What is Encryption-as-a-Service?
With cyberattacks growing more sophisticated and data privacy regulations becoming stricter, organizations must rethink how they secure sensitive data. Enter Encryption-as-a-Service (EaaS)—a modern, cloud-driven approach to encrypting data across storage, transit, and usage environments without the operational burden of managing encryption infrastructure internally. What Is Encryption-as-a-Service? Encryption-as-a-Service is a cloud-native security offering that enables businesses to encrypt their data using advanced cryptographic methods. Instead of building and managing in-house encryption systems, companies can now rely on EaaS providers to encrypt files, communications, and databases—while also handling key generation and lifecycle management. Whether you're a startup or a large enterprise, EaaS offers scalable protection tailored to your needs. It ensures that only authorized parties can decrypt and access information, regardless of where or how it's stored. How Does EaaS Function? EaaS works through a straightforward yet secure process: Data Submission: Users upload or transmit data through APIs or secure dashboards. Encryption Process: The service applies industry-standard encryption algorithms and creates unique encryption keys per dataset. Secure Storage or Transmission: Encrypted data is then safely stored in the cloud or sent securely to its destination. Controlled Decryption: Authorized users can decrypt the data through the same EaaS platform using the appropriate credentials or keys. Key Management: The provider oversees the encryption keys—ensuring secure storage, rotation, and disposal. Key Variants of EaaS You Should Know EaaS isn’t a one-size-fits-all solution. It includes multiple encryption strategies to meet varied security needs: Full Disk Encryption: Encrypts entire storage devices to prevent data theft if hardware is lost. File & Field-Level Encryption: Secures individual files or database fields like health records or financial details. End-to-End Encryption: Ensures data remains private throughout its entire journey. Homomorphic Encryption: Enables computations on encrypted data without revealing it. HTTPS & Network-Level Encryption: Secures web traffic and data moving across networks. Why Businesses Are Adopting EaaS Organizations are turning to EaaS for several compelling reasons: Reduced IT Complexity: No need to build or maintain custom encryption systems. Lower Operational Costs: Pay-as-you-go models eliminate the need for upfront investment. Compliance Made Easy: Helps meet regulatory requirements like HIPAA, GDPR, and PCI DSS. Remote Access Flexibility: Cloud delivery allows access to secure services from any location. Limitations to Keep in Mind Despite its advantages, EaaS isn’t without challenges: Performance Impact: Encryption processes can affect application speed. Vendor Dependency: Outages or security issues at the provider’s end could affect access. Key Management Risks: Poor key handling could lead to data exposure. User Workflow Disruption: Employees may face hurdles while working with encrypted data. Conclusion Encryption-as-a-Service has become an essential component of modern cybersecurity strategies. By delivering scalable, reliable, and compliant encryption without the overhead of managing infrastructure, EaaS empowers businesses to focus on growth while safeguarding their data. Though it requires thoughtful implementation, the security and peace of mind it offers make it a worthwhile investment in today’s data-centric world.


