Threat Actors Trojanize Popular Versions of Games To Infect Systems Bypassing Evasion Techniques
In a sophisticated cyberattack campaign dubbed “StaryDobry,” threat actors have exploited popular games to distribute malicious software, targeting users worldwide. The campaign, first detected on December 31, 2024, leveraged trojanized versions of games such as BeamNG.drive, Garry’s Mod, and Dyson Sphere Program, distributed via torrent sites. These repackaged games contained a hidden payload designed to […] The post Threat Actors Trojanize Popular Versions of Games To Infect Systems Bypassing Evasion Techniques appeared first on Cyber Security News.

In a sophisticated cyberattack campaign dubbed “StaryDobry,” threat actors have exploited popular games to distribute malicious software, targeting users worldwide.
The campaign, first detected on December 31, 2024, leveraged trojanized versions of games such as BeamNG.drive, Garry’s Mod, and Dyson Sphere Program, distributed via torrent sites.
These repackaged games contained a hidden payload designed to bypass detection and install a cryptominer on victims’ systems.
The attackers capitalized on the holiday season’s surge in torrent activity, uploading these malicious game installers as early as September 2024.
While the security analysts at Securelist identified that the victims were primarily located in Russia, Brazil, Germany, Belarus, and Kazakhstan.
The malware’s primary goal was to deploy the XMRig cryptominer, exploiting the high-performance hardware of gaming systems to mine cryptocurrency.
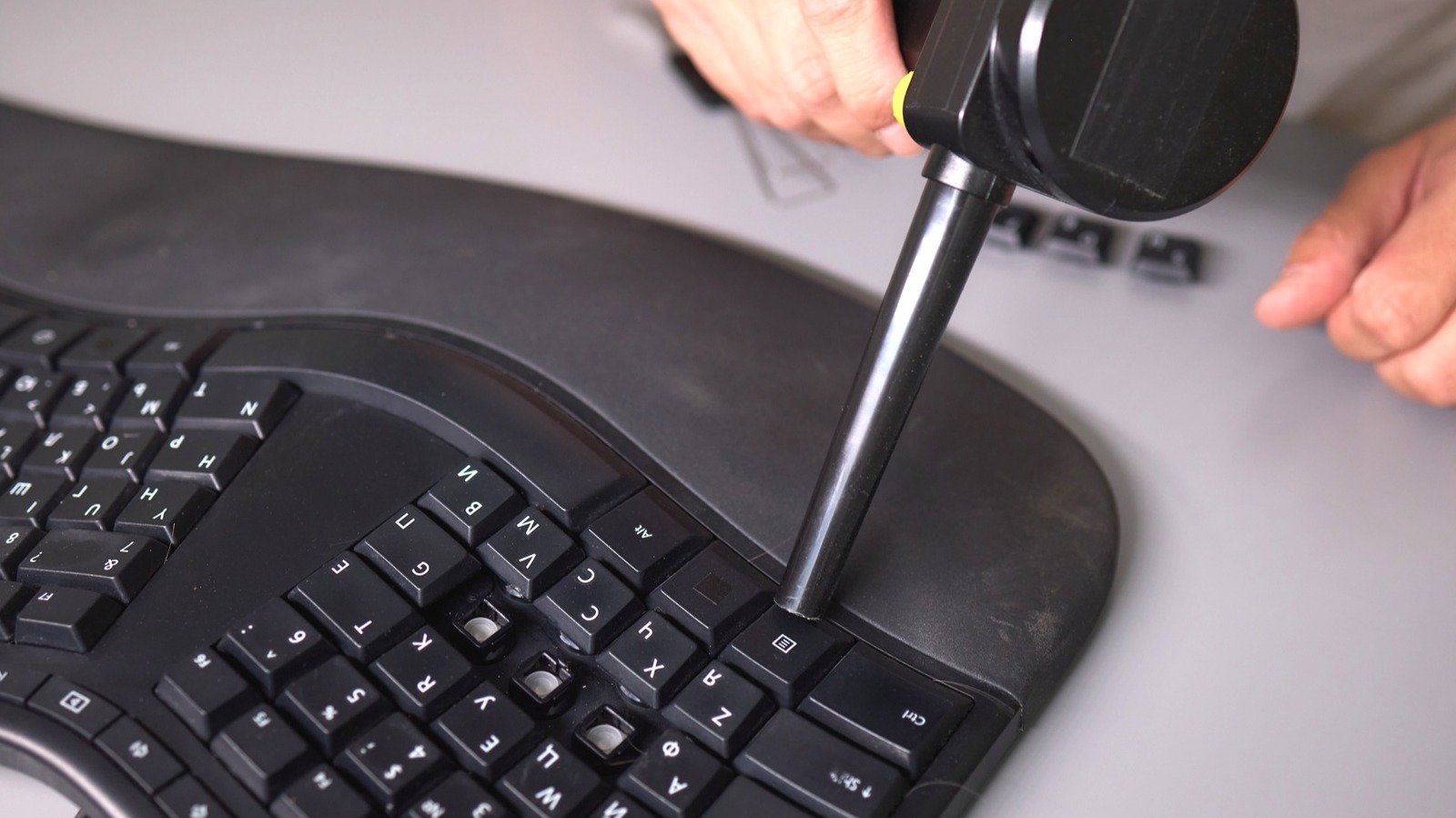
Execution of The Trojanized Installer
The infection chain begins with a seemingly legitimate installer created using Inno Setup. Upon execution, the installer decrypts and extracts malicious files using the AES algorithm with a hard-coded key.
.webp)
Key components include the unrar.dll dropper, which decrypts and executes additional payloads while evading detection by performing anti-debugging checks.
.webp)
