Chrome Buffer Overflow Vulnerabilities Allow Arbitrary Code Execution & Gain System Access
Google has urgently patched two high-severity heap buffer overflow vulnerabilities in its Chrome browser, CVE-2025-0999, and CVE-2025-1426, that could allow attackers to execute arbitrary code and seize control of affected systems. The vulnerabilities, fixed in Chrome 133.0.6943.126/.127 for Windows/Mac and 133.0.6943.126 for Linux, target the V8 JavaScript engine and GPU components, respectively. Multiple High-Severity Vulnerabilities […] The post Chrome Buffer Overflow Vulnerabilities Allow Arbitrary Code Execution & Gain System Access appeared first on Cyber Security News.

Google has urgently patched two high-severity heap buffer overflow vulnerabilities in its Chrome browser, CVE-2025-0999, and CVE-2025-1426, that could allow attackers to execute arbitrary code and seize control of affected systems.
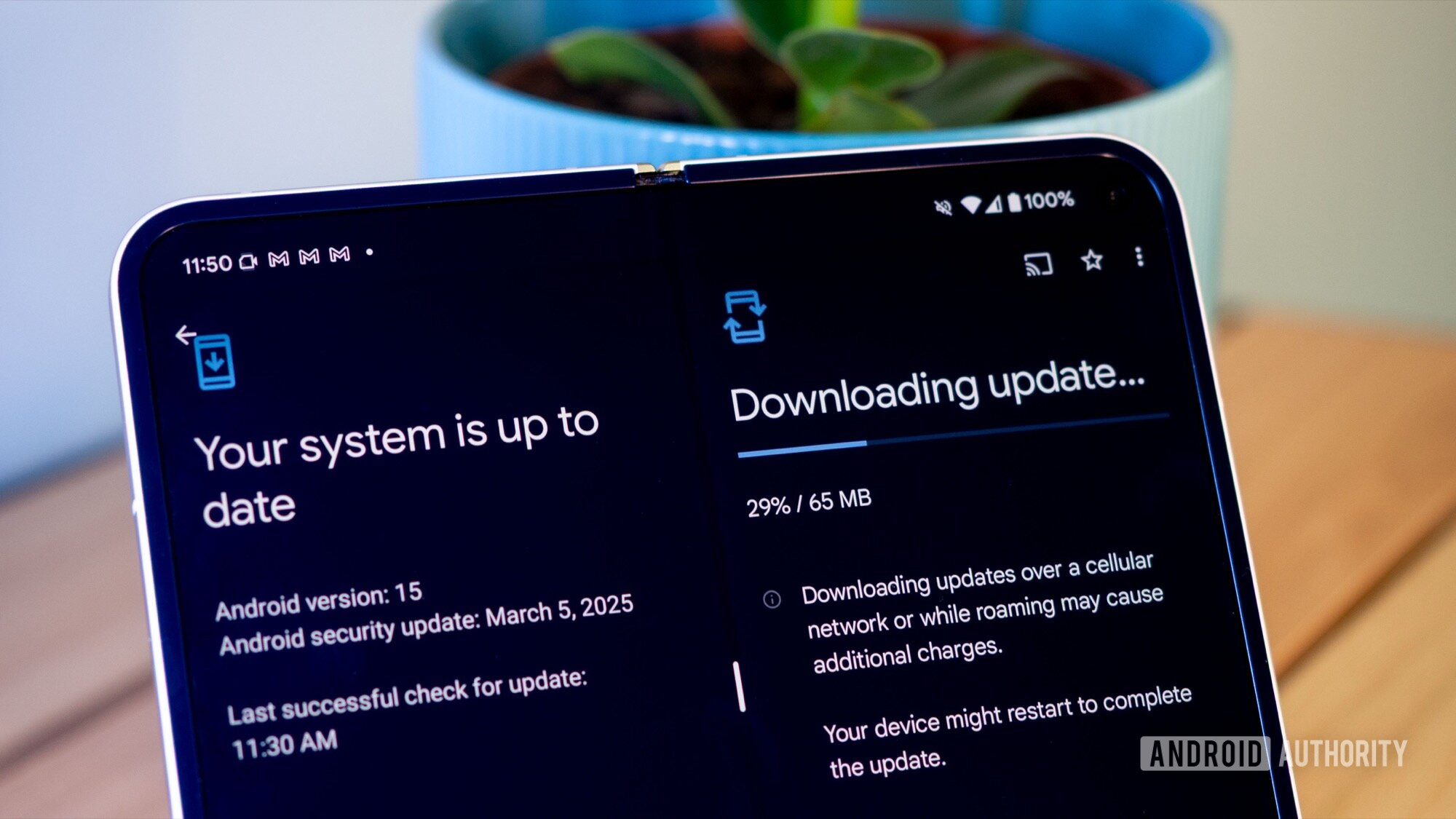
The vulnerabilities, fixed in Chrome 133.0.6943.126/.127 for Windows/Mac and 133.0.6943.126 for Linux, target the V8 JavaScript engine and GPU components, respectively.
Multiple High-Severity Vulnerabilities
The V8 engine vulnerability (CVE-2025-0999) arises from improper memory management when processing JavaScript objects, enabling heap corruption through crafted HTML pages.
Separately, the GPU flaw (CVE-2025-1426) exploits Chrome’s graphics processing unit integration, allowing attackers to overflow buffer limits during rendering operations.