With cyberattacks growing more sophisticated and data privacy regulations becoming stricter, organizations must rethink how they secure sensitive data. Enter Encryption-as-a-Service (EaaS)—a modern, cloud-driven approach to encrypting data across storage, transit, and usage environments without the operational burden of managing encryption infrastructure internally.
What Is Encryption-as-a-Service?
Encryption-as-a-Service is a cloud-native security offering that enables businesses to encrypt their data using advanced cryptographic methods. Instead of building and managing in-house encryption systems, companies can now rely on EaaS providers to encrypt files, communications, and databases—while also handling key generation and lifecycle management.
Whether you're a startup or a large enterprise, EaaS offers scalable protection tailored to your needs. It ensures that only authorized parties can decrypt and access information, regardless of where or how it's stored.
How Does EaaS Function?
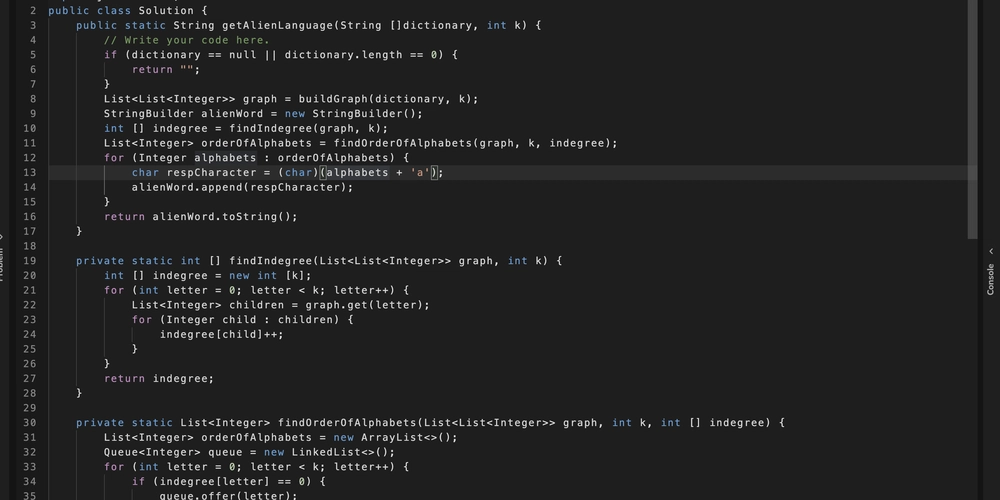
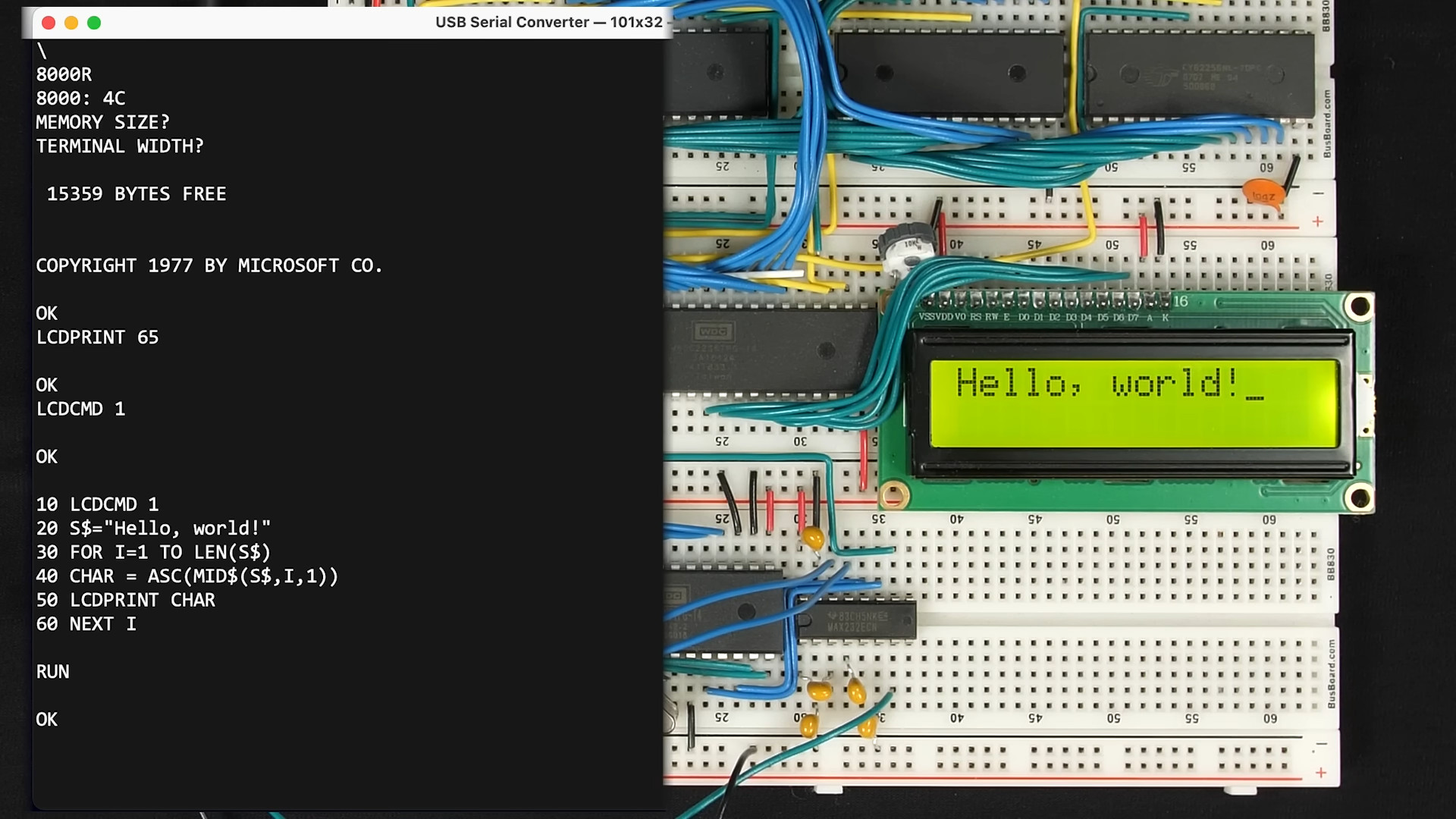
EaaS works through a straightforward yet secure process:
- Data Submission: Users upload or transmit data through APIs or secure dashboards.
- Encryption Process: The service applies industry-standard encryption algorithms and creates unique encryption keys per dataset.
- Secure Storage or Transmission: Encrypted data is then safely stored in the cloud or sent securely to its destination.
- Controlled Decryption: Authorized users can decrypt the data through the same EaaS platform using the appropriate credentials or keys.
- Key Management: The provider oversees the encryption keys—ensuring secure storage, rotation, and disposal.
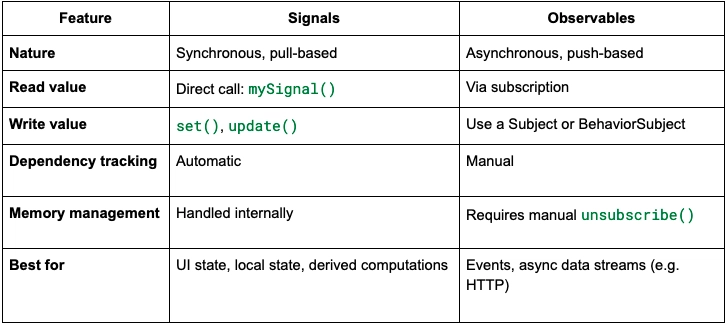
Key Variants of EaaS You Should Know
EaaS isn’t a one-size-fits-all solution. It includes multiple encryption strategies to meet varied security needs:
- Full Disk Encryption: Encrypts entire storage devices to prevent data theft if hardware is lost.
