Decoding Residential Proxies: An In-Depth Exploration for the Informed Novice
In many professional settings, one inevitably encounters services purporting to offer resident proxies. Historically, I, like many, accepted these offerings without a thorough investigation—merely using them in the manner presented. However, a burgeoning curiosity compelled me to scrutinise the mechanics behind residential proxies and share the insights gleaned from this analytical journey. This narrative is not intended as prescriptive advice, but rather as an articulate dissection of a subject that has long hovered at the periphery of mainstream technical discourse. The Fundamentals of Proxy Servers: Masking Your Digital Identity At its core, a proxy server functions as an intermediary between your personal device and the internet at large. Its primary role is to obscure your genuine IP address, thereby altering how your digital footprint appears to the external world. Imagine, if you will, donning a pristine white overcoat amidst a snowy landscape—a straightforward metaphor for concealment. Yet, rather than rely solely on sartorial imagery, let us draw inspiration from the natural world’s adept masters of disguise. A Comparative Overview: Residential Proxies in the Realm of Digital Camouflage Within the broad categorisation of proxies, two principal types emerge: data centre proxies—often synonymous with server proxies—and residential proxies. An additional variant exists, commonly referred to as mobile proxies, which, for the purposes of this discussion, can be considered a specialized offshoot of residential proxies. To elucidate the differences, one might consider an analogy drawn from the animal kingdom: if the Malagasy flat-tailed gecko epitomises superior camouflage, then residential proxies assume this role, whereas server proxies resemble the less versatile Yemeni chameleon. In a similar vein, mobile proxies might be likened to the distinctive orchid mantis, each with its own set of attributes. Residential Proxies – The Gecko of Digital Stealth Server Proxies – The Chameleon of Data Centres Mobile Proxies – The Orchid Mantis of Connectivity For the remainder of this discussion, our focus will remain firmly on resident proxies. The critical distinction here is that resident proxies utilise IP addresses issued to actual households, in stark contrast to data centre proxies, which draw from a consolidated pool of addresses under a singular administrative domain. Visual comparisons typically underscore the enhanced obfuscation capabilities of resident proxies relative to their server-based counterparts. The Genesis of Residential IP Addresses For users to avail themselves of resident proxies, service providers must maintain a robust inventory—a reservoir of residential IP addresses ready for deployment. But whence do these addresses originate? Who, in essence, is the modern-day benefactor reallocating ordinary digital identifiers for a specialised purpose? To answer this, consider several mechanisms through which a typical user’s IP address may be incorporated into a proxy network: 1. Voluntary Engagement in Residential Proxy Networks Certain proxy services employ affiliate programmes whereby individuals are incentivised to share their IP addresses. Under such schemes, users opt into the programme, consent to its terms, and in return, receive a nominal financial recompense for lending their digital presence to the provider’s network. Although the process is transparent, it tends to attract fewer participants from regions with higher living standards. 2. Collaborative Agreements with Internet Service Providers Another prevalent strategy involves establishing contractual relationships with local or regional ISPs. These agreements grant proxy providers access to an existing cache of residential IP addresses. Often, the terms of service users agree to with their ISP may implicitly permit the sharing of their IP addresses with third parties. In such instances, while the bulk of the responsibility falls on the provider, a degree of ambiguity persists—perhaps unbeknownst to you, your IP is concurrently serving multiple roles in disparate networks. 3. Aggregation and Lease Arrangements A natural extension of the aforementioned approach is the direct negotiation between companies and ISPs. In these arrangements, a provider might either utilise the acquired addresses internally or lease them to external entities that are unable to secure such addresses through direct channels. This aggregation method serves to broaden the available supply in response to market demand. 4. Exploitation of Pre-Existing Hardware Infrastructure A further model posits the repurposing of already deployed home devices—routers, smart appliances, or other IoT equipment—to establish a distributed network of resident proxies. Here, the proxy provider bypasses traditional ISP channels by forging direct agreements with hardware suppliers. Although tangible examples of this approach are scant, t
