates your buckets and alerts you when a bucket is unencrypted, is publicly accessible, or is shared with AWS accounts outside of your organization. Macie’s pricing scales with the amount of data it processes and the number of S3 buckets it monitors. 4. AWS Config: AWS Config records and continuously evaluates your AWS resource configuration. This includes keeping a historical record of all changes to your resources, which is useful for compliance with legal requirements and your organization’s policies. AWS Config evaluates new and existing resources against rules that validate certain configurations. For example, if all EC2 volumes must be encrypted, AWS Config can detect non-encrypted volumes and send a notification. In addition, it can also execute remediation actions such as encrypting the volume or deleting it. Config is configured per region, so it’s essential to enable AWS Config in all regions to ensure all resources are recorded, including in regions where you don’t expect to create resources. 5. AWS CloudTrail: AWS CloudTrail tracks all activity in your AWS environment. It records all actions a user executes in the AWS console and all API calls as events. You can view and search these events to identify unexpected or unusual requests in your AWS environment. CloudTrail is enabled by default in all AWS accounts since August 2017. If you also use AWS Organizations to manage multiple accounts, you can enable CloudTrail within the organization on all existing accounts. 6. Security Hub: AWS Security Hub combines information from all the above services in a central, unified view. It collects data from all security services from multiple AWS accounts and regions, making it easier to get a complete view of your AWS security posture. In addition, Security Hub supports collecting data from third-party security products. Security Hub is essential to providing your security team with all the information they may need. A key feature of Security Hub is its support for industry recognized security standards including the CIS AWS Foundations Benchmark and Payment Card Industry Data Security Standard (PCI DSS). Combine Security Hub with AWS Organizations for the simplest way to get a comprehensive security overview of all your AWS accounts. Now that we have addressed the top account security tools, let’s focus on the top four AWS application sSecurity tTools you should consider. Top 4 AWS Application Security Tools 1. Amazon Inspector: Amazon Inspector is a security assessment service for applications deployed on EC2. These assessments include network access, common vulnerabilities and exposures (CVEs), Center for Internet Security (CIS) benc
Amazon Web Services enables organizations to build and scale applications quickly and securely. However, continuously adding new tools and services introduces new security challenges. According to reports, 70 percent of enterprise IT leaders are concerned about how secure they are in the cloud and 61 percent of small- to medium-sized businesses (SMBs) believe their cloud data is at risk.
AWS provides security tools designed to improve both account security and application and service security.
Top 6 AWS Account Security Tools
1. AWS Identity and Access Management (IAM):
AWS IAM is essential for controlling access to your AWS resources. It enables you to create users and roles with permissions to specific resources in your AWS environment. Always assigning least-privilege permissions to these users and roles minimizes the impact of a breach where an attacker has gained access. AWS IAM also has multi-factor authentication and supports single sign-on (SSO) access to further secure and centralize user access.
Use the IAM policy simulator to test and troubleshoot the extent of permissions you assign to your users and roles, and make sure you're following the principle of least privilege when configuring your IAM permissions.
2. Amazon GuardDuty:
Amazon GuardDuty uses machine learning to look for malicious activity in your AWS environments. It combines your CloudTrail event logs, VPC Flow Logs, S3 event logs, and DNS logs to continuously monitor and analyze all activity. GuardDuty identifies issues such as privilege escalation, exposed credentials, and communication with malicious IP addresses and domains. It can also detect when your EC2 instances are serving malware or mining bitcoin.
In addition, GuardDuty can detect anomalies in your access patterns such as API calls in new regions. Pricing is based on the amount of data analyzed, so costs will increase linearly as your AWS environments grow.
3. Amazon Macie:
Amazon Macie discovers and protects your sensitive data stored in AWS S3 buckets. It first identifies sensitive data in your buckets, such as personally-identifiable information or personal health information, through discovery jobs. You can schedule these jobs to monitor new data added to your buckets. After it finds sensitive data, Macie continuously evaluates your buckets and alerts you when a bucket is unencrypted, is publicly accessible, or is shared with AWS accounts outside of your organization.