Both vulnerabilities grant remote code execution (RCE) capabilities, potentially enabling full system compromise, data theft, or lateral movement within networks.
Heap buffer overflow vulnerability enables attackers to overwrite dynamically allocated memory regions and execute arbitrary code. This vulnerability arises when programs write data beyond the bounds of memory blocks allocated on the heap a dynamically managed memory area used for runtime data storage.
Another vulnerability is CVE-2025-1006, a medium-severity use-after-free (UAF) vulnerability in Google Chrome’s Network component. Attackers could exploit it by crafting malicious web content to trigger arbitrary code execution, potentially compromising user systems or exfiltrating sensitive data
External researchers have discovered several vulnerabilities. Seunghyun Lee (@0x10n) received an $11,000 bounty for CVE-2025-0999. The team “un3xploitable && GF” is awaiting a reward for CVE-2025-1426. Additionally, researchers from Palo Alto Networks (Tal Keren, Sam Agranat, Eran Rom, Edouard Bochin, and Adam Hatsir) were awarded $4,000 for CVE-2022-4135.
Google has withheld full technical details until most users update, a standard practice to prevent exploit weaponization.
While no active exploitation has been confirmed, the similarities to prior Chrome zero-days, such as CVE-2022-4135, a GPU heap overflow exploited in 2022, heighten concerns. Chrome’s dominance (65% global browser share) makes it a prime target for attackers seeking maximum impact.
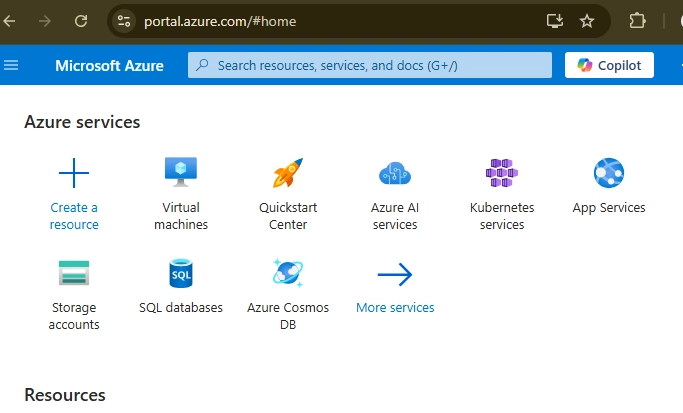
