Jaguar Land Rover Breached by HELLCAT Ransomware Group using Jira Credentials
Luxury automotive manufacturer Jaguar Land Rover (JLR) has become the latest victim of the rapidly emerging HELLCAT ransomware group, with sensitive internal documents and employee data now exposed on hacking forums. The attack bears the hallmarks of HELLCAT’s sophisticated tactics, which have previously targeted other major corporations, including Telefonica, Schneider Electric, and Pinger. Hudson Rock […] The post Jaguar Land Rover Breached by HELLCAT Ransomware Group using Jira Credentials appeared first on Cyber Security News.

Luxury automotive manufacturer Jaguar Land Rover (JLR) has become the latest victim of the rapidly emerging HELLCAT ransomware group, with sensitive internal documents and employee data now exposed on hacking forums.
The attack bears the hallmarks of HELLCAT’s sophisticated tactics, which have previously targeted other major corporations, including Telefonica, Schneider Electric, and Pinger.
Hudson Rock researchers reported that the threat actor identified as “Rey” claimed responsibility for the breach on a notorious hacking forum, stating that approximately 700 internal JLR documents had been compromised.
The leaked data reportedly includes development logs, tracking data, proprietary source codes, and an extensive employee dataset containing usernames, email addresses, display names, and time zone information.
“The leak includes around 700 internal documents and a compromised employee dataset exposing sensitive information such as username, email, display name, time zone, and more,” a Threat actor announced on the forum.
Security researchers confirm that some of the exposed data contains information about legitimate JLR employees from global operations, raising significant concerns about potential identity theft and targeted phishing campaigns.
Under the nickname “APTS,” a second threat actor surfaced on the forum with a thread of his own, claiming to have gained access to JLR’s systems and stolen an even greater quantity of data from the organization by using the same infostealer credentials.
An additional batch of data, estimated at an even more concerning 350 gigabytes, was leaked by “APTS” and contained information not seen in Rey’s data dump.
Attack Methodology: Jira Exploitation
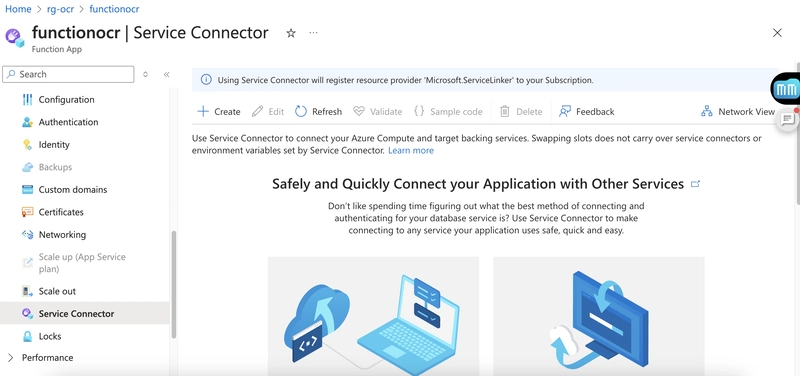
HELLCAT’s attack against JLR appears to follow their established playbook of targeting Atlassian Jira instances using stolen credentials.
According to Hudson Rock’s cybercrime intelligence database, which includes over 30,000,000 systems infected with Infostealers, thousands of firms have Jira-related compromised credentials from Infostealer infections.
The group likely gained initial access through compromised Jira credentials, similar to their recent attack against Telefonica where they exploited the telecommunications company’s Jira platform at “jira.globalsap.telefonica.com”.
HELLCAT, which emerged in mid-2024, has rapidly established itself as a sophisticated ransomware operation employing advanced tactics, techniques, and procedures (TTPs).
Their multi-stage attack chain typically begins with spear phishing emails or exploitation of public-facing applications to gain initial access.
Once inside a network, HELLCAT deploys a sophisticated series of PowerShell scripts:
This registry modification establishes persistence, ensuring the malware runs each time a user logs in. Subsequent stages involve AMSI bypass techniques and reflective code loading to evade detection.
The final payload typically delivers SliverC2, a command-and-control framework that provides attackers with persistent remote access to compromised systems.
The stolen JLR data poses particular concerns for the automotive manufacturer. The source code and tracking data could potentially expose intellectual property and may contain cloud access keys or passwords that could be leveraged for deeper network penetration.
Cybersecurity experts noted that the most concerning data allegedly stolen is tracking data. This information could be used by a threat actor to find individual customers or sold to groups that intend to do the same.
This breach highlights the growing threat posed by infostealer malware that can harvest credentials from infected devices.
Once such credentials are obtained, they can be weaponized against critical systems like Jira, which often serves as a gateway to an organization’s sensitive information.
As organizations like JLR assess the damage and implement mitigation strategies, cybersecurity experts emphasize the critical importance of multi-factor authentication, regular credential rotation, and comprehensive monitoring to prevent similar breaches.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Jaguar Land Rover Breached by HELLCAT Ransomware Group using Jira Credentials appeared first on Cyber Security News.










































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)




.jpg?#)
































_Christophe_Coat_Alamy.jpg?#)





































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)