These checks scan for sandbox environments or debugging tools like taskmgr.exe and procmon.exe. If detected, the malware halts execution.
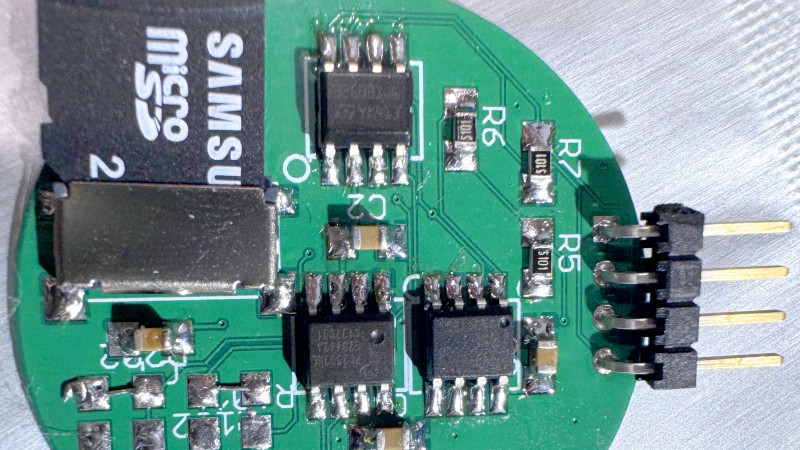
The malware collects system fingerprints by retrieving parameters such as MachineGUID, memory size, processor count, and GPU details.
This information is encoded in Base64 and sent to a command-and-control (C2) server.
The malware then creates two files: %SystemRoot%\%hash%.dat (storing the fingerprint) and %SystemRoot%\%hash%.efi (a decoy file). Here the decompiled installer code responsible for these actions.
.webp)
The final payload, MTX64.exe, is decrypted using AES-128 and disguised as legitimate Windows DLL files by spoofing resource properties such as CompanyName and FileVersion.
The malware further obfuscates its presence by altering file creation timestamps.
.webp)
The XMRig miner implant constructs a predefined command line based on system specifications.
It avoids execution on systems with fewer than eight CPU cores, ensuring optimal mining performance.
Unlike typical mining campaigns that use public pools, this operation hosted its own mining infrastructure to evade detection.
To maintain stealth, the attackers employed DNS-over-HTTPS (DoH) for encrypted communication with their C2 servers.
This tactic obscured network traffic from traditional monitoring tools, complicating detection efforts.
By exploiting user trust in popular games and employing advanced evasion techniques, threat actors have demonstrated their ability to infiltrate systems undetected while maximizing financial gain through cryptomining.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post Threat Actors Trojanize Popular Versions of Games To Infect Systems Bypassing Evasion Techniques appeared first on Cyber Security News.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)

























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)





































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)