Macie’s pricing scales with the amount of data it processes and the number of S3 buckets it monitors.
4. AWS Config:
AWS Config records and continuously evaluates your AWS resource configuration. This includes keeping a historical record of all changes to your resources, which is useful for compliance with legal requirements and your organization’s policies. AWS Config evaluates new and existing resources against rules that validate certain configurations. For example, if all EC2 volumes must be encrypted, AWS Config can detect non-encrypted volumes and send a notification. In addition, it can also execute remediation actions such as encrypting the volume or deleting it.
Config is configured per region, so it’s essential to enable AWS Config in all regions to ensure all resources are recorded, including in regions where you don’t expect to create resources.
5. AWS CloudTrail:
AWS CloudTrail tracks all activity in your AWS environment. It records all actions a user executes in the AWS console and all API calls as events. You can view and search these events to identify unexpected or unusual requests in your AWS environment.
CloudTrail is enabled by default in all AWS accounts since August 2017. If you also use AWS Organizations to manage multiple accounts, you can enable CloudTrail within the organization on all existing accounts.
6. Security Hub:
AWS Security Hub combines information from all the above services in a central, unified view. It collects data from all security services from multiple AWS accounts and regions, making it easier to get a complete view of your AWS security posture. In addition, Security Hub supports collecting data from third-party security products. Security Hub is essential to providing your security team with all the information they may need.
A key feature of Security Hub is its support for industry recognized security standards including the CIS AWS Foundations Benchmark and Payment Card Industry Data Security Standard (PCI DSS).
Combine Security Hub with AWS Organizations for the simplest way to get a comprehensive security overview of all your AWS accounts.
Now that we have addressed the top account security tools, let’s focus on the top four AWS application sSecurity tTools you should consider.
Top 4 AWS Application Security Tools
1. Amazon Inspector:
Amazon Inspector is a security assessment service for applications deployed on EC2. These assessments include network access, common vulnerabilities and exposures (CVEs), Center for Internet Security (CIS) benchmarks, and common best practices such as disabling root login for SSH and validating system directory permissions on your EC2 instances.
Based on data provided on an agent application you can install on your EC2 VMs, Inspector generates a report with a detailed list of security findings prioritized by severity. Run Inspector as part of a gated check in your deployment pipeline to assess your applications’ security before deploying to production.
2. AWS Shield:
AWS Shield is a fully-managed distributed denial-of-service (DDoS) protection service. Shield is enabled by default as a free standard service with protection against common DDoS attacks against your AWS environment.
Shield Advanced goes a step further by integrating with AWS WAF to prevent a wide variety of malicious traffic from reaching your websites and applications. It can cover multiple accounts under an organization to ensure that all of your organization's internet-facing endpoints are protected from attackers.
3. AWS Web Application Firewall:
AWS Web Application Firewall (WAF) monitors and protects applications and APIs built on services such as CloudFront, API Gateway, and AppSync. You can block access to your endpoints based on different criteria such as the source IP address, the request’s origin country, values in headers and bodies, and more (i.e, you can enable rate limiting, only allowing a certain number of requests per IP
The AWS Marketplace also includes a set of managed rules you can associate with your WAF, along with 3rd party managed rules from leading security vendors.
4. AWS Secrets Manager:
AWS Secrets Manager is a managed service where you can store and retrieve sensitive information such as database credentials, certificates, and tokens. Use fine-grained permissions to specify exact actions an entity can perform on the secrets, such as creating, updating, deleting, or retrieving secrets.
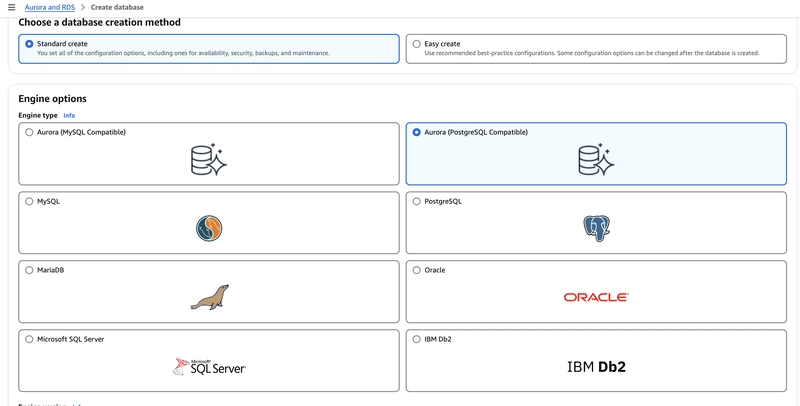
Secrets Manager also supports automatic rotation for AWS services such as Amazon Relational Database Service (RDS). Through Lambda functions, secrets for other services can be automatically rotated as well. Never store your sensitive information in source control management systems, such as Git. Always use a tool like Secrets Manager.
Thank you for your time.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)

























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)




.jpg?#)
































_Christophe_Coat_Alamy.jpg?#)






































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)