In many professional settings, one inevitably encounters services purporting to offer resident proxies. Historically, I, like many, accepted these offerings without a thorough investigation—merely using them in the manner presented. However, a burgeoning curiosity compelled me to scrutinise the mechanics behind residential proxies and share the insights gleaned from this analytical journey. This narrative is not intended as prescriptive advice, but rather as an articulate dissection of a subject that has long hovered at the periphery of mainstream technical discourse.
The Fundamentals of Proxy Servers: Masking Your Digital Identity
At its core, a proxy server functions as an intermediary between your personal device and the internet at large. Its primary role is to obscure your genuine IP address, thereby altering how your digital footprint appears to the external world. Imagine, if you will, donning a pristine white overcoat amidst a snowy landscape—a straightforward metaphor for concealment. Yet, rather than rely solely on sartorial imagery, let us draw inspiration from the natural world’s adept masters of disguise.
A Comparative Overview: Residential Proxies in the Realm of Digital Camouflage
Within the broad categorisation of proxies, two principal types emerge: data centre proxies—often synonymous with server proxies—and residential proxies. An additional variant exists, commonly referred to as mobile proxies, which, for the purposes of this discussion, can be considered a specialized offshoot of residential proxies. To elucidate the differences, one might consider an analogy drawn from the animal kingdom: if the Malagasy flat-tailed gecko epitomises superior camouflage, then residential proxies assume this role, whereas server proxies resemble the less versatile Yemeni chameleon. In a similar vein, mobile proxies might be likened to the distinctive orchid mantis, each with its own set of attributes.
Residential Proxies – The Gecko of Digital Stealth
Server Proxies – The Chameleon of Data Centres
Mobile Proxies – The Orchid Mantis of Connectivity
For the remainder of this discussion, our focus will remain firmly on resident proxies. The critical distinction here is that resident proxies utilise IP addresses issued to actual households, in stark contrast to data centre proxies, which draw from a consolidated pool of addresses under a singular administrative domain. Visual comparisons typically underscore the enhanced obfuscation capabilities of resident proxies relative to their server-based counterparts.
The Genesis of Residential IP Addresses
For users to avail themselves of resident proxies, service providers must maintain a robust inventory—a reservoir of residential IP addresses ready for deployment. But whence do these addresses originate? Who, in essence, is the modern-day benefactor reallocating ordinary digital identifiers for a specialised purpose? To answer this, consider several mechanisms through which a typical user’s IP address may be incorporated into a proxy network:
1. Voluntary Engagement in Residential Proxy Networks
Certain proxy services employ affiliate programmes whereby individuals are incentivised to share their IP addresses. Under such schemes, users opt into the programme, consent to its terms, and in return, receive a nominal financial recompense for lending their digital presence to the provider’s network. Although the process is transparent, it tends to attract fewer participants from regions with higher living standards.
2. Collaborative Agreements with Internet Service Providers
Another prevalent strategy involves establishing contractual relationships with local or regional ISPs. These agreements grant proxy providers access to an existing cache of residential IP addresses. Often, the terms of service users agree to with their ISP may implicitly permit the sharing of their IP addresses with third parties. In such instances, while the bulk of the responsibility falls on the provider, a degree of ambiguity persists—perhaps unbeknownst to you, your IP is concurrently serving multiple roles in disparate networks.
3. Aggregation and Lease Arrangements
A natural extension of the aforementioned approach is the direct negotiation between companies and ISPs. In these arrangements, a provider might either utilise the acquired addresses internally or lease them to external entities that are unable to secure such addresses through direct channels. This aggregation method serves to broaden the available supply in response to market demand.
