BlackLock Ransomware Hacked 40+ Organization Within Two Months
BlackLock ransomware has emerged as one of the most notorious cybersecurity threats of 2025, compromising more than 40 organizations within just two months. The fast-rising ransomware group has targeted victims across multiple sectors, with construction, real estate, and technology industries bearing the brunt of these sophisticated attacks. Operating as a Ransomware-as-a-Service (RaaS) platform, BlackLock has […] The post BlackLock Ransomware Hacked 40+ Organization Within Two Months appeared first on Cyber Security News.

BlackLock ransomware has emerged as one of the most notorious cybersecurity threats of 2025, compromising more than 40 organizations within just two months.
The fast-rising ransomware group has targeted victims across multiple sectors, with construction, real estate, and technology industries bearing the brunt of these sophisticated attacks.
Operating as a Ransomware-as-a-Service (RaaS) platform, BlackLock has quickly positioned itself as a dominant force in the cybercriminal ecosystem through its advanced encryption techniques and aggressive targeting strategies.
.webp)
According to recent attack data, BlackLock has conducted precisely 48 attacks in the first two months of 2025, demonstrating an alarming operational tempo.
The group’s tactics involve encrypting critical organizational data and demanding substantial ransoms for decryption keys, while simultaneously threatening to publish stolen information on their dedicated leak site if demands aren’t met.
DarkAtlas Security researchers identified that BlackLock is actually a rebranded version of the previously known Eldorado ransomware group.
“After facing increased scrutiny from law enforcement, the Eldorado operators have resurfaced under the BlackLock banner with a refined operational model and enhanced capabilities,” noted the DarkAtlas Research Team in their latest threat report.
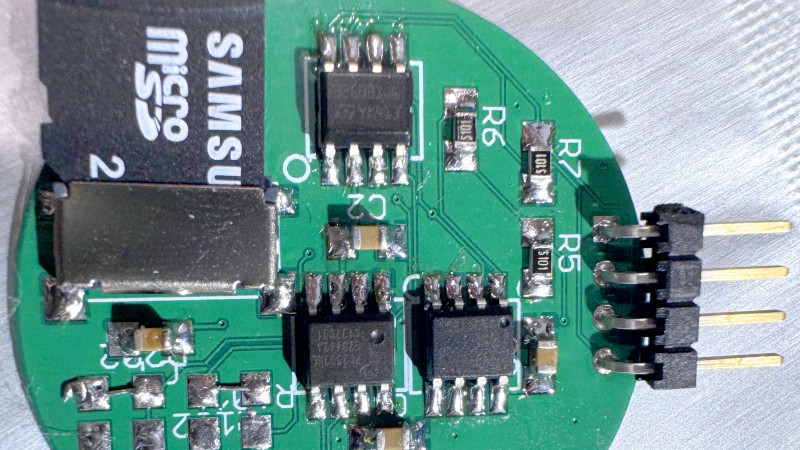
The ransomware employs sophisticated cross-platform capabilities, using Golang to execute attacks on both Windows and Linux systems.
Unlike many competitors who rely on leaked builder sources, BlackLock developers have created their own malware from scratch, indicating a high level of technical expertise within the group.
.webp)
This encryption process transforms files by adding random character strings and appends similarly randomized extensions, creating the distinctive pattern seen in affected systems.
Technical Operations and Infection Chain
The infection process begins when BlackLock operators gain access to target networks, often through compromised credentials or vulnerabilities in internet-facing applications.
Once inside, the ransomware encrypts files using ChaCha20 for file content and RSA-OAEP for key encryption, allowing it to attack files on shared networks via SMB protocols.
After encryption completes, victims find a ransom note titled “HOW_RETURN_YOUR_DATA.TXT” containing payment instructions.
.webp)
The distribution across sectors shows Technology and Miscellaneous industries suffering the highest proportion of attacks, reflecting the group’s strategic targeting of high-value organizations.
Particularly concerning is BlackLock’s recruitment of “traffers” – specialists who drive malicious traffic and establish initial access points.
These individuals play crucial roles in the early stages of attacks, steering potential victims toward compromise.
The group maintains communication through encrypted Telegram channels, making tracking and attribution challenging for security researchers and law enforcement alike.
Organizations are advised to implement robust backup strategies, network segmentation, and comprehensive endpoint protection to mitigate the growing BlackLock threat.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post BlackLock Ransomware Hacked 40+ Organization Within Two Months appeared first on Cyber Security News.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)




































































































.png?#)





.jpg?#)
































_Christophe_Coat_Alamy.jpg?#)






































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)