Users must immediately update via Chrome > Help > About Google Chrome, restarting the browser to apply patches. Enterprise administrators should prioritize deploying the update across networks, as delayed patching leaves systems exposed to drive-by download attacks or phishing campaigns delivering exploit code.
As attackers increasingly chain multiple vulnerabilities for systemic breaches, users and organizations cannot afford complacency. With Chrome updates automated by default, vigilance now centers on ensuring update mechanisms function correctly across all devices.
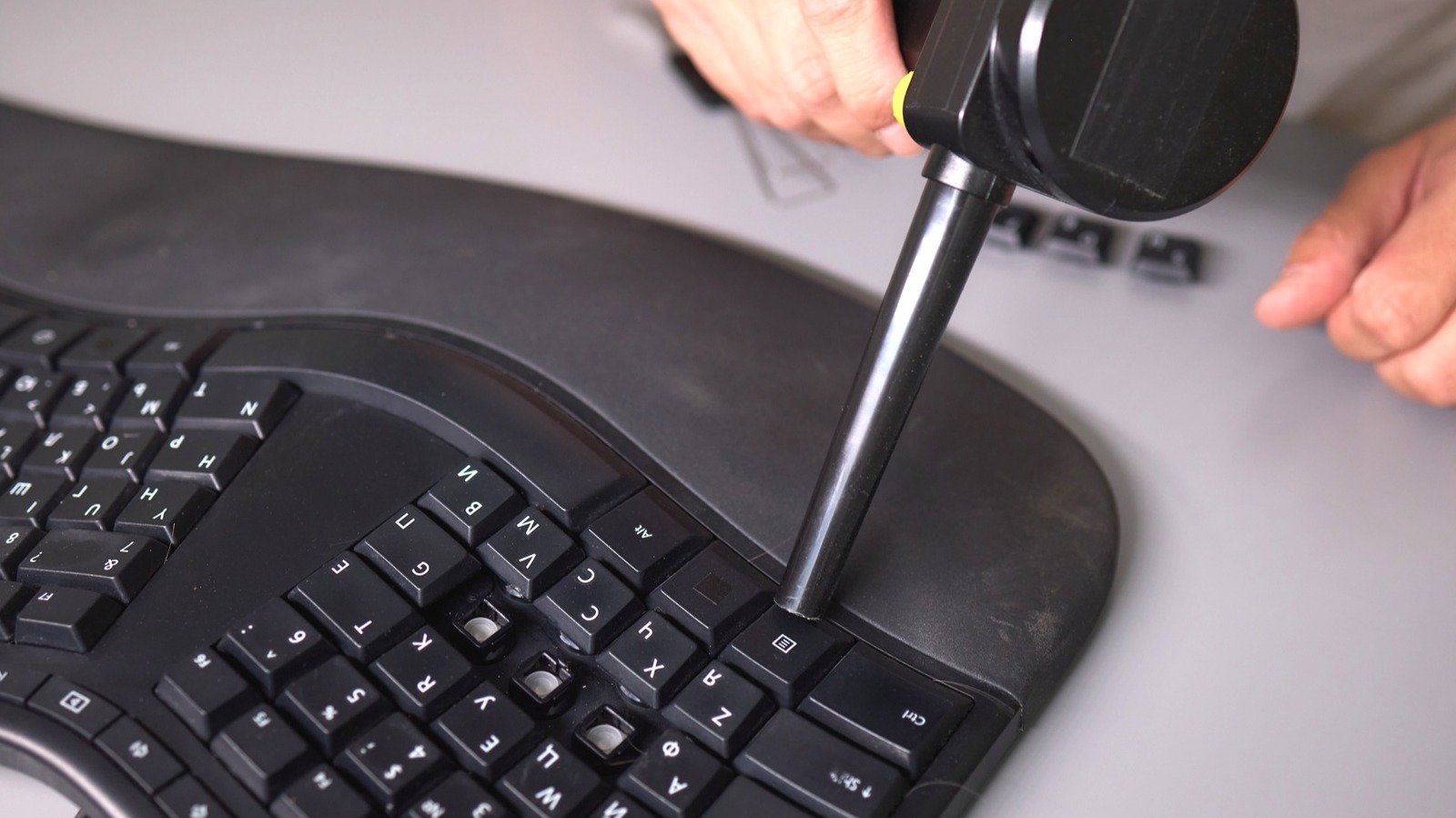
Update Steps for Chrome:
- Open Chrome and click the three-dot menu (top-right).
- Navigate to Help > About Google Chrome.
- Allow the browser to check for updates.
- Click Relaunch if an update is available.
Google continues to credit external researchers through its Vulnerability Rewards Program, having disbursed over $12 million since 2010.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post Chrome Buffer Overflow Vulnerabilities Allow Arbitrary Code Execution & Gain System Access appeared first on Cyber Security News.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)

























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)





































































































.png?#)





.jpg?#)






























_Christophe_Coat_Alamy.jpg?#)




































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)