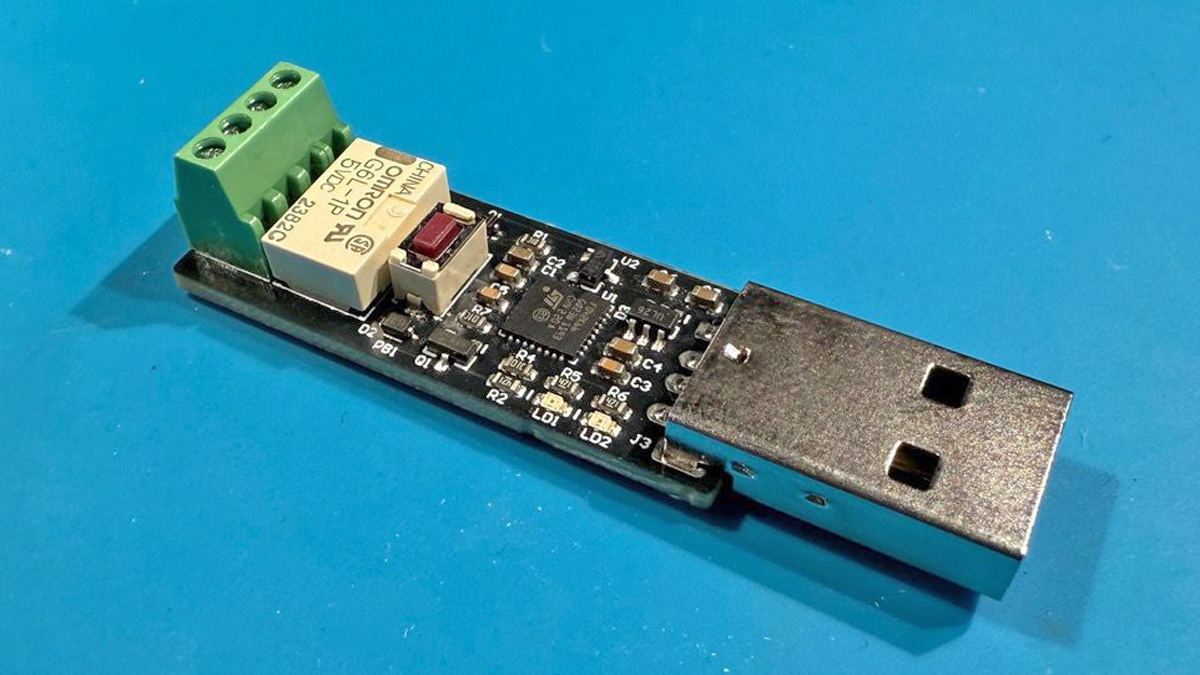
4. Exploitation of Pre-Existing Hardware Infrastructure
A further model posits the repurposing of already deployed home devices—routers, smart appliances, or other IoT equipment—to establish a distributed network of resident proxies. Here, the proxy provider bypasses traditional ISP channels by forging direct agreements with hardware suppliers. Although tangible examples of this approach are scant, there is no inherent reason to dismiss its potential viability.
5. Application-Driven Acquisition of User IPs
Perhaps the most scalable model in the current digital landscape is the utilisation of mobile applications. Many ostensibly free apps incorporate user agreements that permit the reallocation of their IP addresses for proxy purposes. Unlike the constraints imposed by regional ISP infrastructure, these applications can operate on a global scale, enabling users in metropolises such as New York or Prague to contribute to a far-reaching proxy network.
Decentralised VPN Services: A Parallel Model
It is also pertinent to acknowledge the existence of decentralised VPN services, which offer a conceptually similar alternative. These services create a network by interlinking real users, thereby allowing each participant to leverage the IP address of another. While many decentralised VPNs refrain from commercial resale of these addresses, exceptions do exist. Nevertheless, the inherent structure of such networks introduces distinct security considerations that merit careful evaluation.
The Underlying Mechanics: How Residential Proxies Operate
Having established that resident proxies derive from IP addresses assigned to genuine households, let us now explore their operational mechanics. Consider the analogy of dispatching a letter without divulging your home address. Rather than sending it directly, you entrust it to a reliable courier who, in turn, uses their own return address. The recipient, therefore, receives the letter with the courier’s details rather than your own.
Translated into technical terms, the process unfolds as follows:
Step One: Your computer initiates a request, which is directed to the proxy server—akin to handing over your letter.
Step Two: The proxy intercepts the request, substituting your actual IP address with its own identifier, before forwarding the request to the intended target.
Step Three: The target server processes the request and returns the response to the proxy server, rather than to you directly.
Step Four: The proxy server then relays the response back to your device, effectively preserving the anonymity of your original IP address.
This orchestrated sequence not only obscures your true digital identity but also facilitates circumvention of geographic or network-specific restrictions. Moreover, the utilisation of a genuine residential connection—as opposed to a uniform data centre—imbues the process with an additional layer of credibility and security.
Assessing the Trade-Offs: Drawbacks and Limitations of Residential Proxies
No technological solution is devoid of imperfections, and resident proxies are no exception. Several challenges persist:
Cost: The expense associated with resident proxies is typically higher than that of server-based alternatives.
Performance: The inherent variability of home network routing may result in reduced connection speeds.
Scalability: The finite nature of residential IP address pools may constrain operations on a large scale.
Despite these limitations, my extensive experience comparing resident and server proxies has led me to favour the former. When precision in regional search results and robust anonymity are paramount, resident proxies consistently deliver the requisite performance—albeit at a premium price. In essence, the added expense is often a small sacrifice for enhanced security and reliability.










































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)























































































































![[FREE EBOOKS] The Kubernetes Bible, The Ultimate Linux Shell Scripting Guide & Four More Best Selling Titles](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)



![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)






































































































.png?#)




.jpg?#)
































_Christophe_Coat_Alamy.jpg?#)





































































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)