- File & Field-Level Encryption: Secures individual files or database fields like health records or financial details.
- End-to-End Encryption: Ensures data remains private throughout its entire journey.
- Homomorphic Encryption: Enables computations on encrypted data without revealing it.
- HTTPS & Network-Level Encryption: Secures web traffic and data moving across networks.
Why Businesses Are Adopting EaaS
Organizations are turning to EaaS for several compelling reasons:
- Reduced IT Complexity: No need to build or maintain custom encryption systems.
- Lower Operational Costs: Pay-as-you-go models eliminate the need for upfront investment.
- Compliance Made Easy: Helps meet regulatory requirements like HIPAA, GDPR, and PCI DSS.
- Remote Access Flexibility: Cloud delivery allows access to secure services from any location.
Limitations to Keep in Mind
Despite its advantages, EaaS isn’t without challenges:
- Performance Impact: Encryption processes can affect application speed.
- Vendor Dependency: Outages or security issues at the provider’s end could affect access.
- Key Management Risks: Poor key handling could lead to data exposure.
- User Workflow Disruption: Employees may face hurdles while working with encrypted data.
Conclusion
Encryption-as-a-Service has become an essential component of modern cybersecurity strategies. By delivering scalable, reliable, and compliant encryption without the overhead of managing infrastructure, EaaS empowers businesses to focus on growth while safeguarding their data. Though it requires thoughtful implementation, the security and peace of mind it offers make it a worthwhile investment in today’s data-centric world.









































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)







































































































.png?#)




.jpg?#)


















 (1).webp?#)













_Christophe_Coat_Alamy.jpg?#)





































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)